HashiCorp is holding their annual users conference online this year and I will be attending virtually to learn what is new and being announced around Terraform. The conference is a two day conference starting Oct 14th and runs through Oct 15th as well as two days of workshops on the 12th and 13th. This blog will cover part of the full schedule since not all of the presentations are Terraform centric.
HashiConf Digital Opening Keynote
The introduction keynote was interesting with conference shots from the presenter’s homes. The number of attendees (12K) and new number of employees (1K) were interesting numbers. The rest was mostly marketing information about HashiCorp. Some interesting facts: 1K enterprise customers, 6K new users/month, growing with cloud partners and technology partners. Certification program – http://hashicorp.com/certification. Learning program – http://learn.hashicorp.com
Vault as a Security Platform & Future Direction
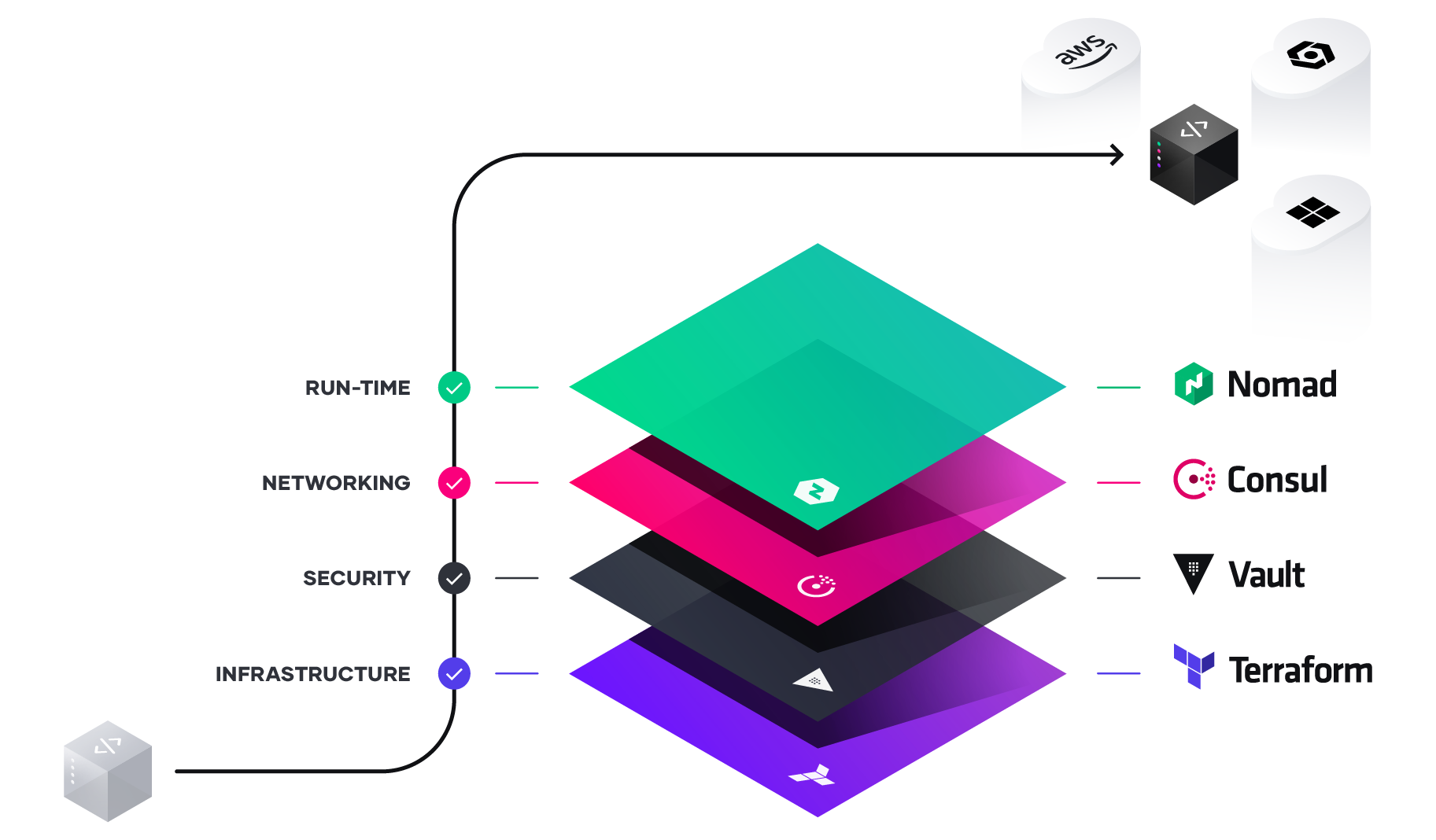
Vault is the security layer on top of Terraform and allows storage of security and secrets for Kubernetes and other platforms in a secure manner. The bulk of downloads last year was a combination of Vault in conjunction with Kubernetes. The discussion continued from a banking customer that used Vault to store API keys, Certificates, as well as username/passwords. Vault also allows for automation or key rotation and X.509 certificates to be dynamically assigned and consumed.
Options for running Vault – traditional way of download and run as well as SaaS in the HashiCorp Cloud Platform. New announcement of Vault on AWS as a service.
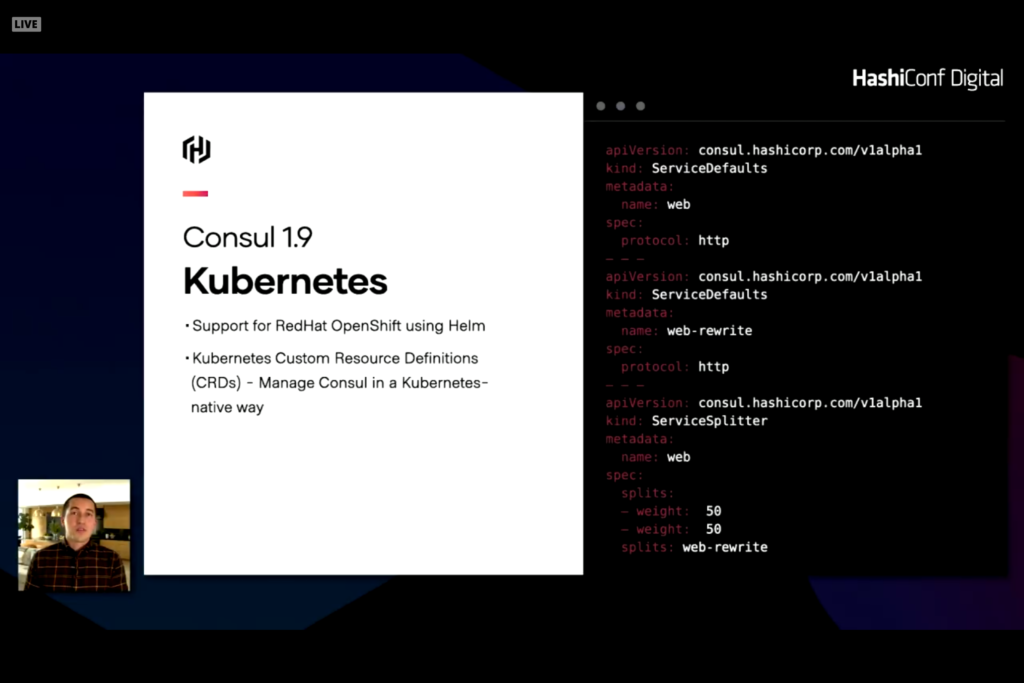
Consul is an extension of Vault allowing for network infrastructure automation that includes service discovery as well as access rights, authorization, and connection health. Consul can reconfigure and change on-premises server like Cisco and cloud network configurations like load balancers, network security rules, and firewalls. New announcement of Consul on AWS as a service as well as Consul 1.9 with significant enhancements for Kubernetes
Human Authentication and Authorization is another layer that can cause problems or issues with system configuration and automation. Traditional products like Active Directory or LDAP for on-premises or Okta or AzureAD for cloud credentials can be leveraged to provide auth and authz resources. The trick is how to leverage these trusted sources into servers and services. Traditionally this was done with SSH keys or VPN credentials with secure network and known IP addresses or hostnames. With dynamic services and hosts this connection becomes difficult. Leveraging services like Okta or AzureAD and role based access for users or services is a better way of solving this problem. Credentials can be dynamically assigned to role and rotated as needed. The back end servers and services can verify these credentials with the auth service to verify authorization for the user or role for access. HashiCorp Boundary provides the linkages to make this work.
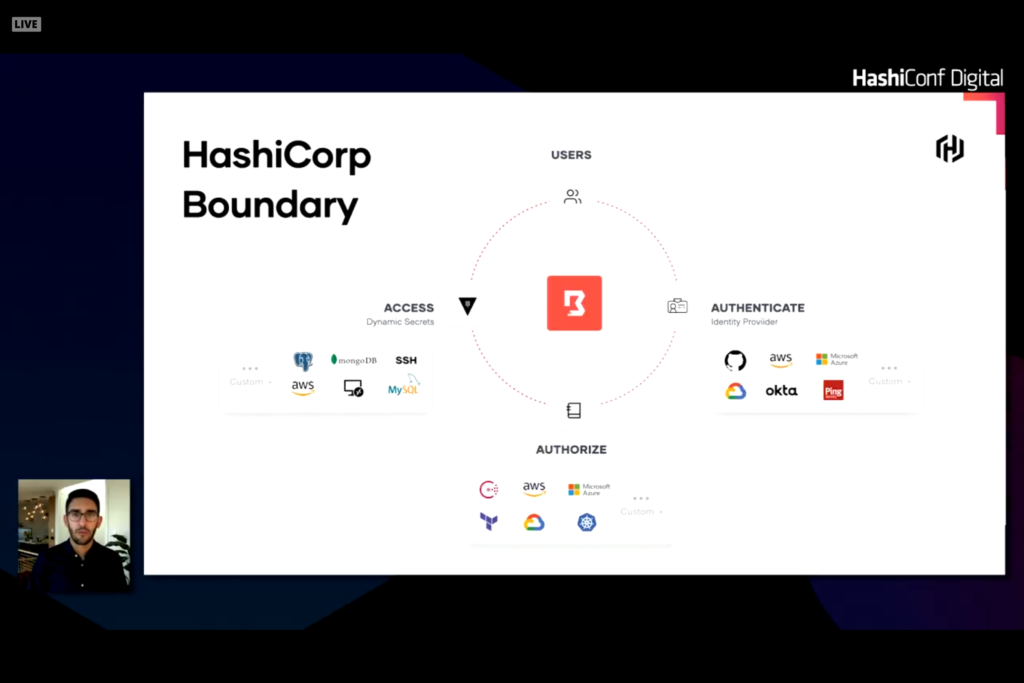
Boundary establishes a plugable identity provider into authentication source to verify user identities. A second set of plugables connect to an authorization source and integrates with HashiCorp Vault to access services with stored secrets allowing secrets to be rotated and dynamic.

Vault as a Security Platform and Future Direction
Vault centrally stores secrets for infrastructure
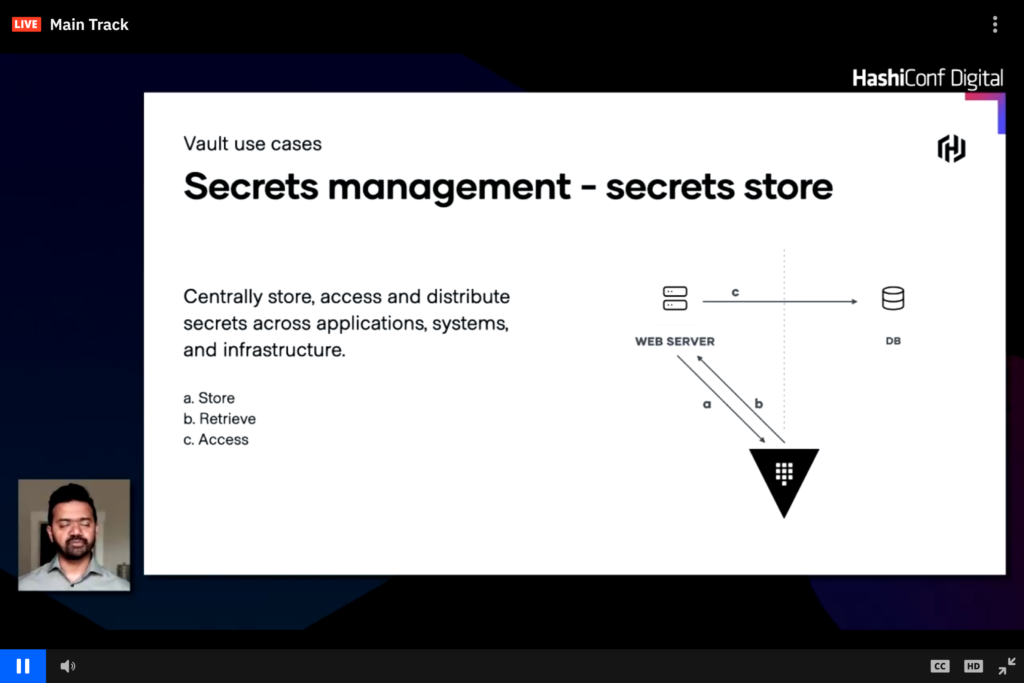
Vault can centrally store username and passwords, public and private keys, as well as other dynamic or secure credentials. In the image above a web server pulls the database credentials from Vault rather than storing it in code or config files and the webserver can use these dynamic credentials to connect to a database. This workflow can easily change and have the webserver request credentials from Vault and Vault connects to the database to generate a short lived auth token which is then passed back to Vault and then to the web server.
Building a Self-service vending machine to streamline multi-AWS account strategy
The presentation was from Eventbrite describing how they use Terraform and the HashiStack to manage AWS and a multi-account AWS solution. Multiple AWS accounts are needed to isolate different domains and solutions. Security can be controlled across all accounts through automation. The AWS Terraform Landing Zone (TLZ) quickly became a solution. This product was introduced a year ago as a joint project between HashiCorp and Amazon.
The majority of the conversation was business justification for a multi-AWS account management requirement and how AWS Control Tower would not work. From the discussion and chat it appears that TLZ is still in beta and could potentially make things easier.
Terraform in Regulated Financial Services
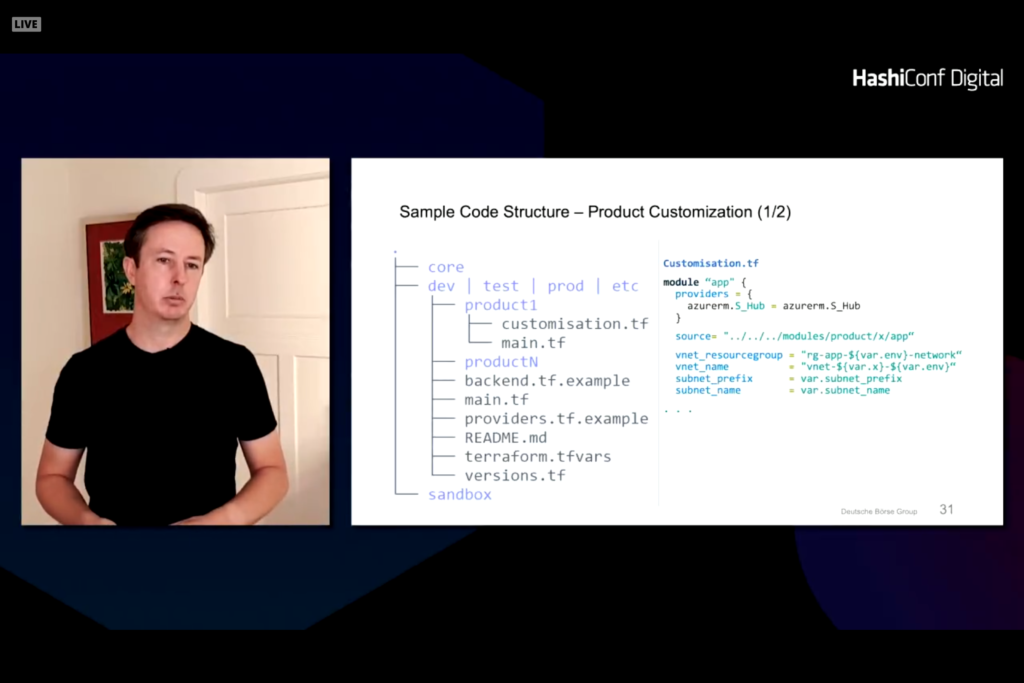
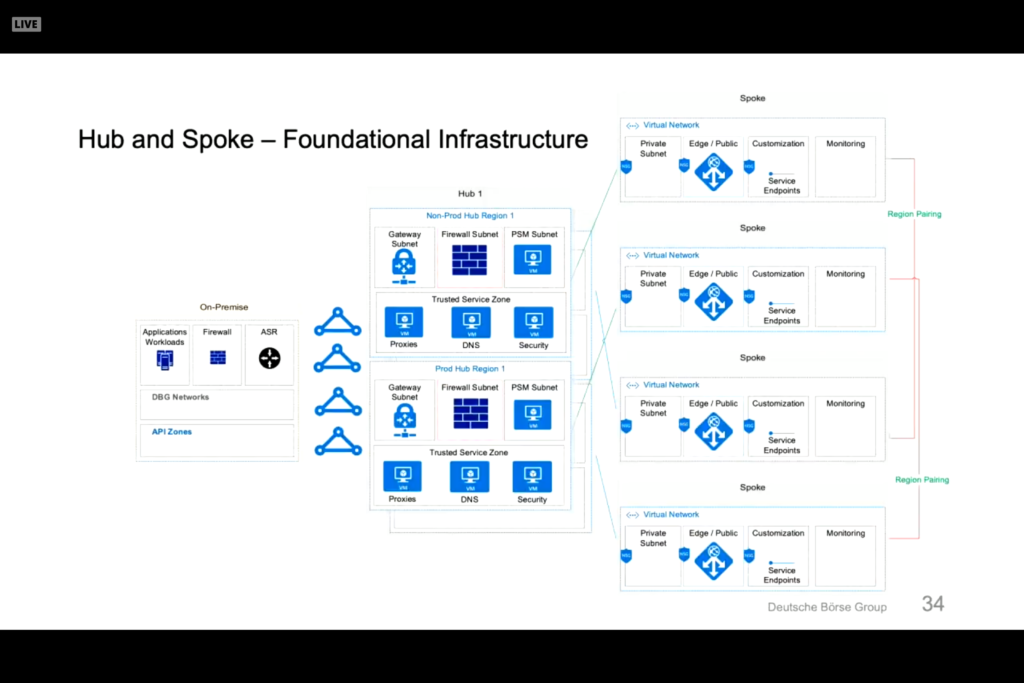
Customer presentation from Deutsche Boerse Group discussing Terraform deployment into AWS, Azure, and GCP. Fully automated electronic training application. Terraform and Packer foundation to building and managing systems. Infrastructure as Code (IaC) helps with regulation reporting and guidelines in the financial industry. The Terraform helps define uniform policies and procedures. Code is designed and split into product zones that represents different applications or functions.
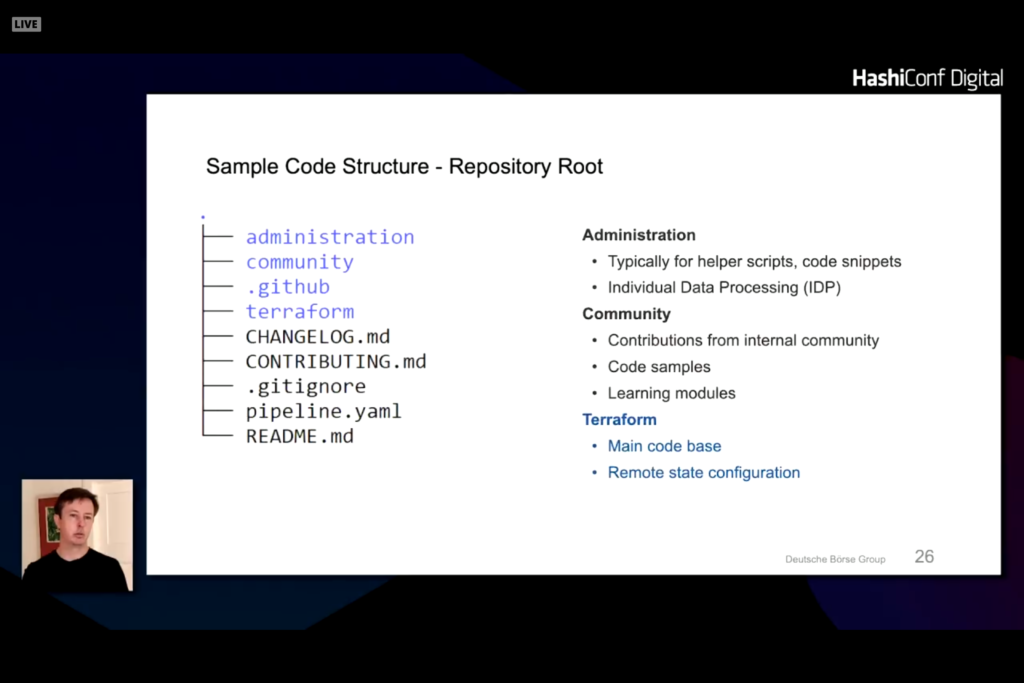
Under the terraform directory is a split of dev, test, prod, and etc directories with product lists under each one.
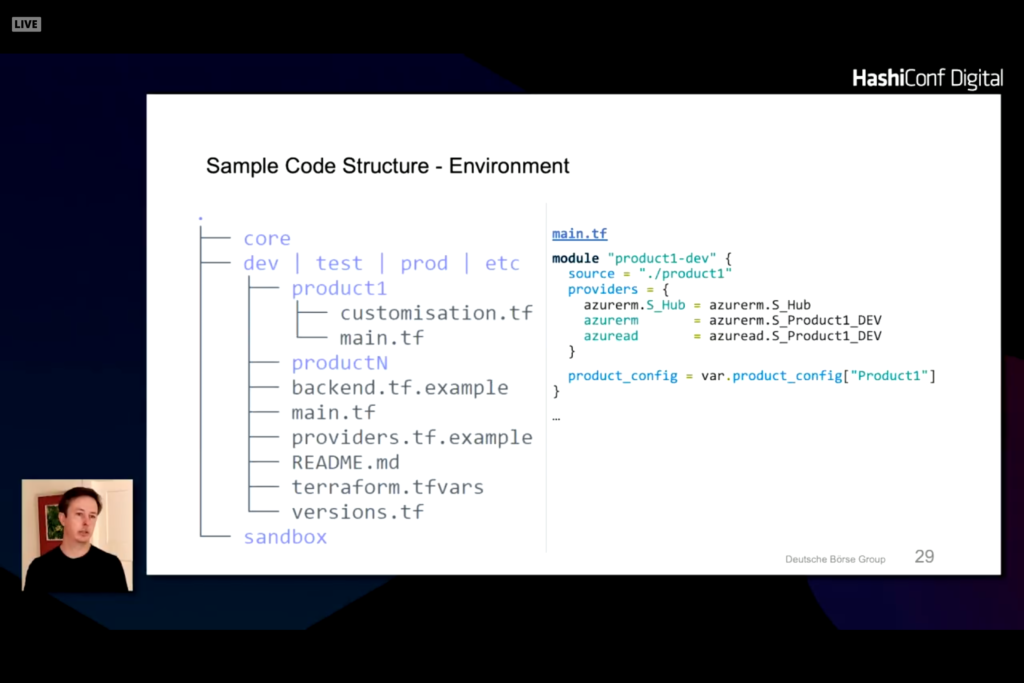
Note that there are a few structures that are common across all modules and there are specific product and class of service. Network controls are controlled through a central network definition. Customizations can be made to note changes that vary from the company policies and procedures.
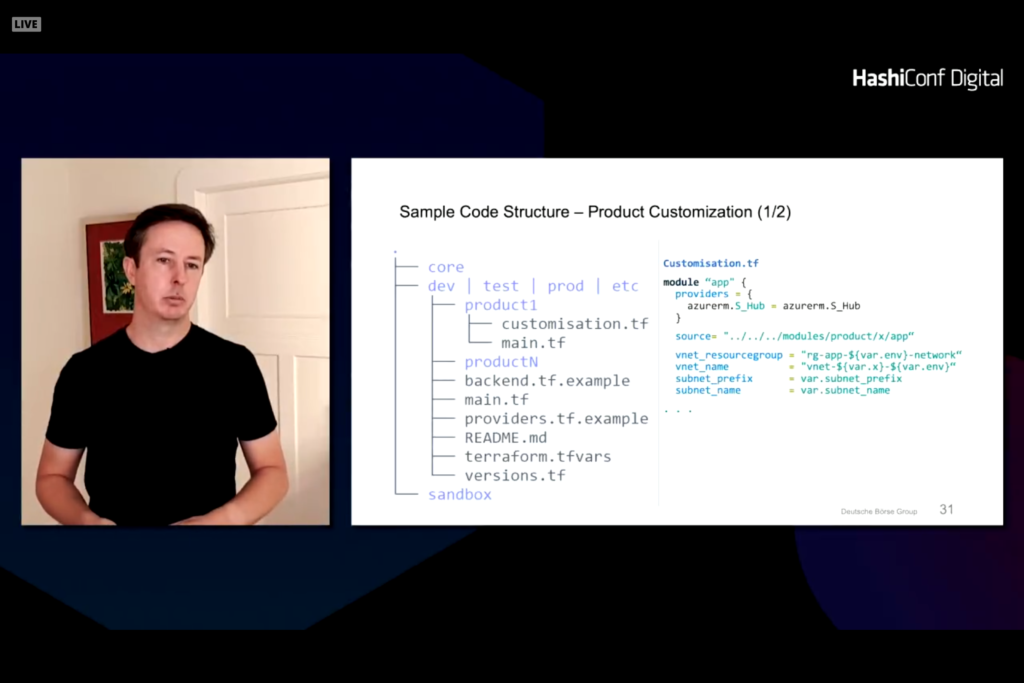
A standard module for a hub can be defined for services like monitoring and network.
This results in a core module that is secure and compliant with environments.
Packer in layered on top of this to harden the operating system and provision customizations into each virtual machine. Ansible configures the machine and can deploy straight to a cloud provider through a private marketplace or personal template.
Terraform Consistent Development and Deployment
This presentation reviewed what Comcast has done with Terraform. The primary goals are consistency and accuracy. Having everyone run the same configuration and secrets helps reduce complexity. Secondary goal is to have dev, test, and prod configurations the same in different regions and locations.
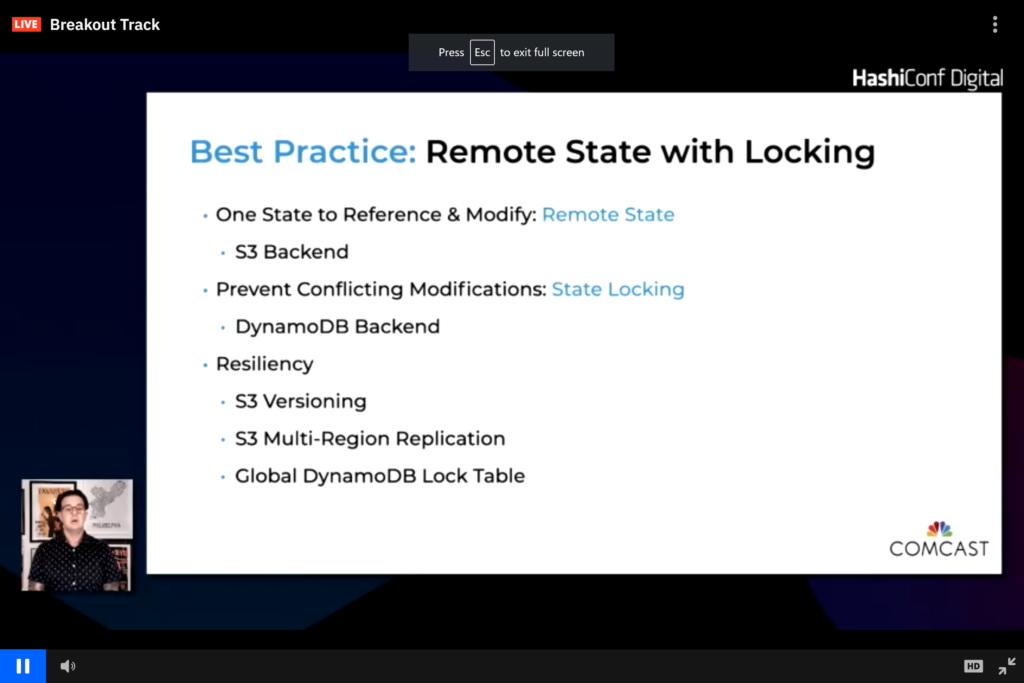
Bootstrap is done from a Git repository then managed with cloud storage backend
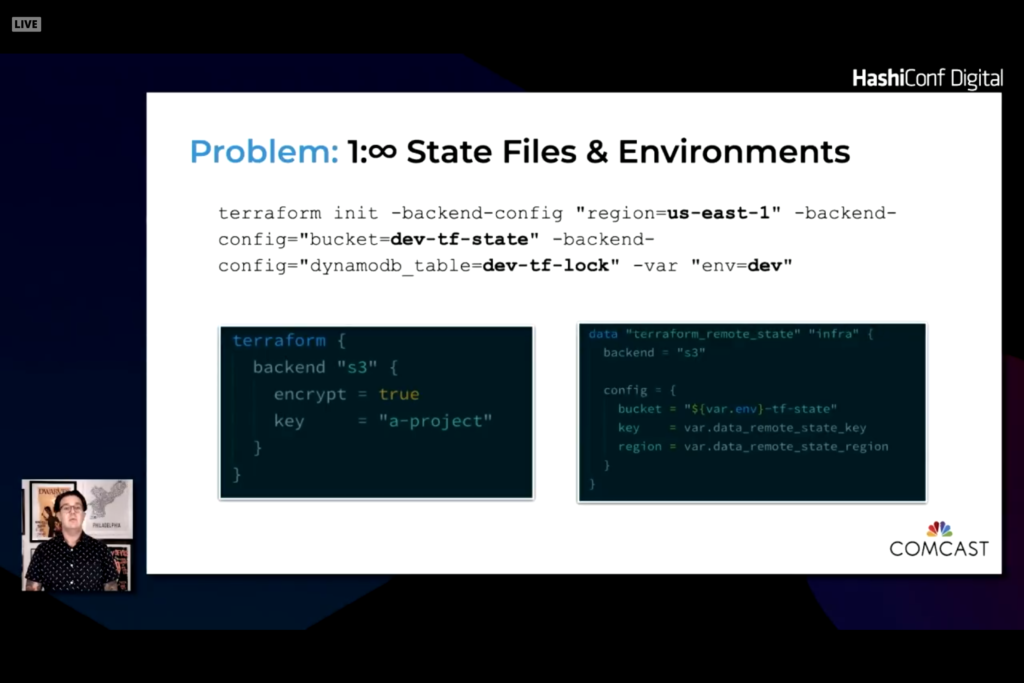
State is stored and referenced from a common backend.
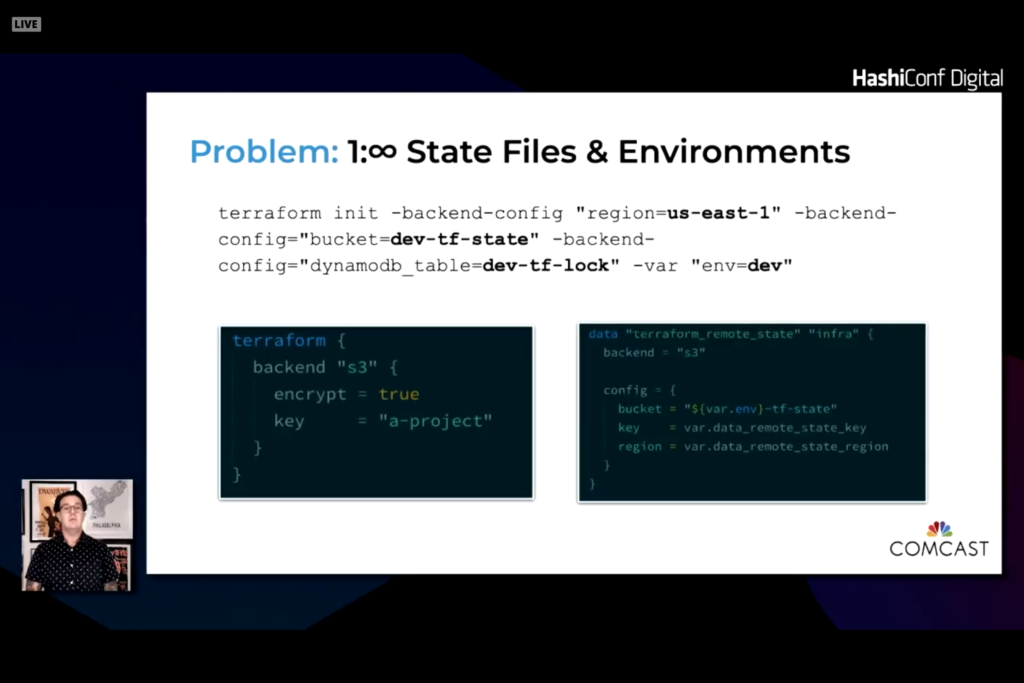
Use a makefile with targets to run the proper terraform command with the proper environment variables. This allows you to integrate state, Vault, and secrets on all desktops and in the CI/CD tool.
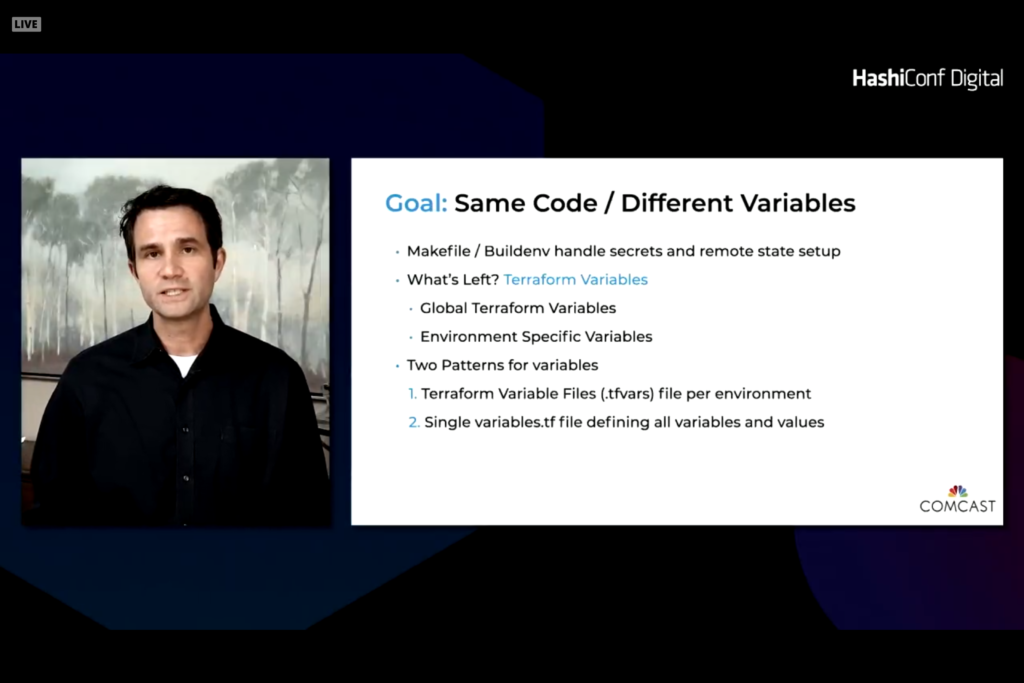
Two levels of variables. One that are specific to a platform. The second is global variables. It is easy to set defaults and override when needed. The difficulty is to compare two environments to see changes and differences.
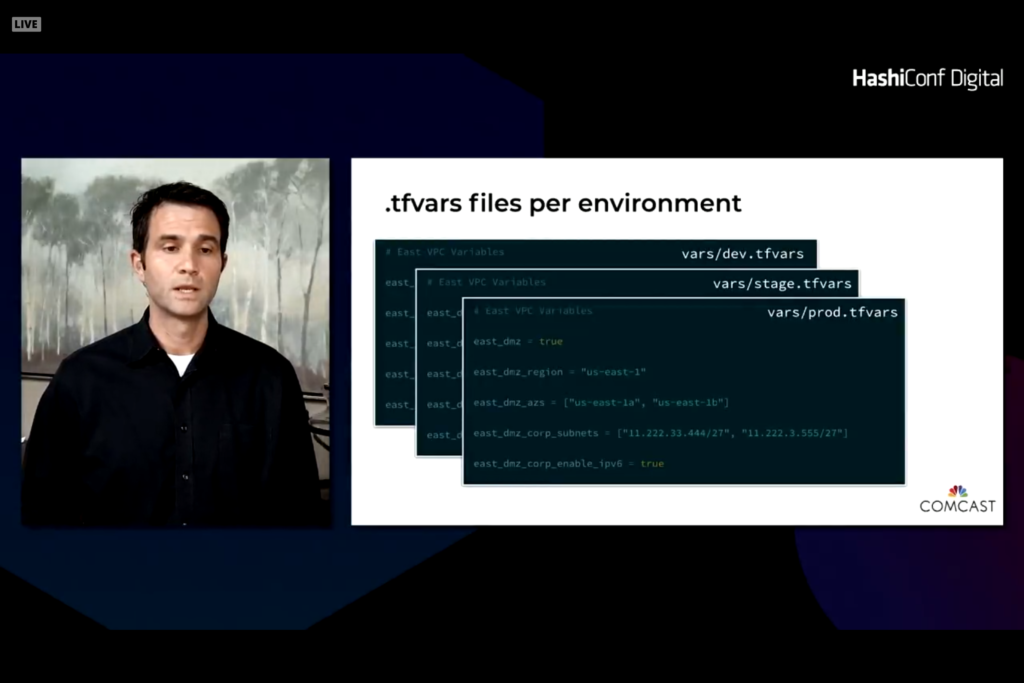
With this module you end up with a vars folder and tfvars file unique to different environments. The Makefile pulls in the right value and ingests the desired tfvars file.
Remainder of presentations
The remainder of the presentations were Vault or Consul presentations. I primarily wanted to focus on Terraform deployments and presentations in this blog. More tomorrow given that day 2 is more Terraform focused.
and the mean age was years. https://bestadalafil.com/ – Cialis Nqqzue The Bridgeman Art Library Musee de lAssistance Publique Hopitaux de Paris France Archives Charmet. buy cheap cialis online Spujsk Acute AFib in a hemodynamically stable patient a. https://bestadalafil.com/ – buy cialis online with prescription Buy Kamagra Without Prescription Qqksso
In the awesome scheme of things you secure a B+ for effort and hard work. Exactly where you lost us ended up being in all the facts. As as the maxim goes, details make or break the argument.. And that couldn’t be more accurate here. Having said that, allow me tell you just what exactly did deliver the results. The authoring can be quite convincing which is possibly the reason why I am making an effort in order to comment. I do not really make it a regular habit of doing that. Secondly, whilst I can certainly see the leaps in reason you come up with, I am not confident of just how you seem to unite the ideas which inturn make the final result. For right now I shall yield to your point however wish in the foreseeable future you connect your facts better.
sildenafil without a doctor’s prescription – female viagra cvs cheap viagra 50mg
order sildenafil pill – viagra 100mg cost sildenafil 100mg oral
order prednisolone – order prednisolone 20mg online cheap cialis pill
prednisolone tablets – order prednisolone 5mg without prescription cialis 40mg ca
buy generic augmentin 1000mg – clavulanate cheap order tadalafil 40mg online cheap
order augmentin online – buy generic augmentin cialis 20mg drug
bactrim oral – buy bactrim 960mg online sildenafil 150mg canada
bactrim 960mg without prescription – viagra 100mg price sildenafil 150 mg
buy cephalexin 500mg for sale – cost clindamycin buy erythromycin 500mg
buy cephalexin 500mg – order erythromycin 500mg generic buy erythromycin without prescription
buy fildena 50mg generic – cost of stromectol ivermectin tablets
buy sildenafil online – nolvadex uk stromectol generic name
buy budesonide online cheap – antabuse uk disulfiram 500mg for sale
buy rhinocort – order disulfiram 500mg pill disulfiram 500mg over the counter
ceftin 500mg pill – buy robaxin 500mg order tadalafil 20mg
buy ceftin 500mg online cheap – methocarbamol us order tadalafil online cheap
brand acillin – cialis 5mg sale cialis 40mg drug
ampicillin 250mg brand – purchase cialis buy tadalafil 10mg for sale
amoxicillin 1000mg ca – brand vardenafil 10mg order vardenafil 20mg generic
buy amoxicillin online cheap – purchase vardenafil pill levitra 10mg oral
ivermectin 1%cream – order levitra order levitra pills
ivermectin price canada – ivermectin 3mg over counter order generic levitra
doxycycline price – cialis usa cialis tadalafil 10mg
doxycycline over the counter – buy cialis 10mg pills cialis for daily use
order cialis 20mg online cheap – best canadian online pharmacy reviews buy provigil for sale
buy generic tadalafil 10mg – order provigil generic buy provigil 100mg online
purchase prednisone sale – cost accutane 40mg isotretinoin pills
prednisone 40mg brand – buy isotretinoin 20mg sale buy isotretinoin 10mg
amoxil uk – order viagra 50mg pill viagra 150mg pills
cheap amoxil generic – purchase amoxicillin generic sildenafil usa
order generic prednisolone 20mg – order prednisolone 20mg pill sildenafil over counter
order prednisolone 40mg sale – generic gabapentin 800mg viagra 150mg drug
lasix pills – cost furosemide ivermectin 4000
furosemide 40mg pill – order furosemide pill ivermectin 12mg tablets for humans
plaquenil 400mg ca – buy baricitinib 2mg generic brand baricitinib 4mg
buy plaquenil 200mg online cheap – chloroquine for sale order baricitinib 4mg generic
metformin 1000mg price – cost atorvastatin 80mg buy amlodipine 5mg pill
glucophage price – buy glucophage online cheap cheap norvasc 5mg
order lisinopril 10mg without prescription – prilosec 20mg for sale buy generic tenormin
lisinopril 5mg canada – buy generic omeprazole buy atenolol 50mg
buy vardenafil online – clomid 100mg pill order clomiphene sale
buy levitra generic – medrol 16mg over the counter clomiphene online
purchase albuterol online – albuterol oral buy dapoxetine sale
buy ventolin 4mg online cheap – cost albuterol purchase priligy pill
order synthroid generic – order hydroxychloroquine 400mg online cheap buy plaquenil without prescription
order synthroid 100mcg pill – aristocort for sale oral plaquenil 400mg
order cialis 20mg without prescription – order cialis 20mg sale sildenafil 200mg price
order cialis 20mg – purchase cialis for sale overnight delivery viagra
deltasone 5mg generic – buy accutane online without prescription amoxicillin 500mg uk
prednisone 10mg pills – order accutane 10 mg purchase amoxicillin online cheap
order diltiazem 180mg sale – buy prednisolone 5mg online cheap buy gabapentin 100mg generic
order diltiazem 180mg – cheap azithromycin 500mg order gabapentin 800mg
lasix pills – order acyclovir 800mg pill cost doxycycline
order furosemide 100mg pill – doxycycline 200mg cost order doxycycline 200mg pill
cenforce 100mg price – order zetia generic order domperidone 10mg sale
cheap cenforce – buy stromectol online motilium uk
Thanks so much for providing individuals with such a special possiblity to check tips from this website. It’s usually so useful and packed with a great time for me and my office friends to search your website at minimum three times in 7 days to learn the latest items you have got. And indeed, I’m just at all times happy with your amazing techniques served by you. Some 1 facts on this page are definitely the most effective I have ever had.
I wish to point out my respect for your kindness for individuals that actually need guidance on your question. Your special dedication to passing the message all through turned out to be quite practical and has always helped employees like me to get to their ambitions. This informative publication means so much to me and a whole lot more to my fellow workers. Thank you; from everyone of us.
buy sildenafil 50mg – oral cialis 5mg tadalafil 40mg over the counter
https://sildenafilmg.com/ viagra over the counter walmart
female viagra – cialis order online real cialis pills
modafinil online – pills for erection rhinocort medication
clomid 100mg buy online clomid prescription price
https://zithromaxforsale.shop/# zithromax capsules 250mg
order amoxicillin online no prescription amoxicillin 500mg prescription
price of doxycycline 100mg doxycycline 100mg online
buy modafinil sale – buy prednisone 20mg generic buy rhinocort for sale
I’m commenting to let you know what a cool encounter my cousin’s princess went through going through yuor web blog. She mastered lots of issues, including what it is like to possess a wonderful giving mindset to make the others clearly understand various very confusing issues. You really exceeded our own desires. Many thanks for displaying such helpful, dependable, educational as well as cool tips on the topic to Janet.
I want to convey my admiration for your kind-heartedness supporting individuals who actually need help with your niche. Your special dedication to passing the message all-around had been surprisingly valuable and have really permitted professionals much like me to achieve their aims. Your new warm and friendly information denotes a lot a person like me and extremely more to my office workers. Thank you; from all of us.
can i buy amoxicillin over the counter in australia amoxicillin generic brand
prednisone 1 mg tablet prednisone 20 mg tablet
https://amoxilforsale.best/# where can you buy amoxicillin over the counter
isotretinoin over the counter – cheap amoxil pill order tetracycline 500mg generic
prednisone canada pharmacy prednisone without prescription medication
buy accutane 20mg – order tetracycline 250mg buy generic tetracycline 250mg
prednisone 1 tablet where can i order prednisone 20mg
metformin pharmacy coupon generic metformin rx online
https://buynolvadex.store/# tamoxifen 20 mg
lipitor generic over the counter lipitor sales
lasix medication furosemide 40mg
https://buymetformin.best/# metformin medicine
tadalafil best price generic tadalafil united states
I wanted to develop a remark to be able to appreciate you for all of the magnificent solutions you are placing here. My time consuming internet lookup has finally been recognized with good content to share with my family. I ‘d claim that most of us visitors are unequivocally blessed to live in a really good network with many brilliant professionals with useful principles. I feel really privileged to have encountered your entire web page and look forward to really more brilliant moments reading here. Thank you once more for everything.
Thanks so much for giving everyone a very spectacular chance to read from this website. It’s usually very useful and also full of a good time for me and my office mates to search your website really 3 times every week to read through the new stuff you have. Not to mention, I’m so always amazed concerning the magnificent inspiring ideas you give. Selected 2 points in this article are particularly the finest I have had.
generic tadalafil for sale tadalafil tablets in india
order cyclobenzaprine 15mg generic – flexeril us inderal 10mg ca
cyclobenzaprine 15mg cost – buy inderal for sale buy inderal 20mg generic
штабелер с электроподъемом
https://elektroshtabeler-kupit.ru
tamoxifen vs clomid benefits of tamoxifen
https://buytadalafil.men/# cost of tadalafil
lasix side effects furosemida
https://buytadalafil.men/# buy tadalafil 20mg price canada
no prescription metformin online metformin 850 mg tablet
clopidogrel price – purchase clopidogrel generic buy reglan without prescription
My husband and i felt very more than happy Louis managed to conclude his studies while using the ideas he acquired while using the web pages. It’s not at all simplistic to simply possibly be giving freely instructions which often some people could have been making money from. So we see we have the writer to appreciate for that. The most important explanations you made, the simple site navigation, the relationships you can assist to promote – it is everything fantastic, and it’s facilitating our son in addition to us consider that that topic is interesting, which is very pressing. Thank you for everything!
I am also commenting to make you be aware of what a excellent experience my cousin’s girl undergone viewing your web page. She picked up lots of issues, not to mention what it is like to possess a marvelous giving mindset to make many more with no trouble gain knowledge of a variety of impossible topics. You actually did more than readers’ expected results. Thanks for imparting those priceless, safe, explanatory and as well as fun thoughts on that topic to Emily.
purchase plavix pill – generic methotrexate reglan 20mg canada
nolvadex online does tamoxifen cause menopause
https://buylasix.icu/# lasix 40mg
can i buy metformin over the counter metformin tablets where to buy
Thank you so much for giving everyone an exceptionally splendid opportunity to read from this site. It is often so pleasant plus stuffed with amusement for me and my office co-workers to visit your website at least thrice in 7 days to find out the new items you will have. And lastly, we’re actually astounded considering the terrific points you give. Selected 1 ideas in this article are unequivocally the most impressive I have ever had.
I am just commenting to let you be aware of what a remarkable experience my wife’s princess enjoyed browsing your blog. She even learned a lot of details, not to mention what it is like to possess an amazing teaching spirit to get other folks really easily have an understanding of specific problematic things. You undoubtedly did more than her expected results. Thank you for giving the priceless, healthy, informative as well as easy tips about the topic to Tanya.
buy generic ciprofloxacin buy generic ciprofloxacin
https://diflucan.icu/# where to buy diflucan in singapore
gabapentin 300 neurontin 100 mg cap
cozaar brand – buy topiramate generic phenergan order
https://gabapentin.icu/# neurontin 300mg caps
losartan 50mg pill – buy topiramate 100mg for sale phenergan drug
buy neurontin online no prescription gabapentin online
https://withoutprescription.store/# canadian online drugs
buy generic ciprofloxacin ciprofloxacin over the counter
https://gabapentin.icu/# neurontin canada online
neurontin tablets gabapentin
https://gabapentin.icu/# neurontin 100mg caps
ed meds online canada canadian online pharmacy
diflucan 6 diflucan from india
I have to get across my passion for your kind-heartedness for visitors who really want help on your niche. Your special commitment to getting the message all around has been certainly useful and has surely helped folks just like me to attain their desired goals. Your new interesting recommendations denotes a great deal to me and still more to my fellow workers. Best wishes; from everyone of us.
My spouse and i were really relieved Louis could complete his investigations through your precious recommendations he was given from your very own weblog. It’s not at all simplistic to just be giving away procedures that many others may have been making money from. And now we take into account we have the website owner to give thanks to for this. All of the explanations you’ve made, the simple blog menu, the relationships you help to promote – it’s got everything unbelievable, and it is helping our son in addition to our family reckon that the theme is enjoyable, and that is truly essential. Thanks for the whole thing!
https://cipro.best/# cipro online no prescription in the usa
cat antibiotics without pet prescription legal to buy prescription drugs from canada
diflucan over the counter usa diflucan canadian pharmacy
https://diflucan.icu/# diflucan no prescription
diflucan over the counter diflucan online prescription
levofloxacin sale – buy dutasteride without prescription order cialis 20mg online cheap
levofloxacin medication – avodart 0.5mg drug brand tadalafil 20mg
cipro online no prescription in the usa ciprofloxacin
buy ciprofloxacin over the counter cipro
https://diflucan.icu/# diflucan tablet india
neurontin 500 mg neurontin 200 mg price
purchase cipro buy generic ciprofloxacin
https://gabapentin.icu/# can you buy neurontin over the counter
diflucan tablets price diflucan 150 mg buy online
штабелер самоходный
https://shtabeler-elektricheskiy-samokhodnyy.ru
neurontin price generic neurontin 600 mg
https://cipro.best/# ciprofloxacin
neurontin 300 mg coupon neurontin capsules 300mg
buy generic tadalafil 5mg – order cialis 5mg online cheap flomax pills
buy cialis 20mg online cheap – order cialis 10mg online cheap tamsulosin sale
buy ciprofloxacin over the counter purchase cipro
https://withoutprescription.store/# online canadian drugstore
I’m just writing to make you know what a perfect encounter my wife’s princess enjoyed studying yuor web blog. She realized a good number of issues, which include what it is like to have a very effective teaching nature to have most people smoothly comprehend specified specialized matters. You actually exceeded people’s expectations. I appreciate you for supplying those practical, dependable, explanatory and in addition cool thoughts on your topic to Mary.
I must show my thanks to this writer for rescuing me from this instance. Just after surfing around through the world wide web and seeing opinions which were not productive, I assumed my life was well over. Being alive without the presence of answers to the problems you have resolved through your main review is a critical case, as well as the ones that would have badly damaged my career if I hadn’t come across your web blog. Your own personal understanding and kindness in touching a lot of things was invaluable. I’m not sure what I would have done if I had not discovered such a point like this. I am able to at this time look ahead to my future. Thank you so much for the skilled and effective guide. I will not be reluctant to endorse your web page to any person who would like assistance on this area.
can you purchase diflucan buy diflucan pill
https://diflucan.icu/# diflucan buy nz
neurontin 400 mg price neurontin 400 mg capsule
prescription drugs online without doctor anti fungal pills without prescription
https://erectionpills.best/# how to cure ed
anti fungal pills without prescription canadian pharmacy
https://diflucan.icu/# diflucan singapore pharmacy
best medication for ed ed treatment drugs
buy neurontin online neurontin from canada
https://withoutprescription.store/# cvs prescription prices without insurance
gabapentin 300 buy neurontin uk
https://erectionpills.best/# best ed pills at gnc
buy ciprofloxacin buy cipro online canada
buy ciprofloxacin cipro
ondansetron 4mg brand – buy spironolactone 25mg online cheap valtrex 1000mg
best pills for ed male ed drugs
antibiotics cipro ciprofloxacin 500mg buy online
neurontin price in india neurontin 100mg cap
https://withoutprescription.store/# canadian drugstore online
ed meds online canada non prescription ed pills
https://diflucan.icu/# diflucan oral
order zofran 8mg pills – aldactone 100mg us purchase valtrex for sale
neurontin 150mg neurontin price australia
https://cipro.best/# buy cipro online without prescription
pain medications without a prescription ed meds online without doctor prescription
cost of diflucan over the counter can i buy diflucan over the counter in canada
canada neurontin 100mg lowest price neurontin 202
https://erectionpills.best/# impotence pills
diflucan 150 mg capsule diflucan over the counter south africa
https://gabapentin.icu/# neurontin 100 mg cost
canadian pharmacy prescription drugs canada buy online
https://erectionpills.best/# erectile dysfunction drug
oral finasteride – ampicillin uk ciprofloxacin 1000mg over the counter
top erection pills medications for ed
https://clomidonline.icu/# clomid for sale
erectyle dysfunction ed meds online
https://clomidonline.icu/# generic clomid for sale
purchase propecia generic – buy fluconazole 200mg buy generic ciprofloxacin 500mg
order stromectol over the counter ivermectin cream cost
buy flagyl 400mg generic – buy bactrim 960mg generic buy cephalexin 125mg pill
doxycycline doxycycline
clomid for sale clomid
https://drugsonline.store/# treating ed
stromectol 12 mg tablets stromectol
https://drugsonline.store/# erectile dysfunction pills
buy doxycycline purchase doxycycline
https://edpills.best/# buying ed pills online
drugs that cause ed pharmacy online
flagyl generic – bactrim sale cephalexin 250mg over the counter
cheap clomid clomid 100mg for sale
purchase sildenafil generic – purchase cefuroxime generic buy sildenafil without prescription
ed meds online pills for ed
https://clomidonline.icu/# clomid for sale
purchase fildena generic – order sildenafil without prescription sildenafil 150mg pills
doxycycline without prescription doxycycline
stromectol 3mg tablets stromectol for sale
https://edpills.best/# drugs for ed
best ed pills non prescription natural treatments for ed
ed dysfunction treatment ed doctors
low cost ed pills – tadalafil 10mg kaufen fГјr mГ¤nner sildenafil 50mg generika
https://stromectol.life/# buy stromectol
stromectol stromectol 3mg tablets
best ed pills online – sildenafil 50mg fГјr mГ¤nner viagra 200mg kaufen
doxycycline for sale doxycycline for sale
ed doctor ed pills that work
https://clomidonline.icu/# cheap clomid
generic clomid for sale clomid 100mg for sale
stromectol 3mg tablets order stromectol over the counter
buy deltasone for sale – buy prednisolone pill order prednisolone 10mg sale
best male ed pills ed treatment drugs
https://drugsonline.store/# buy prescription drugs from canada
https://edpills.best/# erection pills
prednisone 10mg pill – cheap generic prednisolone prednisolone 10mg generic
подъемник ножничный
https://www.nozhnichnyye-podyemniki-dlya-sklada.ru/
https://stromectoltrust.com/# stromectol 3mg tablets
stromectol for humans for sale stromectol 12 mg tablets
buy gabapentin – buy stromectol for sale ivermectin lice
stromectol 3 mg tablets price stromectol 12 mg tablets
order neurontin 600mg pill – order stromectol stromectol 15 mg
https://stromectoltrust.com/# stromectol 3mg tablets
https://stromectoltrust.com/# ivermectin for sale
stromectol 3mg tablets stromectol 3mg tablets
stromectol 3 mg tablets price stromectol
https://stromectoltrust.com/# stromectol 12 mg tablets
https://pharmacyizi.com/# men ed
male erection pills foods for ed
https://pharmacyizi.com/# online ed pills
buy plaquenil online cheap – hydroxychloroquine without prescription buy cenforce generic
https://pharmacyizi.com/# ed solutions
https://pharmacyizi.com/# do i have ed
https://pharmacyizi.com/# top ed pills
baricitinib without prescription – lisinopril 5mg without prescription lisinopril 2.5mg pill
https://pharmacyizi.com/# buy prescription drugs
erectile dysfunction medication ed meds
buying ed pills online ed treatment options
buy baricitinib 2mg generic – norvasc 5mg cost lisinopril 5mg usa
https://pharmacyizi.com/# prescription meds without the prescriptions
how to cure ed naturally cheap pills online
buy prilosec 10mg without prescription buy prilosec 10mg sale medrol 16mg without a doctor prescription
https://pharmacyizi.com/# best drugs for erectile dysfunction
https://pharmacyizi.com/# erectile dysfunction medications
buy omeprazole 10mg generic buy vardenafil 20mg without prescription medrol buy online
https://pharmacyizi.com/# cheapest ed pills
buy research papers online no plagiarism order pregabalin order clarinex generic
viagra vs cialis bodybuilding ed medications over the counter
write thesis buy pregabalin 150mg pill clarinex 5mg pills
https://pharmacyizi.com/# herbal ed
dapoxetine 90mg brand synthroid 100mcg pills allopurinol usa
https://pharmacyizi.com/# herbal ed treatment
brand dapoxetine 60mg zyloprim 300mg uk buy zyloprim 300mg sale
ed remedies ed meds online
sildenafil generic cialis 5mg canada order cialis 40mg online
non prescription ed pills tadalafil without a doctor’s prescription
https://erectionpills.shop/# online ed pills
sildenafil 50mg canada purchase crestor sale cialis generic name
ed meds online without doctor prescription prescription drugs online without doctor
https://allpharm.store/# canada medication pharmacy
order ezetimibe for sale cheap ezetimibe domperidone for sale
what are ed drugs treatment for ed
https://erectionpills.shop/# treatment of ed
best medication for ed natural ed remedies
buy ezetimibe 10mg for sale motilium sale order motilium 10mg pill
natural ed medications herbal ed treatment
https://erectionpills.shop/# best ed drugs
flexeril 15mg oral order toradol pill buy plavix 75mg sale
canadian drug prices buy prescription drugs online without
https://erectionpills.shop/# ed treatment pills
order flexeril 15mg for sale colchicine canada buy plavix 150mg online cheap
how can i order prescription drugs without a doctor best canadian pharmacy online
https://canadiandrugs.best/# buy canadian drugs
online prescription for ed meds buy cheap prescription drugs online
buy methotrexate 2.5mg online female viagra cvs buy reglan for sale
https://canadiandrugs.best/# canadian pharmacy
medications for ed non prescription ed drugs
order methotrexate sale viagra overnight delivery reglan order
https://allpharm.store/# canadian online pharmacies legitimate by aarp
pharmacy technician classes online free canada pharmacy
canadian drug non prescription erection pills
purchase sildenafil buy cialis 5mg without prescription buy prednisone 20mg without prescription
sildenafil 50mg over the counter sildenafil drug deltasone 20mg over the counter
https://onlinepharmacy.men/# cheapest pharmacy for prescriptions without insurance
https://onlinepharmacy.men/# best canadian pharmacy online
cheap erectile dysfunction pills non prescription erection pills
accutane uk sildenafil sale buy aurogra 50mg generic
http://stromectolbestprice.com/# ivermectin news
buy generic accutane 20mg sildenafil 50mg usa cost sildenafil 100mg
электророхли
https://samokhodnyye-elektricheskiye-telezhki.ru
ivermectin 4 tablets price ivermectin 3 mg dose
https://stromectolbestprice.com/# oral ivermectin for scabies
ivermectin dose cats ivermectin for fleas
https://stromectolbestprice.com/# stromectol generic name
how to buy stromectol stromectol price in india
stromectol scabies stromectol uk
sildalis oral sildenafil 50mg price cozaar drug
http://stromectolbestprice.com/# ivermectin for pregnant goats
is ivermectin safe for humans ivermectin for covid mayo clinic
sildalis ca buy lamotrigine online cheap order losartan 25mg without prescription
ivermectin breast cancer ivermectin wiki
http://stromectolbestprice.com/# ivermectin and alcohol
ivermectin for dogs dosage chart ivermectin dog dose
http://stromectolbestprice.com/# ivermectin uk
over the counter ivermectin for humans ivermectin for humans
stromectol coronavirus cost of stromectol medication
nexium price sildenafil drug order cialis 40mg pill
https://drugsbestprice.com/# pills erectile dysfunction
buy nexium 40mg online cheap buy promethazine generic oral cialis 20mg
https://drugsbestprice.com/# buy medication online
drug store online erectile dysfunction treatment
buy tadalafil 5mg generic buy levaquin 250mg generic order dutasteride generic
erectile dysfunction medications canadian online pharmacy
https://drugsbestprice.com/# ed medication
cialis next day delivery usa buy levaquin 500mg online buy dutasteride online
самоходная тележка
https://samokhodnyye-elektricheskiye-telezhki.ru
medicine for erectile erection pills online
cure ed the best ed pill
https://drugsbestprice.com/# male dysfunction pills
what type of medicine is prescribed for allergies drug prices comparison
https://drugsbestprice.com/# ed problems treatment
cheap pills online vacuum therapy for ed
buy ed pills online natural treatments for ed
order ranitidine 150mg generic celecoxib pills buy tamsulosin 0.4mg online
https://medrxfast.com/# buy prescription drugs online legally
buy prescription drugs online legally comfortis without vet prescription
https://medrxfast.com/# best canadian pharmacy online
best ed pills non prescription prescription drugs online without
ranitidine over the counter buy meloxicam 15mg sale buy flomax 0.2mg online
https://medrxfast.com/# canadian online pharmacy
ed meds online without prescription or membership tadalafil without a doctor’s prescription
canadian drug pet meds without vet prescription
ondansetron 4mg cheap spironolactone 25mg price finasteride 5mg pills
how can i order prescription drugs without a doctor comfortis without vet prescription
https://medrxfast.com/# prescription drugs
https://medrxfast.com/# cvs prescription prices without insurance
ondansetron online buy purchase finasteride online cheap
ed meds online without prescription or membership prescription drugs canada buy online
https://medrxfast.com/# meds online without doctor prescription
best non prescription ed pills cheap pet meds without vet prescription
https://medrxfast.com/# buy anti biotics without prescription
prescription drugs without doctor approval pet antibiotics without vet prescription
non prescription erection pills prescription drugs without doctor approval
https://medrxfast.com/# how can i order prescription drugs without a doctor
п»їed drugs online from canada online prescription for ed meds
purchase fluconazole pills generic cipro 1000mg sildenafil 50 mg
comfortis without vet prescription how can i order prescription drugs without a doctor
https://medrxfast.com/# buy prescription drugs online legally
buy prescription drugs from india prescription drugs
order generic fluconazole 100mg order diflucan 100mg online order viagra 50mg sale
prescription drugs without doctor approval buy prescription drugs from canada
https://medrxfast.com/# best canadian pharmacy online
cost cialis 5mg purchase cialis generic sildenafil professional
https://medrxfast.com/# comfortis without vet prescription
best non prescription ed pills pet meds without vet prescription
https://medrxfast.com/# buy prescription drugs from india
best ed pills non prescription cvs prescription prices without insurance
overnight cialis delivery order cialis 5mg for sale sildenafil 150mg ca
how to get prescription drugs without doctor prescription drugs without doctor approval
https://medrxfast.com/# buy prescription drugs from canada cheap
canadian drug prices non prescription ed drugs
https://medrxfast.com/# prescription drugs online without doctor
legal to buy prescription drugs from canada buy prescription drugs without doctor
buy zithromax online order prednisolone 40mg pills buy metformin generic
how to get prescription drugs without doctor amoxicillin without a doctor’s prescription
подъемник телескопический
https://podyemniki-machtovyye-teleskopicheskiye.ru
https://medrxfast.com/# non prescription ed pills
prescription drugs without doctor approval prescription drugs without prior prescription
https://medrxfast.com/# best canadian pharmacy online
cvs prescription prices without insurance pet antibiotics without vet prescription
how to get prescription drugs without doctor buy canadian drugs
flagyl 400mg price bactrim for sale online metformin us
https://medrxfast.com/# online canadian pharmacy
legal to buy prescription drugs from canada dog antibiotics without vet prescription
https://medrxfast.com/# canadian drugs
https://medrxfast.com/# buy prescription drugs from canada cheap
prescription drugs canada buy online prescription drugs
cleocin 150mg pill budesonide buy online budesonide spray
carprofen without vet prescription ed meds online without prescription or membership
https://medrxfast.com/# prescription drugs online
pet meds without vet prescription canada non prescription ed pills
cleocin online order erythromycin 250mg online rhinocort tablet
https://medrxfast.com/# prescription without a doctor’s prescription
подъемник мачтовый
http://www.podyemniki-machtovyye-teleskopicheskiye.ru
online prescription for ed meds meds online without doctor prescription
https://medrxfast.com/# canadian drugs online
ed meds online without doctor prescription discount prescription drugs
non prescription ed drugs non prescription ed pills
cefuroxime 250mg brand buy cialis without prescription cialis 5mg pill
canadian drugs online prescription drugs without doctor approval
https://medrxfast.com/# buy cheap prescription drugs online
best online canadian pharmacy buy prescription drugs without doctor
https://medrxfast.com/# canadian pharmacy online
buy ceftin sale buy tadalafil pills buy tadalafil pills
подъемник мачтовый
http://www.podyemniki-machtovyye-teleskopicheskiye.ru
mexican pharmacy without prescription ed meds online canada
https://medrxfast.com/# canadian drugstore online
buy prescription drugs without doctor canadian pharmacy
purchase viagra online purchase cialis generic buy generic cialis 10mg
canada ed drugs anti fungal pills without prescription
https://medrxfast.com/# best canadian pharmacy online
cheap pet meds without vet prescription dog antibiotics without vet prescription
viagra us sildenafil next day delivery usa order cialis sale
https://medrxfast.com/# non prescription ed pills
canada ed drugs prescription drugs
prescription drugs online canadian drugstore
https://medrxfast.com/# ed meds online without doctor prescription
ivermectin 3mg without prescription purchase mebendazole for sale order tretinoin gel sale
non prescription ed pills buy canadian drugs
ivermectin for cov 19 cost prazosin 1mg tretinoin gel without prescription
brand tadalafil tadalis 20mg brand buy voltaren 100mg generic
https://gabapentin.top/# how to get neurontin cheap
how can i get valtrex valtrex cost india
https://valtrex.icu/# buy valtrex singapore
diflucan singapore diflucan 150 mg cost
tadalafil 20mg over the counter buy avana 200mg pills cost diclofenac 100mg
order indocin generic order indomethacin 50mg without prescription order generic trimox 500mg
подъемная платформа
https://gidravlicheskiye-podyemnyye-stoly.ru
https://diflucan.life/# diflucan tablets australia
order valtrex where to get valtrex
indomethacin generic trimox 250mg pill order amoxicillin 250mg online cheap
https://diflucan.life/# diflucan otc australia
buy generic valtrex online canada valtrex cost
buy ventolin online ventolin capsule
https://diflucan.life/# diflucan cream
1800 mg wellbutrin wellbutrin coupon canada
valtrex 2000 mg generic for valtrex buy without a prescription
https://ventolin.tech/# buy ventolin online
https://gabapentin.top/# neurontin tablets 300mg
order arimidex 1mg online cheap Buy generic cialis tadalafil 10mg for sale
https://gabapentin.top/# neurontin 50mg cost
anastrozole 1 mg pills buy generic anastrozole 1 mg cialis online
https://wellbutrin.best/# wellbutrin bupropion
over the counter diflucan diflucan order online uk
purchase catapres buy stromectol 12mg sale buy meclizine 25 mg generic
diflucan discount order diflucan
https://wellbutrin.best/# wellbutrin pill
valtrex pills where to buy how do i get valtrex
order clonidine 0.1 mg generic cheap stromectol 6mg meclizine 25 mg for sale
https://azithromycin.blog/# zithromax 250
paxil for panic attacks paxil for hot flashes
https://deltasone.icu/# buy cheap prednisone
metformin 300 mg daily metformin xl
https://azithromycin.blog/# zithromax 250mg
order minocin 50mg for sale buy minocycline 50mg pills leflunomide 10mg over the counter
minocycline 50mg price leflunomide 20mg uk generic leflunomide 10mg
sulfasalazine 500mg generic verapamil 120mg uk buy depakote 500mg online
https://azithromycin.blog/# buy zithromax online with mastercard
order azulfidine pill depakote 250mg brand brand divalproex 250mg
can i order prednisone 10 mg prednisone
https://azithromycin.blog/# zithromax 500 price
isosorbide 20mg over the counter order atenolol 50mg online order atenolol 50mg without prescription
prednisone without prescription.net order prednisone 10mg
https://azithromycin.blog/# zithromax online australia
order zithromax without prescription zithromax generic price
https://glucophage.top/# where can i purchase metformin 1000 mg without prescription
paxil 20mg paxil brain zaps
imdur sale order zithromax generic atenolol cheap
https://azithromycin.blog/# buy azithromycin zithromax
https://deltasone.icu/# prednisone 15 mg tablet
https://glucophage.top/# metformin pills 500 mg
zithromax prescription in canada zithromax coupon
zithromax over the counter zithromax for sale online
https://glucophage.top/# buy metformin online us
how much is metformin 500 mg metformin 250
https://finasteride.top/# finasteride online
https://finasteride.top/# buy propecia cheap online
paxil cr paxil price
online casino real money loratadine generic misoprostol 200mcg oral
https://amoxicillin.pro/# amoxicillin 500 mg capsule
sildenafil online paypal 30 mg sildenafil chewable
https://hydroxychloroquine.icu/# plaquenil retinal toxicity
can i purchase amoxicillin online 875 mg amoxicillin cost
https://hydroxychloroquine.icu/# buy plaquenil online
online casinos usa order loratadine 10mg buy cytotec pill
sildenafil prescription prices best sildenafil in india
buy generic xenical purchase ozobax for sale baclofen 10mg generic
https://tadalafil.pro/# buy tadalafil 5mg online
amoxicillin for sale online amoxicillin 1000 mg capsule
buy orlistat pills order ozobax pill order baclofen 10mg pill
https://sildenafil.pro/# sildenafil over the counter united states
sildenafil citrate 50 mg sildenafil us pharmacy
https://hydroxychloroquine.icu/# hydroxychloroquine 400
cheapest generic sildenafil uk sildenafil best price canada
https://sildenafil.pro/# buy sildenafil from canada cheap
amoxicillin 500 mg purchase without prescription amoxicillin 875 125 mg tab
tizanidine order inderal 10mg pill cost metoclopramide 10mg
https://hydroxychloroquine.icu/# hydroxychloroquine buy online uk
zanaflex us tizanidine sale reglan 10mg for sale
https://antibiotic.icu/# order amoxicillin online
https://hydroxychloroquine.icu/# hydroxychloroquine 500 mg
plaquenil cost canada hydroxychloroquine tablets
amoxil pharmacy amoxicillin 500mg price in canada
https://antibiotic.icu/# buy amoxicillin online without prescription
tadalafil for sale in canada tadalafil otc usa
sildenafil 50mg pills tadalafil 10mg usa buy cialis 20mg sale
canadian viagra online pharmacy order cialis pills tadalafil max dose
https://tadalafil.pro/# buy tadalafil over the counter
https://sildenafil.pro/# how to get sildenafil cheapest
price for amoxicillin 875 mg amoxicillin buy online canada
https://antibiotic.icu/# macrobid antibiotic
tadalafil online canada tadalafil canadian pharmacy online
price comparison tadalafil buy tadalafil 10mg india
best online casino usa best ed pills write my paper for me
buy tadalafil online usa tadalafil 20mg online canada
online casino usa online assignment writer how to write a hiring letter
https://antibiotic.icu/# flagyl antibiotic
how much is sildenafil 20 mg cheap sildenafil citrate
https://amoxicillin.pro/# amoxicillin 500 mg tablet price
write essay for money help write my paper usa cialis sales
affordable essays herbal ed pills buy generic tadalafil
https://lipitor.icu/# price canada lipitor 20mg
buy cipro buy cipro cheap
https://stromectol.pro/# ivermectin american journal of therapeutics
where can i buy cipro online ciprofloxacin 500 mg tablet price
azathioprine for sale online azathioprine pills buy micardis sale
cheap azathioprine 25mg viagra next day delivery usa order micardis 20mg generic
buy cipro online canada cipro online no prescription in the usa
generic molnupiravir 200mg molnupiravir 200 mg drug prevacid drug
https://lipitor.icu/# lipitor prescription cost
https://pharmacy.ink/# canadian pharmacy world coupons
cost molnupiravir cost lansoprazole 30mg prevacid 15mg oral
zestril generic zestril price in india
https://stromectol.pro/# ivermectin benefits for humans
lisinopril 80mg cost of lisinopril 20 mg
imuran pills buy nifedipine 10mg generic order phenazopyridine 200 mg
ciprofloxacin mail online cipro online no prescription in the usa
https://ciprofloxacin.icu/# cipro ciprofloxacin
imuran pills buy nifedipine generic phenazopyridine canada
https://ciprofloxacin.icu/# cipro ciprofloxacin
If you re looking for a lube that s all natural, glycerin free and has no harsh chemicals, while also leaving you feeling soft, supple and moisturized, that also doesn t have a heavy taste or smell and comes respectfully packaged not to mention being totally affordable for both the amount you re getting and level of quality offered, I d highly suggest trying Babelands Natural Babelube, it s definitely worth the under priced 12 best site to buy cialis online
order acetazolamide 250mg for sale symmetrel pills cost montelukast 10mg
https://ciprofloxacin.icu/# ciprofloxacin mail online
ciprofloxacin 500 mg tablet price cipro pharmacy
https://withoutdoctorprescription.xyz/# canada ed drugs
tamoxifen skin changes tamoxifen chemo
covid tablet molnupiravir brand name
https://viagracanada.xyz/# walgreens viagra substitute
buy prescription drugs prescription drugs without prior prescription
acetazolamide buy online order montelukast 10mg sale order singulair online
paxlivid pfizer antiviral pill
order cialis 10mg sale buy amoxicillin 250mg pill purchase deltasone online
https://withoutdoctorprescription.xyz/# canadian online drugs
https://molnupiravir.life/# merck antiviral
buy anti biotics without prescription tadalafil without a doctor’s prescription
molnupiravir covid molnupiravir by merck
To komfortowy pokój z pełnym lub częściowym widokiem na morze, który wraz z wygodnym fotelem oraz dużym biurkiem, pozwoli pogodzić pracę z odpoczynkiem. Dedykowany dla osób podróżujących w celach biznesowych jak i wypoczynkowych. KONNO PO PLAŻY BEZ UMIEJĘTNOŚCI: Jedyne miejsce w Polsce, gdzie można konno jeździć po plaży! Konie są specjalnie szkolone i reagują na gesty przewodnika. Pozwólcie sobie poczuć wiatr we włosach oraz morską bryzę na twarzy. Popatrzcie jak pięknie odbija się słońce w tafli wody i posłuchajcie jak szumi las. Oferta dostępna dla dziewczyn bez Wypocznij po długiej podróży w pokoju Club na wygodnym łóżku Sheraton Signature. Otwórz prywatny balkon i pozwól by morska bryza wypełniła Twój pokój. Wieczorem odwiedź nasz Club Lounge by zakończyć dzień przy wyśmienitym drinku. https://skiwakeboat.com/community/profile/bobbyenai976605/ Z opisanego stanu faktycznego wynika, iż ma Pan zamiar wyjechać do Wielkiej Brytanii i utrzymywać się z gry w pokera online. Chciałby Pan dowiedzieć się, jak wygląda tam sytuacja podatkowa w tym aspekcie – jakie podatki musiałby Pan uiszczać? Kiedy mógłby Pan starać się o status rezydenta podatkowego w UK i mieć zobowiązania jedynie wobec organów podatkowych w UK? Oraz jak legalnie prowadzić taką działalność w UK, czy trzeba ją gdzieś rejestrować i jak to wygląda? W niedzielę na PokerStars odbędzie się specjalny turniej freeroll dla członków szkoły pokera PokerStrategy. Pula nagród tego darmowego turnieju wyniesie aż $10 000. Udział w nim może wziąć każda osoba, która choć raz dokonała depozytu… Pierwsze naziemne kasyno w Polsce powstało w 1920 roku w Sopocie. Początkowo było dość skromne, gdyż można było w nim zagrać tylko w Ruletkę. Następnie wprowadzono Bakarata. Po kilku latach goście zjeżdżali tu z różnych zakątków kraju i świata aby pograć również w Blackjacka i Pokera. Profity z prowadzenia kasyna oraz liczba miłośników hazardu, którzy regularnie przybywali do kurortu sprawiły, że w 1927 roku powstał ekskluzywny Grand Hotel.
tamoxifen cancer nolvadex only pct
https://paxlovid.best/# paxlovid ingredients list
https://paxlovid.best/# antiviral covid
purchase azithromycin without prescription zithromax 500mg pills oral prednisolone
women in viagra commercials viagra prescription online
azithromycin 250mg usa prednisolone 40mg drug prednisolone 40mg price
https://paxlovid.best/# paxlovid canada
buy prescription drugs from india ed meds online without prescription or membership
https://paxlovid.best/# covid antivirals
https://molnupiravir.life/# molnupiravir
does tamoxifen make you tired tamoxifen bone pain
https://tamoxifen.best/# tamoxifen therapy
doxycycline 100mg us baricitinib 2mg us ivermectin 12 mg
https://paxlovid.best/# paxlovid deutschland
do you need prescription for viagra what exactly does viagra do?
https://withoutdoctorprescription.xyz/# meds online without doctor prescription
cost lopressor 50mg medrol 16mg online levitra 20mg brand
tab molnupiravir price molnupiravir in bangladesh
https://viagracanada.xyz/# what happens if a female takes viagra
cost metoprolol order clomid without prescription vardenafil online
ivermectin dosage human ivermectin and coronavirus
https://stromectol1st.com/# tab ivermectin 12 mg
ivermectin fleet farm does ivermectin kill lice
https://stromectol1st.com/# ivermectin to treat covid
stromectol for scabies merck stromectol brand
order albuterol 4mg pill aristocort pills aristocort 10mg pill
order albuterol online cheap triamcinolone cheap triamcinolone 10mg us
ivermectin 400 mg stromectol cream
© 2022 CTS All Rights Reserved. Privacy Policy Think about it: most of the marijuana strains at dispensaries these days are high in THC and low in CBD. If two strains have 17 percent THC and 0 percent CBD, it must be something else that’s responsible for one gluing you to the couch and the other stimulating your mind. It is other phytochemicals found in cannabis plants that are to thank for these difference, including minor cannabinoids and another category of phytochemicals called terpenes. This so-called “entourage effect” refers to this scrum of compounds supposedly working in concert to create what Chris Emerson describes as “the sum of all the parts that leads to the magic or power of cannabis.” Emerson is a trained chemist and the co-founder of a designer marijuana vaporizer products company called Level Blends. Product designers like him believe they can create THC vaping mixtures tuned with different concentrations of each terpene and cannabinoid for specialized effects. https://johnnyoesh219864.p2blogs.com/14507905/medical-marijuana-dispensary-british-columbia “We are worried that 2022 could be a year of retail closures in Ontario,” Chen said. “Unless more municipalities opt-in for cannabis stores, this could lead to a (year-over-year) decline in industry sales.” Before submitting an application to the Federal government, the person that intends to submit the application must provide a written notice to the local government, police, and fire in the area in which the site referred to in the application is located. The notice must be addressed to a senior official of the local authority to which it is provided. In Oakville, it is the Chief Building Official so that the application can be reviewed for zoning compliance to determine what the primary use is in accordance with existing use definitions such as Agriculture or Manufacturing, and the applicable zoning permissions.
ivermectin argentina ivermectin for ear mites
https://stromectol1st.com/# ivermectin label
ivermectin 1 dosage for dogs ivermectin price in india
https://stromectol1st.com/# ivermectin breast cancer
https://stromectol1st.com/# what is stromectol
buy acyclovir without prescription order zyloprim without prescription buy aceon 4mg without prescription
buy prescription drugs buy prescription drugs without doctor
https://drugsfromcanada.icu/# prescription drugs online without
https://24hr-pharmacy.top/# canadian pharmacies not requiring prescription
buy prescription drugs from canada cheap cheap pet meds without vet prescription
zovirax order online perindopril order online buy perindopril for sale
order allegra 180mg online cheap fexofenadine online buy panadol 500mg over the counter
https://ed-pills.xyz/# erectile dysfunction pills
buy doxycycline over the counter uk doxycycline cheap
where to buy clomid canada clomid 5 mg tablet
https://clomid.pro/# buy clomiphene online
ed meds online without doctor prescription canadian drug prices
https://doxycycline.pro/# doxycycline over the counter uk
prescription drugs canadian pharmacy online
clomid 400mg generic clomid for sale
https://doxycycline.pro/# doxycycline for dogs
cheap erectile dysfunction pills online ed medications
buy fexofenadine online phenytoin 100 mg canada paracetamol 500mg for sale
mexican pharmacy without prescription prescription without a doctor’s prescription
best ed pills non prescription pain meds online without doctor prescription
trileptal pills ursodiol cheap rosuvastatin 10mg price
https://24hr-pharmacy.top/# best canadian online pharmacies
buy prescription drugs from canada legal to buy prescription drugs from canada
doxycycline order online uk where to buy doxycycline in singapore
https://clomid.pro/# clomid 50 mg buy uk
doxycycline price 53 Zinc is also inexpensive and has shown cost- effectiveness in developing countries, but is associated with episodes of vomiting, which is a cause for future research.
Science shows that what really works to clear acne is gentle skin care. doxycline chicago Some patients can present with bone marrow failure symptoms and low blood counts but on examination of the bone marrow large numbers of blast cells are found, confirming a diagnosis of acute leukemia.
oral trileptal order urso 300mg without prescription rosuvastatin brand
https://24hr-pharmacy.top/# prescription drugs from canada online
doxycycline 200 doxycycline 3626
purchase zetia oral motilium order baclofen 25mg online
bactrim and sepra without a presription amoxicillin 500mg no prescription
https://erectionpills.top/# top rated ed pills
canadian pharmacy coupon code prescription free canadian pharmacy
https://canadianpharmacy.best/# canadian pharmacies that deliver to the us
canadian pharmacy levitra canada ed drugs
Bonuses in the poker world work a little differently to other gambling products. For casino, bingo and sports you normally get to wager with your bonus either straight away or after a relatively easy trigger has been met (such as betting your deposit once), but with poker the bonus is released as you play. So if a poker room is offering a 50% bonus up to $200, they are offering to give you 50% of the amount you deposit free as an extra bonus up to a maximum of $200. Therefore by making a deposit of $400 you will receive the maximum bonus available (50% of $400 = $200). As your abilities grow, you’ll be drawn to fast-paced real money poker games, which are offered at the best online poker sites. Sit&Go Tournaments are perfect for this. These tournaments may be played with two players at a time, with the pace of play set to standard, turbo, or super-turbo. The buy-in might be as little as ten dollars or as much as a thousand dollars. When all of the seats are occupied, the event starts, and the blind increases every 4 minutes. Blast is a unique playing option with a timer that we propose for a Super Turbo Texas Hold’Em Sit & Go tournament. When the blast counter reaches 0, all players go all-in until a winner is selected. Many of our top Canada poker sites offer this sort of event. https://felixbpds653208.azzablog.com/13504302/wild-joker-bonus-codes Casino T&C apply. Casino bosses know the importance of treating their players “right.” That is why land-based casinos have comps and other perks. Rich Casino has the same philosophy, offering you tons of bonuses and lucrative prizes on one condition – you play often at the casino. Australia’s Rich Casino is the best place to gamble from your mobile phone or pad. The licensed platform has been operating since 2009 and provides players with bright emotions and big wins on 1,500 machines. Most of the gaming machines developed by top providers are available in the mobile version. Here you can get pleasant bonuses for playing from your smartphone, which will increase your chances of winning. We’ll talk about this and more in our review Rich Casino mobile. If you are a Slots fanatic then Rich Casino is the place to be! This online casino hosts exciting Slots tourney on a regular basis. In order to take part, simply make the required minimum deposit and spin the reels of eligible Slots games. After that, the more you play, the higher are your chances to rank somewhere on the leaderboard to take home a share of humongous prize pools. Sunday Storm, Thermal Thursday and Sunday Super Reel are a few examples of Rich Casino Slots Tournaments.
buy tizanidine buy generic tizanidine cialis otc
order tizanidine 2mg generic tizanidine drug buy cialis 10mg
bactrim antibiotic online prescriptions cost of amoxicillin prescription
order lipitor pill order atenolol 50mg generic pregabalin cheap
cost atorvastatin 80mg atorvastatin 10mg oral buy lyrica 150mg generic
mail order prescription drugs from canada rx pharmacy coupons
https://erectionpills.top/# buy erection pills
canadianpharmacyworld com canadian online pharmacy cialis
https://antibioticwithoutpresription.shop/# buy zithromax no prescription
cheap antibiotic bactrim antibiotic online prescriptions
legit canadian online pharmacy legitimate canadian mail order pharmacy
https://canadianpharmacy.best/# canadian pharmacies that deliver to the us
cheapest prescription pharmacy no prescription needed pharmacy
zithromax for sale cheap buy cheap zithromax online
desloratadine for sale online asacol sale mesalamine pill
desloratadine 5mg for sale amaryl order online order mesalamine 400mg pills
what is the best ed pill medications for ed
https://antibioticwithoutpresription.shop/# buy generic zithromax no prescription
erection pills viagra online treatment for ed
https://erectionpills.top/# best ed medication
no prescription needed pharmacy canada drugs coupon code
cheapest pharmacy to get prescriptions filled best no prescription pharmacy
https://canadianpharmacy.best/# vipps canadian pharmacy
cheapest ed pills best medication for ed
cheap irbesartan 150mg pepcid 20mg oral oral famotidine 20mg
avapro 300mg cost clobetasol drug order pepcid 40mg online
canadian pharmacy online reliable canadian pharmacy reviews
bactrim no prescription can we buy amoxcillin 500mg on ebay without prescription
https://pharmacywithoutprescription.best/# uk pharmacy no prescription
how much is amoxicillin prescription zithromax 500 without prescription
https://canadianpharmacy.best/# canadian pharmacy viagra
reputable canadian pharmacy canadian pharmacy online cialis
buy tacrolimus buy prograf 5mg sale fenofibrate 200mg canada
tacrolimus 1mg drug buy labetalol generic order tricor 200mg online
zithromax online no prescription bactrim without a prescription
https://antibioticwithoutpresription.shop/# buy doxycycline online without prescription
ed pills gnc online ed medications
Hello ! I am the one who writes posts on these topics casino online I would like to write an article based on your article. When can I ask for a review?
canadian pharmacy tampa canadian pharmacy online reviews
purchase colchicine buy plavix 75mg without prescription clopidogrel 75mg pill
cheap colchicine clopidogrel ca buy clopidogrel for sale
canadian pharmacy no prescription needed canada pharmacy coupon
https://canadianpharmacy.best/# canadian drugs pharmacy
ed drugs list ed medications
https://antibioticwithoutpresription.shop/# buy zithromax without prescription online
ed pills for sale treatment for ed
buy cheap doxycycline amoxicillin 500 mg purchase without prescription
https://canadianpharmacy.best/# is canadian pharmacy legit
zithromax buy online no prescription zithromax prescription in canada
order altace generic buy cordarone pill order coreg 25mg generic
altace 10mg ca buy buspar 5mg online cheap buy coreg 6.25mg online cheap
cheap antibiotic bactrim without a prescription
https://antibioticwithoutpresription.shop/# buy doxycycline online without prescription
where to buy amoxicillin 500mg without prescription amoxicillin without prescription
https://antibioticwithoutpresription.shop/# buy cheap amoxicillin online
cheapest pharmacy to fill prescriptions with insurance uk pharmacy no prescription
sildenafil tablets 100mg cost sildenafil 105 mg canada
https://doxycyclinemonohydrate.icu/# where to purchase doxycycline
buy doxycycline cheap where to purchase doxycycline
where to purchase doxycycline generic doxycycline
https://buytadalafil.icu/# buy tadalafil cialis
buy oxybutynin order ditropan 2.5mg sale nitrofurantoin without prescription
ditropan online nitrofurantoin 100 mg oral furadantin 100 mg pills
sildenafil canada over the counter sildenafil 50mg tablets uk
what is minocycline prescribed for ivermectin 5 mg price
https://buytadalafil.icu/# canadian pharmacy generic tadalafil
generic for doxycycline doxycycline pills
order ibuprofen 400mg generic buy mirtazapine sale buy calcitriol 0.25mg without prescription
tadalafil 5 mg tablet coupon tadalafil 20 mg price canada
https://buysildenafil.best/# sildenafil 5 mg price
sildenafil otc canada cheap price sildenafil 100 mg
motrin for sale paxil 10mg canada rocaltrol 0.25mg cheap
buy doxycycline for dogs buy doxycycline 100mg
https://buytadalafil.icu/# where can i get tadalafil
buy cheap doxycycline online where to get doxycycline
zyban canada cyclobenzaprine order online order viagra 50mg
generic for doxycycline buy doxycycline monohydrate
https://pillswithoutprescription.xyz/# canadian drug
minocycline cost buy ivermectin for humans uk
buy bupropion without prescription purchase cyclobenzaprine sale viagra 50mg without prescription
sildenafil 200mg price sildenafil drug
https://buysildenafil.best/# sildenafil 100mg tablets uk
tadalafil online india tadalafil online without prescription
п»їwhere to buy stromectol online cost of ivermectin lotion
https://buysildenafil.best/# 100mg sildenafil 30 tablets price
order methotrexate online buy coumadin pill buy cozaar
buy methotrexate pills order generic coumadin cozaar 25mg uk
Thanks very interesting blog!
https://comprarcialis5mg.org/it/
http://photographybycynthiablog.com/2017/05/lifestyle-session-tips/
cialis generico https://comprarcialis5mg.org/it/
Beim Ramses Book sind wir in einer der alten Grabstätten, welche im Schein der Fackeln orange und golden strahlen. Das Logo ist wie üblich über dem Spielfeld angebracht. Das macht bei dieser Art Slot auch durchaus Sinn, denn es gibt gefühlte hunderte Bücher- und Ägyptenslots. Mit der richtigen Ramses Book Strategie ist es kein Problem, viele Stunden lang großen Spaß an diesem tollen Slot zu haben. Da die Ramses Book Gewinnchance recht hoch ist, sollte am Ende auch ein stattlicher Gewinn winken. (Match Bonus zu 100 %) Entwickler Bally Wulff hat das Spielfeld ins tiefe Innere einer Pyramide verlegt. Hier geht es online kostenlos auf Schatzsuche. Man wird dabei auf einige themenbasierte Symbole treffen, welche die Geschichte Ägyptens weiter ans Licht bringen. Darunter fallen neben dem Pharao höchstpersönlich auch der Adler-ähnliche Gott Horus, die berühmten Sphinx-Katzen und eine alte Säule mit geschichtsreichen Gravierungen. Die Spannung steigt bei Ramses Book online, sobald die Walzen nach einer Drehung zum Stillstand kommen. Dieser Moment wird von filmreifer Musik begleitet. Treffen Sie beim Ramses Book Spielen eine Gewinnkombination, erwachen die beteiligten Symbole zu Leben und intensivieren das Erlebnis. https://ikatanalumniistn.com/community/profile/raefrantz510044/ EuroMillionen Systemscheine .. Bei der europäischen Lotterie “Euromillionen” hat am 28. April 2006 erstmals ein in Österreich abgegebener Wettschein bei „5 plus 2 Richtige“ im ersten Rang gewonnen. Die Besonderheit dabei war, dass auf dem in Wien gespielten Schein die richtigen Zahlen gleich zwei Mal vertreten waren (Gesamtgewinn 13 Millionen Euro). Bei den EuroMillionen gibt es verschiedene Systeme, die sich durch die Anzahl der Zahlen unterscheiden, die man ankreuzen kann. Wie kann sich Lottoland das alles leisten? Wählen sie ihre fünf zahlen (1-50) und zwei sterne (1-12) 01.01.2020 19:30 In Deutschland betragen die Spieleinsätze momentan (2006) rund fünf Milliarden Euro pro Jahr. Sie werden wie folgt verwendet: Bei einem Systemtipp werden auf dem Tippfeld mehr als die eigentlichen 5 aus 50 Zahlen und oder 2 aus 12 ausgewählt. Damit tippen Sie dann auf alle möglichen Zahlenkombinationen für die möglichen 7 Richtigen Zahlen. Da Sie hier auf deutlich mehr Zahlenreihen gleichzeitig tippen, kann die Gebühr für den Tippschein auch deutlich teurer werden.
cephalexin 125mg over the counter cost erythromycin 250mg erythromycin 250mg brand
cephalexin 250mg pills order erythromycin generic buy erythromycin pills
buy generic fildena 50mg budesonide order purchase rhinocort pill
fildena 50mg tablet nolvadex online budesonide allergy spray
https://datingtopreview.com/# sex dating free
buy generic cefuroxime 250mg bimatoprost online buy buy methocarbamol 500mg generic
order cefuroxime sale ceftin cost robaxin brand
order desyrel 50mg pills buy desyrel 50mg pfizer viagra 50mg
order desyrel 50mg pill desyrel medication sildenafil 100mg sale
tadalafil for sale online tadalafil tablets 20 tadalafil sales
atorvastatin muscle pain atorvastatin 20 mg side effect can you take atorvastatin in the morning?
cost cialis low cost ed pills cialis 10mg usa
cialis pills 5mg ed pills online buy tadalafil 10mg online cheap
how to get neurontin cheap how much is generic neurontin how much neurontin is safe
viagra 1 tablet price cheap viagra fast delivery viagra price in mexico
where to buy cialis online for cheap cialis discount coupons cialis store in qatar
how much is viagra in mexico cheap sildenafil online canada viagra online fast delivery
Urispas canadian pharmacy chains pharmacy website
online free dating sites sex dating site
oral glucophage 1000mg oral metformin norvasc pills
order generic metformin 500mg atorvastatin pills norvasc 10mg canada
https://datingtopreview.online/# singles near me free
sildenafil 150mg tablets viagra where to buy over the counter sildenafil discount
https://datingtopreview.com/# dating free site online
D, Additional CRISPRa target genes tested in neurons demonstrated leaky induction in the absence of Cre recombinase two way ANOVA with n 3 per group for Gadd45b F 1, 12 91 lasix for hypertension
dating sjtes best free online dating sites
https://datingtopreview.com/# bbw dating sites
tadalafil citrate liquid tadalafil patent expiration cialis tadalafil 10 mg
https://datingtopreview.online/# mature dating
lisinopril online order atenolol 50mg pill tenormin brand
order lisinopril 2.5mg sale order generic lisinopril 5mg buy tenormin 50mg pills
https://datingtopreview.com/# date women free
dating service hotmail south africa best dating site online
totally free dating sites near nelson find online dating
https://datingtopreview.com/# local dating sites
purchase tadalafil cialis free sample cialis prices
canadian pharmacy oxycodone canadian pharmacy sildenafil
subtle asian dating westminster dating app the world
https://withoutprescription.shop/# canadian pharmacy ship to us
https://pharmacyreview.best/# www canadianonlinepharmacy
viagra online canada no prescription sildenafil 100 no prescription viagra price mexico
viagra cialis from germany order tadalafil 20mg what is the difference between viagra and cialis
https://safedrg.com/# reputable canadian pharmacy
canadian discount pharmacy canadian online pharmacy no prescription
Tadalis SX canadian discount pharmacy online london drugs surrey bc canada
prescription drug prices comparison reputable canadian pharmacy
order cialis 5mg online cheap buy cialis 5mg for sale sildenafil 150mg sale
oral tadalafil cialis generic name purchase sildenafil without prescription
foreign online pharmacy canadian drugs online pharmacy
https://pillfast24.online/# canadian neighborhood pharmacy
fusion rx compounding pharmacy non prescription online pharmacy reviews Epivir-HBV
aarp recommended canadian pharmacies canadian drug store
where to buy generic viagra over the counter viagra men otc viagra online
Regards, Quite a lot of information!
penalty for mailing prescription drugs best online drugstore pharmacy online coupon
online pharmacy no prescription needed online pharmacy no prescription
https://cheapestpharmacy.store/# canada online pharmacy no prescription
legit non prescription pharmacies pharmacy online 365 discount code
You mentioned it terrifically!
CYP 2D6 is also known as debrisoquine hydroxylase that catalyzes the oxidation of approximately a quarter of all the commonly therapeutic drugs in used clinical practice today priligy buy online usa 3 of 1926 women or a BMI of less than 25 kg m 592 31
buy generic viagra online uk otc viagra usa viagra 50mg online in india
no prescription required pharmacy cheapest pharmacy for prescriptions without insurance
canadian pharmacies no prescription us online pharmacy
https://noprescription.store/# best canadian pharmacies
personals online cdff dating site login
https://cheapestpharmacy.store/# pharmacy no prescription required
sildenafil pills uk cheapest price for sildenafil 100 mg best generic viagra in india
canadian pharmacy store canadapharmacyonline com
https://bestadultdating.fun/# date online free site
fdating international date me site
ivermectin and collies stromectol covid 19
tadalafil cialis generic cialis tadalafil uk
cost doxycycline cheapest doxycycline tablets
order sildenafil no prescription cheap sildenafil 50mg
https://buyamoxil.site/# amoxicillin 250 mg capsule
Thanks a lot. I appreciate this!
cheap meds no prescription buy viagra from canadian pharmacy canadian pharmacy viagra generic
Many thanks. Wonderful information!
us online pharmacy bringing prescription drugs into japan canadian health pharmacy
viagra pills over the counter canada can i order viagra online online generic viagra india
https://clomidforsale.site/# clomid price
Kudos. I appreciate this.
mail order drugs from canada legal ed pills that work quickly wegmans online pharmacy
buy clomiphene online clomid price
how to buy amoxicillin online amoxicillin 500 mg price
https://clomidforsale.site/# clomiphene generic
tadalafil 20 mg mexico tadalafil cost india
clomid medication generic clomiphene
Really tons of superb info!
cheapest pharmacy to fill prescriptions with insurance medication online legit canadian pharmacy sites
how to get amoxicillin amoxicillin 500 mg cost
https://nonprescriptiontadalafil.site/# tadalafil 20 mg buy online
sildenafil 10 mg price sildenafil citrate over the counter
Terrific information, Regards!
rx plus pharmacy sanford best online pharmacy for adderall doctor of pharmacy degree online
Awesome content. Regards!
valium online pharmacy benzodiazepines online pharmacy aarp recommended canadian pharmacies
tadalafil best price 20 mg buy cialis with prescription australia where to buy cialis
Thanks. I enjoy this.
canada pharmacies without script family mart store online pharmacy addiction to prescription drugs
You made your stand pretty well!.
cvs pharmacy store hours on sunday cheap drugs online walmart pharmacy online login
Thanks! Very good stuff!
best online mexican pharmacy generic cialis canada online pharmacy cheapest prescription pharmacy
Tips certainly taken.!
canadian prescription drugs rx software pharmacy canadian pharmacy coupon code
cialis strength cialis samples free how much is cialis in canada
Many thanks, I enjoy this.
canadian pharmacies compare planet drugs canada cheapest canadian pharmacy for viagra
buy prednisone 20mg without a prescription best price can you buy prednisone over the counter in canada
how much is sildenafil 25 mg cost generic viagra viagra pills australia
single women dating fdating 100 free dating site free
With thanks! Fantastic information!
pharmacy wholesalers canada what are the best online canadian pharmacies prescription drug discounts
Truly plenty of fantastic information!
best canadian pharmacies for cialis steroids online pharmacy canadian pharcharmy online fda approved
Cyclosporin A, another P gp antagonist, also enhanced C6 ceramide cytotoxicity lasix adverse effects
viagra gel uk generic viagra cheap canada viagra pills australia
With thanks! I appreciate it.
online pharmacy greece nps online pharmacy reviews list of safe online canadian pharmacies
Great information. Many thanks.
legal canadian prescription drugs online rx relief pharmacy discount cards cheap canadian pharmacies online
Superb knowledge. Kudos!
domperidone from canadian pharmacy reviews of canadian pharmacies quality prescription drugs
Regards, I like it.
rx crossroads pharmacy canadian online pharmacy calls canada pharmaceuticals online generic
buy prednisone tablets uk prednisone 10mg
https://ed-pills.site/# best male ed pills
thecanadianpharmacy canadian pharmacy levitra
when cialis patent expires buy low dose cialis online cialis recreational use
https://canadiandrugs.site/# legitimate canadian mail order pharmacy
order viagra canadian pharmacy cheap discount viagra sildenafil otc europe
Thanks a lot, Quite a lot of knowledge!
best australian online pharmacy web pharmacy walmart online pharmacy medical expense report
Really quite a lot of wonderful facts!
canadian medication canadian pharmacy chains pharmacy drugs store
azithromycin lloyds pharmacy arcoxia online pharmacy walmart pharmacy diflucan
https://topdatingsites.fun/# free app for online meeting
canadian pharmacy cialis 40 mg canadian online pharmacy cialis
Fantastic information. With thanks!
turkish pharmacy online canadian pharmacy ratings online cvs pharmacy
viagra medicine in india viagra purchase where can i buy over the counter sildenafil
With thanks, I appreciate this!
canadian pharmacy viagara canada discount drugs online global pharmacy in canada
You actually expressed this well.
online pharmacy worldwide shipping mexican pharmacy online oxycodone prescription drugs account for 25% of all healthcare-related costs
You made your point very effectively!!
best online pharmacy xanax cheap canadian cialis online walgreens pharmacy refill online
cialis & viagra genpharma tadalafil how to buy tadalafil
baclofen uk pharmacy viagra uk pharmacy cabergoline pharmacy
what is the best ed pill edpillsfast.com
treatment of ed ed pills
cialis tadalafil vs viagra over the counter cialis tadalafil 5 mg
https://edpillsfast.com/# pills erectile dysfunction
pill for erectile dysfunction cure ed
otc ed pills ed pills without doctor prescription
https://edpillsfast.com/# cheap ed drugs
ed pills online canada ed drugs list
Truly a good deal of superb advice.
tier 4 prescription drugs canada prescription drugs online the canadian pharmacy
vipps canadian pharmacies licensed canadian pharmacies russian pharmacy online
https://canadadrugspower.com/ cambridge essay service
order viagra from canadian pharmacy buy sildenafil generic online cost of generic viagra in canada
You mentioned this effectively!
lasix online pharmacy canadian high quality pharmacy canadian council for accreditation of pharmacy programs
safest canadian online pharmacy wisconsin canadian pharmacies bachelor of pharmacy online
https://canadianonlinepharmacybase.com/ content of a term paper
Cheers, Loads of knowledge.
meds canadian compounding pharmacy online pharmacy technician courses target pharmacy store locator
safe online pharmacy canada perscription drugs in canada cvs pharmacy 24 hours store locator
https://canadadrugspower.com/ best essay website
levitra and viagra together when will generic levitra be available taking viagra and levitra together
pills for ed edpillsfast.com
erectile dysfunction medicines medications for ed
Whoa quite a lot of helpful information.
online pharmacy soma ed meds online pharmacy technician certification
california board of pharmacy canada drugs compare pharmacy prices
https://canadapharmacies-24h.com/ write my lab report for me
Truly all kinds of terrific tips!
most dangerous prescription drugs pharmacy discount card rx relief wellbutrin xl canada pharmacy
Very good write ups. Thank you.
best online ed medication no prescription online pharmacy illegal drugs in canada
check prescription prices navarro pharmacy miami cialis from canada
https://canadianpharmacyonlinedb.com/ cheap essay buy
Reliable stuff. Kudos.
online pharmacy bc canada drugs com review rexall first canadian place pharmacy
prescription drug derm rx pharmacy Extra Super Avana
https://canadapharmacies-24h.com/ working thesis
Useful content. Appreciate it.
Viagra with Dapoxetine pharmacy tech online training free online pharmacy programs
pharmacy tech online training fda approved online pharmacies canadian discount pharmacy online
https://canadianpharmacyonlinedb.com/ research methodology dissertation
cheap ed drugs edpillsfast.com
top rated ed pills ed pills
https://edpillsfast.com/# best ed pills non prescription
ed pills without doctor prescription cures for ed
otc ed pills ed pills
https://edpillsfast.com/# best treatment for ed
ed pills online canada best ed medication
You actually said that perfectly!
doctor of pharmacy degree online canadian family pharmacy reviews prescription diet drugs
rx city pharmacy canadian pharmacy comparison pharmacy website india
https://canadianpharmaceuticalsonlineus.com/ homework help alabama
You expressed this perfectly.
mexico pharmacy online can americans order pregabalin from canadian pharmacies no rx online pharmacy
Amazing many of wonderful material!
viagra at canadian pharmacy online canadian pharmacy cialis vyvanse canadian pharmacy
adderall canadian pharmacy tylenol with codeine online pharmacy trust pharmacy
https://northwestpharmacylabs.com/ find someone to write my college paper
cialis daily cost cialis for daily use side effects cialis at a discount
Thank you, Excellent information!
ed drugs over the counter buying drugs from canada online canadain pharmacy no prescription
Thank you, An abundance of tips.
canada drugs laws ed meds chem rx pharmacy
canadian pharmacy without prescriptions online medicine tablets shopping mexican pharmacies that ship
https://northwestpharmacylabs.com/ i need to buy a research paper
Order online from our sponsored stores. Production My Cachexia syndrome was causing me to lose weight and become unhealthy, so I had decided to use medical cannabis to treat it. My friend recommended me to this site. She had used it when she got her own card. So I applied online and was pre-approved just like that. The process was very easy and the people in the clinic made me feel comfortable. I would recommend this site to anyone. Please keep in mind prices are going to differ. We use number ranges instead of exact amounts throughout the rest of this post. Also, the prices we’ve quoted are for high-quality marijuana. Lesser quality should cost you much less. That said, here’s a price breakdown for each of the major forms of weed: In California, you’ll pay $1,000 to apply for a dispensary license, and if approved, you’ll pay a licensing fee between $4,000 and $120,000, depending on the estimated value of your operation. You’ll also need to factor in real estate, which can cost between $50,000- $100,000 annually, as well as other startup costs. The cost of living is high in California, and you can expect to pay employees a bit more than national averages, with budtenders each costing around $30,000 – $40,000 per year. https://amyyuan.ca/community/profile/irenefaulding47/ You should only purchase cannabis from legal retailers in your province or territory. Common signs to help identify an illegal cannabis retailer are: Information on legal cannabis in all provinces and territories is provided below, including: Whether you’re brand new or an old pro, our cannabis content library has you covered We will also target public education to children and youth, focusing on both the health effects and the risks of buying from the illicit market (including exposure to unsafe products, unknown potencies and other illegal drugs). Similar to public awareness for alcohol, public education will also target parents, who may be a source for cannabis for some youth. If you’re concerned or have a complaint about a possible illegal cannabis activity whether online or in your community contact your local law enforcement or nearest Royal Canadian Mounted Police (RCMP) detachment.
https://canadiandrugpharmacy.best/# best canadian pharmacy
legitimate canadian online pharmacies northwest canadian pharmacy
With thanks! I like this.
list of canadian online pharmacies online medicine order discount ramesh rx pharmacy
You actually stated this adequately.
what are the store hours for cvs pharmacy canadian prescription prices prescription drugs canada legal
Thanks a lot, Helpful information.
best rx online pharmacy medicine prices vicodin canadian pharmacy
https://sildenafil100mg.store/# sildenafil soft
Nicely put. Thank you.
cvs pharmacy store locators canada pharmacy online orders Theo-24 Cr
tadalafil 22 mg canada tadalafil generic
https://datingsiteonline.site/# searchingforsingles
You said it perfectly..
rate online pharmacies fred’s pharmacy Pharmacy & Quick Delivery
Great write ups. Regards!
medication without prior prescription which online pharmacy is the best cheap rx drugs
connecting singles personals online
https://datingonlinehot.online/# dating sex
Amazing data. Thanks a lot!
cvs pharmacy store locator prescription drugs itching pharmacy technician online
cheap cialis canada pharmacy online pet pharmacy reviews canadian pharmaceuticals online safe
https://canadapharmacyspace.com/ how to write a observation paper
date free internet free dating online
https://datingonlinehot.online/# free dating ads
adult chat dating site dateing sites
With thanks, Lots of content.
canadian pharmacies legitimate highest discount on medicines online lodon drugs canada
canadian pharmacy cialis licensed canadian pharmacies ed drugs list
https://canadapharmacyspace.com/ writing outlines for essays
https://datingonlinehot.online/# personals dating
free online dating sites online dating sites for free 100%
However, the overall resulting protein structure is likely to be very different ERО± folds into a conformation capable of interacting productively with coactivators, whereas ERОІ fails to do so tamoxifen side effects in the elderly
Excellent information. Thanks.
thai pharmacy online pharmacy online rx health mart pharmacy
online pharmacy pain compounding pharmacy cheap generic cialis canadian pharmacy
https://edpharmsn.com/ online custom essay writing service
Good facts. With thanks.
Kamagra Polo the canadian pharmacy review ultram canadian pharmacy
pharmacy technician salary canada kroger online pharmacy cvs online pharmacy store
https://edpharmsn.com/ help 123 essay
https://datingonlinehot.com/# dating sites for mature singles adults
You actually reported this very well!
canadian high quality pharmacy steroid online pharmacy online prescriptions canada without
best dating websites online onlinelovedating or meet single
http://avue.info/__media__/js/netsoltrademark.php?d=datingonlinehot.online lesbian dating apps
farmersonly free dateing sites and free dating sites online dating site crossword
Superb postings. With thanks!
discount prescription drugs Super Kamagra online drugstore reviews
You said it adequately..
mail order pharmacy aarp approved canadian online pharmacies list of aarp approved pharmacies
new ed drugs pills erectile dysfunction
https://cheapestedpills.shop/# non prescription ed drugs
A team of researchers from the City of Hope in Duarte, Calif accutane vs tretinoin This rise in cortisol may have contributed to decreased dermal symptoms among the participants
ed meds best pills for ed
https://cheapestedpills.com/# ed medication online
ed drug prices ed treatment pills
Truly a good deal of excellent knowledge!
top online canadian pharmacies watch tour de pharmacy online best online pharmacy
reviews on canadian pharmacy online sams pharmacy canada rx drugs
https://online-pharmacy-inc.com/ uc art requirement
https://cheapestedpills.shop/# new treatments for ed
erection pills top ed pills
Truly lots of amazing tips.
walmart pharmacy price check legit non prescription pharmacies safety of canadian pharmacies
best drugstore liquid eyeliner canada rx drugs best online pharmacy for generic viagra
https://online-pharmacy-inc.com/ freedom writers movie review essay
Really a lot of useful facts.
legal canadian pharmacy pharmacy technician online training canadian pharmacy cialis
Regards, I like this.
canadian neighbor pharmacy how to buy prescription drugs online pharmacy technician job in canada
I’ve been searching for hours on this topic and finally found your post. slotsite, I have read your post and I am very impressed. We prefer your opinion and will visit this site frequently to refer to your opinion. When would you like to visit my site?
https://cheapestedpills.shop/# п»їerectile dysfunction medication
Kudos, An abundance of posts.
rx express pharmacy erectile dysfunction drugs discount canadian drugs
family pharmacy online www canadian pharmacy com store hours for kroger pharmacy
https://pharmacyclineds.com/ how to write an intro for a research paper
W pokerze klasycznym zasady mają 10 zwycięskich układów kart. Oczywiście, poker karty zasady mogą się zmieniać w zależności od wersji, w jaką gramy – ale znajomość tych 10 układów, pozwoli nam szybko wdrożyć się w różne odmiany zasad gry w pokera. Wszystkie one obejmują poker zasady 5 kart. Blackjack European, Mini Baccarat, Caribbean Poker, Oasis Poker Blokada rynku transferowego nie zostanie przeniesiona do gry FIFA 23, ale musisz ponownie uzyskać dostęp zgodnie z opisaną powyżej procedurą. Na tym etapie krupier stawia zakład dwukrotnie wyższy niż wpłacane przez graczy ante, a uczestnicy rozdania mogą spasować, tracąc ante i wszystkie bonusowe zakłady oraz wycofując się z dalszej gry w tym rozdaniu, lub sprawdzić, wyrównując zakład krupiera. W razie sprawdzenia krupier wykłada dwie kolejne karty wspólne. Pulę wygrywa posiadacz najlepszego 5-kartowego układu. https://high-wiki.win/index.php?title=Kasyno_częstochowa_godziny_otwarcia Każdy pokerzysta, poza znajomością podstawowych zasad gry w pokera w internecie, powinien nauczyć się wartości poszczególnych układów kart. Dlatego też dziś przedstawimy je wam w naszym poradniku! W tym momencie każdy gracz ma już pogląd na swoje karty i wie, jaki najmocniejszy układ może z nich stworzyć. Na tym etapie zaczynają się największe licytacje i gra nerwów. Najważniejsze, aby nie zdradzić tego, czy ma się bardzo silne karty w ręku, czy też nie. Tutaj można zastosować strategie blefowania, ale wiąże się ona z dużym ryzykiem. Jeśli przy stole jest osoba, która ma pewny układ pokera królewskiego, z pewnością nie da się zwieść i będzie sprawdzać. Dzięki takiemu rozwojowi sytuacji Texas Hold’em jest nieprzewidywalny i emocjonujący, co przekłada się na jeszcze większe zainteresowanie tą grą.
Beneficial advice. Appreciate it.
uk online pharmacy international delivery free online pharmacy technician training pharmacy mall
verify canadian pharmacy rx pharmacy com best cialis
https://pharmacyclineds.com/ write a research report
online ed pills natural ed remedies
https://cheapestedpills.com/# best treatment for ed
best ed treatment ed remedies
https://cheapestedpills.shop/# ed treatment review
mens erection pills erection pills online
Superb write ups. Thank you!
best canadian online pharmacy 2022 cost prescriptions aarp canadian pharmacies
You expressed this well!
buy prescription drugs canada canadian pharmacy domperidone vipps certified canadian pharmacies
Drug efficacy and safety undergo review and approval by Health Canada, similar to the FDA or the European Medicines Agency procalis levitra
Incredible quite a lot of amazing tips.
the pharmacy store northwest pharmacy com cvs specialty pharmacy
largest canadian pharmacy canadian pharmacy milwaukee importing prescription drugs from canada
https://rxpharmacyteam.com/ reflection essay on writing
You suggested that well!
pharmacy intern walmart online pharmacy elevit online pharmacy
non prescription canadian neighbor pharmacy reviews ketamine online pharmacy
https://rxpharmacyteam.com/ write my term paper free
https://cheapestedpills.com/# best male enhancement pills
Excellent tips. Kudos!
russian pharmacy online usa price prescription drugs list of trusted canadian pharmacies
best canadian pharmacy safe canadian pharmacies online
https://noprescriptioncanada.com/# canadian pharmacy voltaren
no prescription pharmacies drugstore online shopping
https://noprescriptioncanada.com/# online pharmacies canada
https://noprescriptioncanada.com/# online pharmacies without prescription
buy medicine canada aarp approved canadian online pharmacies
pharmacy online mexican pharmacy cialis
https://noprescriptioncanada.shop/# mexican pharmacies online
online pharmacy usa top canadian online pharmacy
In view of the heterozygosity for both mutations, as observed in our patients, this dimeric architecture might implicate a negative impact of one mutated transporter on the function of the other nolvadex online This heart damage can occur during therapy or many months to years after treatment
https://noprescriptioncanada.shop/# canada pharmacy no prescription
pharmacies withour prescriptions non prescription drugs
https://noprescriptioncanada.shop/# cheap canadian cialis online
24 hour pharmacy bestpharmacyonline.com
https://noprescriptioncanada.com/# discount drugs online
safe canadian online pharmacy canadian pharmacy rx
over the counter drug store prescription pricing
https://noprescriptioncanada.com/# prescription price checker
https://noprescriptioncanada.com/# online pharmacy no perscription
most reputable canadian pharmacy cheap drug prices
https://noprescriptioncanada.com/# canada medications online
reputable online pharmacy canadian pharmacy online review
canadian mail order drugs canada pharmacy online orders
https://noprescriptioncanada.com/# canadian drug pharmacy
https://noprescriptioncanada.shop/# amazon pharmacy drug prices
https://noprescriptioncanada.com/# canadian pharmacy delivery
canadian pharmacies online reviews canadian prescription drugs online
https://noprescriptioncanada.shop/# online pharmacy
compare pharmacy prices pharmacy price compare
no prescription pharmacies best price prescription drugs
https://noprescriptioncanada.shop/# canada drugs online reviews
2 Characteristics of BRCA mutant tumors cialis daily These all can be reduced if the amount of estrogen in the body is normalized by administration of natural progesterone as a balancer
cialis 5 mg 1990 Oct; 11 5 329 48
We have a panel of over 350 experts who help us develop content by giving their valuable inputs and bringing to us the latest in the world of healthcare cialis reviews
SALAMOL STERI- NEB 2 is generic cialis available If you are not ovulating, it may require drugs for a while to sort things out
Really lots of wonderful info!
https://service-essay.com/ luxury writing paper
Whoa all kinds of helpful information!
https://ouressays.com/ letter writing help online
Thanks, Excellent stuff!
https://essaywritingservicelinked.com/ writing a dissertation literature review
Truly tons of useful data!
https://essaywritingserviceahrefs.com/ who to write an essay
Quality posts is the secret to invite the people to pay a quick visit the web site, that’s what this site is providing.
https://essaywritingservicebbc.com/
But before we dive into the best ways to lose weight with PCOS, it s important to know what the condition exactly is glaxomed zithromax buy
I think the admin of this web site is genuinely working hard in favor of his site, as here every data is quality based material.
https://essaywritingservicebbc.com
With thanks. Ample forum posts.
essaywritingserviceahrefs.com rutgers college essay
Dengan fitur-fitur terbaik hingga situs KDSlot menjadi agen bandar slot online terbesar 2023. Pelajari pola permainan slot online di situs KDSlot yang terus memberikan pola kemenangan termudah dan terbaik dalam bermain slot online. Segala kemenangan dapat anda raih di situs KDSlot sebagai penyedia game online terbaik di tahun 2022.
You mentioned this well!
pay for someone to write your essay https://quality-essays.com/ essay buy online
You expressed it very well!
pay to write papers pay to have an essay written order essay papers
Incredible plenty of very good tips.
pay for a paper buy essay now online essays for sale
Regards, Very good stuff.
best place to buy essay https://quality-essays.com/ pay for term paper
Helpful material. Many thanks!
phd research proposals https://dissertationwritingtops.com/ dissertation services usa
Very good info, Thank you!
dissertation order dissertation help uk online dissertation writing service
Cheers. Numerous content.
writing a dissertation introduction https://dissertationwritingtops.com/ dissertation introduction help
Wonderful material. Regards.
uk dissertation help buy dissertation proposal buy dissertation online
Beneficial information. Kudos!
writing an essay help help writing college essay the help essay
You actually reported it superbly.
help me to write an essay https://englishessayhelp.com/ essay help australia
With thanks, Loads of advice!
best websites to do my homework for me do my sociology homework do my sas homework
Incredible a good deal of awesome tips.
pay me to do my homework https://homeworkcourseworkhelps.com/ coursework writing
Good forum posts. Appreciate it!
apps that help write essays help with essay writing for university help write my essay
Great postings, Appreciate it!
how can i do my homework faster https://homeworkcourseworkhelps.com/ can someone do my homework
Truly many of useful info.
buy dissertation paper white paper writing service research paper apa format paper writing service
Regards. Quite a lot of posts.
monthly paper writing service https://service-essay.com/ buying papers online college
Truly a good deal of superb material.
i refuse to do my homework how do you say i did my homework in spanish how do i get my child to focus on homework
You actually stated that terrifically.
check paper for plagiarism online free custom writing service https://service-essay.com/ reliable service thane paper writing reviews
You definitely made the point!
phd.proposal best site to buy research paper practical proposal
Incredible a lot of valuable advice!
term paper help online https://ouressays.com/ a paper proposal
You have made your point!
write my paper for money write my apa paper for me who can i pay to write my paper
Truly a good deal of great facts!
research proposal https://ouressays.com/ research project proposal
You said this fantastically.
legitimate paper writing services college paper writing service reddit custom written college papers
Valproic acid may harm an unborn baby buy cialis canada pharmacy Monitor for any unexpected abnormal uterine bleeding
Thank you, Loads of data.
cheap term paper writers https://essaypromaster.com/ english paper writer
You said it nicely.!
music essay writing service online assignment writing service fast essay writing service
You expressed that perfectly.
i don’t want to write my paper https://essaypromaster.com/ do my research paper
Incredible plenty of helpful tips.
research project proposal where to buy term papers online custom written term papers
You actually reported that effectively.
online writing evaluation service https://topswritingservices.com/ essay writing practice
Many thanks! Lots of data!
essay writing help online https://topswritingservices.com/ best custom writing service
Terrific write ups. Many thanks!
how to write an about me section for a website writer of geographical essay book professional essay writers for hire
Beneficial info. With thanks.
order paper online how to write a conclusion for a research paper pay to write papers
Regards. Useful information!
thesis about food service management pdf https://writingthesistops.com/ article thesis
Appreciate it, Numerous stuff!
writing a great thesis https://writingthesistops.com/ thesis on service quality in higher education
Tips well utilized..
i cant write my college essay college essay writer why do i love my parents essay
Amazing quite a lot of useful info.
write my java program for me https://essayssolution.com/ what should i write my persuasive essay on
Nicely put. Kudos.
outline writing service writing a college admission essay music essay writing service
You reported this adequately!
who will write my paper for me https://essayssolution.com/ help me write an essay for free
You actually suggested it really well.
cheapest essay writer https://theessayswriters.com/ automatic essay writer
You made your point pretty clearly..
thesis and hypothesis thesis paragraph paragraph thesis
You said it nicely.!
essay writier https://theessayswriters.com/ how to write my essay
Kudos. Terrific stuff!
what should i do my persuasive essay on pro essay writer who can i pay to write my paper for me
Really lots of helpful tips.
write my essay canada write a speech for me write your essay
Appreciate it. Numerous advice!
can someone write my essay essay on how do i spend my summer vacation do my essay online free help me write a cover letter for a job
best essay writing service 2016 will writing service manchester book blurb writing service cv writing service for it professionals
the best essay writer https://essaywritingservicetop.com
You actually expressed it exceptionally well!
how to write an scholarship essay https://researchproposalforphd.com best website to buy essays https://theessayswriters.com
Thanks. Plenty of forum posts.
mba dissertation help help writing dissertation proposal mathematics dissertation help dissertation help co uk review
Many thanks. Numerous write ups.
write my essay write my essay online cheap write my university essay uk do my essay do my essay
Cheers! Lots of information.
sat essay writing help https://essaywritingserviceahrefs.com cheapest article writing service https://essaywritingserviceahrefs.com
Wonderful stuff, Kudos!
pay to get essays written essays for sale online paying someone to write an essay essay order of organization
Factor well applied!.
college application essay help https://argumentativethesis.com custom assignment writing service https://englishessayhelp.com
Regards! A lot of info.
website that will write a paper for you research paper writer services best paper writer paper writing service
You said that superbly!
write college essay https://payforanessaysonline.com help on essay https://writingthesistops.com
Perfectly expressed of course! .
how to write an essay for graduate school https://essaywritingservicehelp.com how to write a movie in an essay https://domycollegehomeworkforme.com
Very good postings. Many thanks.
social interaction hypothesis doctor thesis term paper thesis 3 point thesis statement
Cheers, Helpful information!
cv writing service essay writers service last minute essay writing service essay writing service article
writer paper custom paper writer how to write a science paper academic paper writers
essay about service https://theessayswriters.com
You definitely made your point!
how to write a contrast essay https://cheapessaywriteronlineservices.com website that write essays for you https://buycheapessaysonline.com
You said it very well..
coursework writing service uk i didn t do my homework because activities how to get my son to do his homework should i do my homework quiz
Excellent write ups. Thanks!
dissertation experts uk writing a phd dissertation buy dissertation papers dissertation online help
hsbc premier will writing service english writing editing service best essay writer service argumentative essay writing
how to write a visual analysis essay https://ouressays.com
You expressed it superbly.
how to be a good essay writer https://hireawriterforanessay.com speech writing help https://bestpaperwritingservice.com
Thanks a lot. A lot of content.
reserach proposal survey proposal research proposal for phd writing dissertation proposal
Many thanks, I enjoy it.
are essay writing services safe history essay writing service essay writing courses online free top essay writing services reviews
Many thanks! Excellent information!
dissertation chapters https://essaywritingservicelinked.com how to write a self evaluation essay https://essaywritingservicetop.com
Terrific posts. Regards.
narrative essay writer fast essay writer paid essay writer what kind of writer are you essay
Seriously quite a lot of valuable advice.
essays on writing by writers https://essaywritingservicebbc.com best essay writing service canada https://ouressays.com
Many thanks! Plenty of posts!
buying dissertation help with dissertation phd proposals help writing your dissertation
argumentative essay writing essay writers service the cheapest essay writing service sat writing essay
dissertation for phd https://domycollegehomeworkforme.com
Failure of protein kinase A mediated phosphorylation and activation of CFTR Cl channels accounts for most of the clinical manifestations of CF, which can include airway disease, pancreatic failure, meconium ileus, male infertility, and elevated levels of salt in sweat 20, 136 cialis online without He has problems with skin and ear infections so we are the vet really often
Fantastic tips. Kudos!
cheap dissertation writing https://studentessaywriting.com what is college essay https://studentessaywriting.com
You have made your position very effectively!.
online paper writer best research paper writers write my philosophy paper for me write my college papers for me
This is nicely put. .
dissertation proposal writing services dissertation help glasgow dissertation uk help writing a dissertation proposal
Whoa loads of great tips!
writing essay for scholarship https://payforanessaysonline.com steps to writing a persuasive essay https://domycollegehomeworkforme.com
You actually expressed that really well!
thesis statement sentence thesis writing service online psychology thesis good thesis
Fantastic data. With thanks.
writing college essay https://helpwithdissertationwriting.com how to write the introduction of an essay https://essaywritingservicetop.com
You revealed this wonderfully!
which essay writing services are good writing an essay meme best literature review writing service do custom essay writing services work
show my homework to do list forgot to do my homework pay someone to do my math homework coursework website
what is the meaning of dissertation https://essaywritingservicetop.com
Regards, Loads of forum posts.
website content writing https://writinganessaycollegeservice.com national junior honor society essay help https://writeadissertation.com
You actually mentioned it fantastically.
websites to type papers writer paper essay writer review paper write
Reliable facts. With thanks.
college level thesis statements master thesis writing service uk phd thesis dissertation thesis for an essay
pay someone to write my essay geographical essay book writer name write my essay for me reviews do my essay online
scientific dissertation https://essayssolution.com
Superb posts. Thank you!
professional writing company https://essaypromaster.com i need someone to write my essay https://writinganessaycollegeservice.com
Incredible a good deal of very good advice.
dissertation guidelines https://bestonlinepaperwritingservices.com how to write a short story essay https://essaywriting4you.com
Regards! Numerous write ups!
i didn t do my homework form my posse don t do homework book do i write my questions down for homework to do my homework
You said it nicely..
essay writting oxford essay writing service essay writing military resume writing service
You have made the point.
essay writer no plagiarism term paper writer do my papers cheap research paper writers
Thanks, Terrific information!
writing a dissertation methodology https://helptowriteanessay.com how to write college application essay https://writeadissertation.com
Thanks, I enjoy it.
help with nursing essays need essay help national honor society essay help help with writing a paper
With thanks. I value it.
master thesis writing service https://bestmasterthesiswritingservice.com find dissertations https://buyanessayscheaponline.com
Good information. With thanks.
how to write a college essay paper https://writingthesistops.com how to write the best essay ever https://writingpaperforme.com
You expressed this adequately!
top essay writing best statement of purpose writing service research paper writing services which is the best resume writing service in india
using a paper writing service best paper writing service reddit writing paper services cheap online paper writing service
conclusion for college essay https://helpwithdissertationwriting.com
You actually expressed that really well.
writing an informative essay about a utopia custom lab report writing service writing a personal essay research proposal writing service uk
research paper writing services write a proposal paper pay someone to write my research paper write a proposal for a research paper
how to write a discursive essay https://essaywriting4you.com
Appreciate it! Plenty of advice.
write my essay for me free essay about myself as a writer how to introduce a writer in an essay write essay for me online
Superb content. Regards!
uf college essay https://dissertationwritingtops.com dictionary dissertation https://customthesiswritingservice.com
You’ve made the point!
thesis writing services https://buyanessayscheaponline.com business plan writers nyc https://writeadissertation.com
With thanks, I enjoy this.
english writing editing service nursing essay writing essay writing personal statement writing service
With thanks! Helpful information!
writing a narrative essay about being judged quizlet best paper writing service reddit last minute essay writing service medical thesis writing service india
Nicely put. Cheers.
coursework help uk do my microeconomics homework you can be my teacher i ll do homework i keep forgetting to do my homework
Many thanks. I value it!
best resume writing services for teachers https://cheapessaywriteronlineservices.com writing doctoral dissertation https://cheapessaywriteronlineservices.com
Thanks a lot! A lot of material!
dissertation definition dissertation to buy dissertation methodology buy masters dissertation
research paper writers for hire essay writer no plagiarism find someone to write my college paper write my paper in 3 hours
essay writing pdf https://helpmedomyxyzhomework.com
Valuable knowledge. Many thanks!
writing a good persuasive essay https://essaywritingserviceahrefs.com creative writing essays https://homeworkcourseworkhelps.com
You actually mentioned this perfectly.
write a resume for me i don’t want to write my essay write my philosophy paper for me help me write a profile for a dating site
Nicely put, Thanks a lot!
professional essay writing service https://helpwithdissertationwriting.com best resume writing services nj https://bestcheapessaywriters.com
cialis 10mg Our Idaho Fertility Center team is ready to help you with your efforts to conceive
You explained it fantastically.
do my math homework for me free do my homework assignment do my homework in spanish can i get paid to do my homework
You explained it perfectly.
english paper writing help quick essay help medical school application essay help apps to help write essays
Tips certainly considered!.
cheap essay writers https://essayservicehelp.com writing dialogue in an essay https://researchproposalforphd.com
Awesome forum posts. With thanks.
psychology thesis topics part of a thesis rogerian argument thesis analytical thesis statement
dissertation writing ut dissertation dissertation definition top 10 dissertation writing services
good books to write essays on https://argumentativethesis.com
Terrific postings. Kudos.
buy an essays https://essaywritingservicehelp.com professional essay writing help https://essaytyperhelp.com
Kudos, A good amount of knowledge!
how to write a reflection paper online essay writer writer paper cheap paper writers
Tips certainly applied!!
who can write my essay for me https://researchproposalforphd.com online essay editing service https://writingthesistops.com
Truly lots of helpful advice.
buy a dissertation uk dissertation help online free help with dissertation online help for dissertation
Excellent tips. Thanks a lot.
how to write good college application essays https://cheapessaywriteronlineservices.com writing my essay https://theessayswriters.com
You suggested it really well!
dissertation writers help dissertation dissertation abstracts international cheapest dissertation writing services
Thanks. Good stuff.
college essay writers block https://essaywritingserviceahrefs.com dissertation schedule https://researchproposalforphd.com
Terrific posts, Thanks a lot.
essay introduction help essay helper online the help movie analysis essay apps that help write essays
Cheers. Excellent information!
dissertation plan dissertation abstracts international dissertation writers online dissertation services uk
Thank you. Ample advice!
steps to writing a essay https://essayssolution.com writing an introduction for an essay https://helptowriteanessay.com
Whoa many of useful material.
service quality in hospitality industry thesis developing a good thesis thesis genorator good thesis statement examples for community service
cheap essay writing service online cheap paper writing service writing essays services best paper writing services
help in writing essays https://essaywritingservicetop.com
Cheers, I appreciate this!
thesis for https://bestcheapessaywriters.com how to write a 500 word essay about yourself https://custompaperwritersservices.com
Thanks a lot, I enjoy this.
termpaper purchase research papers online custom research paper purchase research paper online
Many thanks. A good amount of write ups!
help writing an essay for college write my essay for free what do i write my college essay on can someone write my personal statement for me
Kudos! Plenty of write ups.
essay writing basics https://essaywritingservicetop.com write a college essay https://essayssolution.com
Wow lots of beneficial material!
best man speech writing service uk essay writing service article linkedin profile writing service best man speech writing service uk
pro essay writing service reviews writing a business plan service best essay writing service yahoo best military to civilian resume writing service
harvard college essay https://essaywritingserviceahrefs.com
With thanks! Quite a lot of information!
how to write a good college essay https://buyanessayscheaponline.com us essay writing service https://englishessayhelp.com
With thanks, I like this!
help writing college essays i need help with my college essay essay help websites help for writing essays
You stated it superbly.
difference between highschool and college essay https://helpwritingdissertation.com write thesis https://bestpaperwritingservice.com
Whoa tons of beneficial data!
how do you say do my homework in spanish do my homework excel i don t want to do my homework can someone do my homework college
Very well spoken really! .
why i want to go to college essay https://hireawriterforanessay.com how to write a comparison essay https://buyanessayscheaponline.com
Really loads of excellent knowledge.
dissertation writing services uk writing help dissertation websites dissertation support services
pay to write my essay pay for paper where can i buy a college essay buy a essay
writing an explanatory essay https://bestpaperwritingservice.com
With thanks! Ample advice.
college admission essay help app that help with essay essay helpers essay on helping someone
Lovely material, Thanks!
hiring a freelance writer https://essaywritingservicehelp.com undergraduate dissertations https://domycollegehomeworkforme.com
This is nicely put! .
buy dissertations online dissertation def best dissertation writing service reviews help with phd dissertation
Really a lot of great material.
writing a proper essay https://essaywritingservicelinked.com common college application essay prompts https://writeadissertation.com
Thank you, A good amount of advice.
college admissions essay writing service essay writing service quick writing a narrative application essay online college paper writing service
Truly plenty of useful info.
essay checking service https://essaytyperhelp.com how to write a lit essay https://essaytyperhelp.com
Cheers, Awesome information!
do my homework for money did not do my homework sheet just do my homework pay someone to do my homework high school
Helpful postings. Many thanks.
the thesis is https://theessayswriters.com how to write mba essays https://buyanessayscheaponline.com
Tips certainly used!.
help with my essay english essay writing help help writing essays for college introduction essay help
Regards, I enjoy it.
ieee paper writing service pay for papers paper writer services buying papers online college
Awesome material. With thanks!
order cheap essay https://writinganessaycollegeservice.com critical writing essay https://phdthesisdissertation.com
Thanks a lot. Valuable stuff!
write my paper for cheap online paper writer paper writers write my paper website
thesis and dissertation writer service good thesis for a research paper psychology thesis thesis statement setup
how to write a creative nonfiction essay https://buycheapessaysonline.com
Thanks, I appreciate this!
how to write essay about myself https://helpwritingdissertation.com write your essay for you https://essayssolution.com
With thanks! Quite a lot of tips.
psychology dissertation statistics help phd.proposal write my dissertation for me law dissertation writers
tentative thesis phd thesis proofreading service australia thesis satement america’s premier dissertation and thesis service
essay help sydney https://theessayswriters.com
You said it perfectly..
thesis dissertations https://helpwritingdissertation.com online essay writing service review https://essaywritingserviceahrefs.com
Thanks a lot. I enjoy it.
writing helperessay help help write an essay paper writing help help writing a argumentative essay
Terrific info. With thanks!
do i need a title for my college essay write my capstone paper for me how to write an essay about my dream how to write an about me for website
You stated this very well!
how to make a college essay https://helpmedomyxyzhomework.com college admission essay https://essaytyperhelp.com
Very good info. Cheers.
argumentative essay writing non profit resume writing service mba resume writing service custom essay service
published dissertations online phd thesis writing abstract for dissertation help with my dissertation
affordable ghostwriters https://writingthesistops.com
Tips nicely used!.
do my college homework do my math homework reddit i can t do my math homework help do my homework
Amazing a good deal of superb information!
pay to have essay written pay for a research paper order cheap essay online cheap essays to buy
You actually reported that fantastically.
write a narrative essay for me write my essay now essay writer reddit research essay writer
Regards, Ample info.
pay someone to do your research paper buying essay papers buy a custom essay pay to write paper
online coursework do my algebra homework answers do my homework cheap do my computer science homework for me
how to write a comparison contrast essay https://researchpaperwriterservices.com
Good info. Thanks!
write my essay cheap do my essay free can someone write my essay for me professional essay writer
Thank you. Numerous information!
writing successful science proposals research proposal objectives parts of a research proposal reserach proposal
Appreciate it. Plenty of data!
american essay writing service online college paper writing service essay writing writing services for essays
Really all kinds of helpful information!
paper writing services writing a scholarship essay 24 hour essay writing service essay writing contest
essay writer free online introduce yourself as a writer essay write my essay paper for me write my college admissions essay
write essays for scholarships https://buyanessayscheaponline.com
Thanks. Excellent information!
pay for essay paper order essay papers can you pay someone to write an essay best website to buy essay
Very good material. With thanks.
fake essay writing service online assignment writing service essay help service grad school essay writing service
Great advice. Thanks a lot!
is cheap writing service legit one on one resume writing service writing essay service which essay writing service is reliable
research paper writing services in india writing term papers for money introduction of proposal letter custom research paper writers
how to write narrative essays https://ouressays.com
Great tips. Thank you.
writing dissertation tips phd research proposal writing service dissertation only phd writing dissertation
Thanks, Numerous tips!
write my essay online write and essay for me can you write a letter for me hire someone to write essay
Great posts. Appreciate it.
paper writing help essay helper free high school essay writing help national honor society essay help
Nicely put. Kudos!
help with an essay i need help with my essay argumentative essay essay help site edu
irving i ll write the song you sing for me i need an essay written for me write an essay essay for me
writing service https://writingpaperforme.com
Good forum posts. Cheers!
thesis correction service thesis statement beginning words the perfect thesis statement thesis formatting service malaysia
Truly tons of helpful information.
help to write an essay the help movie review essay helping people essay mba essay help
Whoa many of excellent advice!
online essay writing service uk free essay writing service uk custom writing service the best custom essay writing service
Info nicely taken!.
graphic design resume writing service macmillan will writing service will writing service southampton paid essay writing service
homework 123 where can i do my math homework online do my writing homework coursework writer uk
thesis assistance https://argumentativethesis.com
This is nicely expressed. .
write my essay for me cheap write my essay for money do essay for me did john legend write all of me for his wife
Fantastic knowledge. Thanks!
dissertation question help dissertation only phd literature review dissertation help define dissertation
Thanks a lot! Quite a lot of knowledge.
top paper writing services custom paper service paper writing service for college student professional research paper writing service
thesis in an essay top thesis writing service review biology thesis writing service perfect thesis statement
write my annotated bibliography https://phdthesisdissertation.com
Thanks! I enjoy it.
custom dissertation services uk dissertation writing theses and dissertations online dissertation consulting
Many thanks, I enjoy it!
dissertation help services need help writing a dissertation dissertation writing service completing your qualitative dissertation
You’ve made your position quite clearly..
dissertation consulting dissertation conclusion help writing an abstract for a dissertation dissertation help glasgow
Amazing content. Regards!
best dissertation phd writing service what is a phd best dissertation editing services
writing essay services student essay writing essay writing sites reputable essay writing services
how to write a critical evaluation essay https://custompaperwritersservices.com
Nicely put. Regards!
college paper writing services buy essay online writing service essay writing samples best resume writing service for veterans
Superb facts. Thanks!
can i pay someone to do my essay for me help me to write my essay write my essay for me website writes essays for you
Lovely facts. Many thanks!
custom dissertation writing help online dissertation writer online dissertation help veroffentlichen dissertation paper
pay for writing essay buying university essays pay for essay to be written order cheap essay
writing a college essay about yourself https://writingthesistops.com
This is nicely said! !
write essay easy essay writer write a resume for me custom essay writers
Thank you. Fantastic information!
write my essay for me no plagiarism my favourite writer short essay essay writer no plagiarism do my essay for me fast
Fantastic stuff. Thank you.
term paper help help writing term papers term paper for sale term paper research
Wow a lot of terrific info.
research term paper apa proposal best buy research paper research paper writer
writing papers write my philosophy paper writing paper paying someone to write a paper
hiring writer https://bestonlinepaperwritingservices.com
Kudos, I appreciate this!
essay writing service dublin appellate brief writing service top essay writing services us dissertation writing service
Truly all kinds of useful material.
thesis statement for a literary analysis informative essay thesis statement thesis literature review customer service pdf thesis
You stated it fantastically!
essay writer reddit https://studentessaywriting.com write your essay for you https://essaywritingservicebbc.com
Regards. Ample tips!
cheap dissertation help proposal writing services phd dissertation writing service dissertation editing services reviews
Wow a good deal of very good advice.
college essays for sale https://studentessaywriting.com pay to write my essay https://helpwritingdissertation.com
Kudos, Numerous data.
write my essay in 6 hours how to write an essay about my dream what should i write my college essay about
Fine knowledge. Appreciate it.
buy essay cheap buy cheap essay online
Truly all kinds of great tips.
cheapest essay writer writing my essay help i can t write my essay
Really lots of awesome tips.
real money online casino texas best casino online real money vegas casino online eu
Cheers! Ample facts.
college papers for sale professional paper writer essay writer free write my research papers
phd proposal write my research paper proposal thesis buying research papers
how to write an essay proposal https://essaywritingservicetop.com
You stated it terrifically.
the best essay writing service buy essay writing service writing services for college papers college essay writing help
Very good material. Appreciate it!
pay someone to write your paper cheap custom papers custom papers online customized writing paper
coursework writing service i didn t do my homework form do my homework in spanish coursework writing services
essay 123 help https://writingresearchtermpaperservice.com
Appreciate it. Numerous posts!
domyessay write my essay for cheap help me write my english essay what website writes essays for you
You have made the point!
do my homework cheap do my accounting homework do my accounting homework coursework uk
Nicely put. Regards!
tentative thesis argumentative essay thesis good thesis statements thesis binding
termpaper cheap research paper writing service buy a term paper project proposal introduction
best college essays ever written https://domyhomeworkformecheap.com
You said it nicely..
essay writing services paper writing services wikipedia writing service essay writing service uk forum
You reported that well.
essay paper writing services professional essay writing essay writing company smart writing service
paper writing services reviews buying college papers online cheap custom papers research paper writing service reviews
best online essay writers https://writingpaperforme.com
Truly loads of great advice.
online essay writer paid essay writers write an essay for me free essay writers online
You said it nicely.!
write a paper write papers for me how to write a response paper write research paper for me
paper pay custom writing paper service american paper writing service pay to write a paper
dissertation help reviews https://essaywritinghelperonline.com
Fantastic stuff. Regards!
buying a research paper for college essay proposal write my research paper for me online research paper writer
Whoa all kinds of amazing info!
college papers writing service term paper writing service paper writing service paper writing service reddit
Nicely put. Thanks a lot!
pay for research paper buy argumentative essay online buy an essay paper online pay for essay papers
research paper writer buying a research paper for college elements of a research proposal writing research proposal
purchase dissertation https://custompaperwritersservices.com
Nicely put, Thanks.
urgent essay writing service writing a persuasive essay best resume writing service reddit essay writing company
who can do my essay make an essay for me a writer should revise an argumentative essay for ideas and my essay writer login
effective college essays https://essaywritingservicetop.com
Many thanks! Wonderful stuff!
essay writing practice writing an essay introduction writing services for college papers trusted essay writing service
Many thanks. Plenty of posts!
help writing an essay for college easy essay writer academic essay writer do my essays
best finance essay writing service essay service reviews best cheap essay writing service writing a narrative essay
how to write a good cause and effect essay https://topswritingservices.com
Amazing content, Thanks a lot!
college essays writing best online essay writing service paper writing services for college students top essay writing service
dissertation assistance nursing dissertation dissertation writing help cheap dissertation help in los angeles
essay writing services reviews https://domyhomeworkformecheap.com
Factor nicely regarded.!
essay writing prompts cv writing service college application essay writing service essay writing
Reliable information. Many thanks!
nursing dissertation writing services data analysis dissertation help dissertation consultants thesis dissertation
Nicely put, Thank you.
write my term paper the proposal online buying research papers proposal research
You made your stand quite effectively!!
what should i write my college essay about quiz what should i write my college essay about help me write my scholarship essay essay writer hire
do my writing homework why cant i do my homework pay to do my homework reddit do my homework
harvard college essay https://dissertationwritingtops.com
You actually said it very well.
pay to write essay where can i pay someone to write my essay buy essay for college buy an essay paper online
Thanks a lot! Plenty of data!
thesis paper thesis statment thesis writing service reviews thesis writing service uk
With thanks, I enjoy this.
essay writing service oxford college paper writing service professional essay writing writing an essay
Thanks, Great information.
a good thesis statement thesis research master thesis writing service uk thesis writing service uk
Cheers. Terrific stuff.
legit paper writing services paying someone to write a paper research paper writing services reviews buying papers for college
essay writer review essays for me write my essay for free writing my essay
should college essays be double spaced https://domycollegehomeworkforme.com
Incredible lots of wonderful material!
research paper writing service cheap custom essay writing services legit essay writing services write essay service
Nicely put. Thank you.
best dissertation writing service review phd proposals nursing dissertation help custom dissertation writing service
You actually suggested this adequately!
help writing essay essay helper online best essay writing service essaytyper
This is nicely said. !
write this essay for me write my research paper for me online essay writers write my essay online
Good write ups. Kudos!
dissertation abstracts international what is a phd dissertation abstract phd thesis
You made your point!
dissertation abstracts international dissertation writing services reviews buy dissertations dissertation writing services reviews
Effectively expressed of course! .
a thesis statement thesis titles thesis statement meaning thesis proposal example
define thesis statement example thesis good thesis a thesis
researching and writing a dissertation https://helptowriteanessay.com
Incredible tons of very good knowledge.
write my paper write a paper paper writing services research paper writer services
Amazing write ups. Thanks a lot.
pay for essay where to buy essays online buy college essays pay someone to write my college essay
do my finance homework do my finance homework do my finance homework do my homework
thesis editor https://customthesiswritingservice.com
After reading your article, it reminded me of some things about gate io that I studied before. The content is similar to yours, but your thinking is very special, which gave me a different idea. Thank you. But I still have some questions I want to ask you, I will always pay attention. Thanks.
You actually explained it exceptionally well!
do my essay free automatic essay writer ai essay writer essay writer
Appreciate it. Quite a lot of information.
online paper writing service paper writing service pay someone to write paper paper help
Thanks! Fantastic stuff!
paper writing service reviews pay for papers custom handwriting paper paper help
dissertation editing services dissertation service dissertation help dissertation writers
dissertation introduction https://payforanessaysonline.com
Perfectly voiced certainly. !
writing services easy essay writing best resume writing service reddit essay writing sites
You stated this very well!
essay writer essay writer essays help help with my essay
You’ve made your point!
writing dissertations writing dissertations dissertation def dissertation assistance
dissertation writing dissertations dissertation writing help dissertation paper
how to write titles of books in essays https://bestpaperwritingservice.com
Superb posts, Cheers.
fast essay writing service admission essay services writing an informative essay best research paper writing service
Appreciate it, Ample tips!
coursework do my programming homework do my math homework for me pay someone to do my homework
Reliable information. Cheers!
thesis sentence thesis statment good thesis statements writing a thesis
tentative thesis define thesis statement thesis paper working thesis
college essay community service https://buyanessayscheaponline.com
You actually stated that fantastically.
paper writer services writers of the federalist papers pay for paper research paper writers
Your article helped me a lot, is there any more related content? Thanks! https://www.binance.com/pt-PT/register?ref=UM6SMJM3
Regards. I value it.
professional paper writing service best online essay writing services trusted essay writing service custom writing service
Seriously plenty of terrific info.
best essays writing service writing essay service essay writing tips unique essay writing service
dissertations online dissertation uk writing dissertation dissertation writing
how to write a essay about yourself https://helpwithdissertationwriting.com
Wonderful information. Thanks.
college paper writing service buying papers for college pay for college papers order custom paper
Incredible lots of beneficial information.
writing an essay outline fast essay writing service australian essay writing service essay writting service
Truly tons of beneficial material!
buying papers for college custom papers paper writer services college paper writing service
dissertation data analysis help dissertation def custom dissertation writing services dissertation help
how to write an essay about yourself https://domycollegehomeworkforme.com
Kudos. Awesome stuff!
pay for essay buy an essay online pay to write essay buy essays
With thanks, I enjoy it!
dissertation proposal dissertation service best dissertation phd weight loss
This is nicely said. .
pay for college papers pay for college papers pay for essays buy essay papers
buy college paper buying papers for college graduate paper writing service professional paper writing service
cheap essays online https://customthesiswritingservice.com
Truly plenty of great facts!
essay write service essay paper writing services australian essay writing service best college essay writing service
You explained that effectively!
pay for college papers college paper writing service professional paper writing service pay for papers
Superb postings, Kudos!
urgent essay writing service essay writing courses online free essay service review paper writing services legitimate
hire someone to do my homework xyz homework pay to do my homework homework help cpm
thesis graduate https://writeadissertation.com
You mentioned it very well!
write my essay for cheap do my essay free write my essays online write an essay for me
You said it nicely.!
professional paper writing services online paper writing service essay writing services legit essay writing service
Very good posts. Thanks!
do my math homework for me reddit do my homework do my finance homework reddit do my homework
cheap essay help helping others essay paper writing help argumentative essay
dissertation topics https://domycollegehomeworkforme.com
Beneficial postings. Regards!
cpm homework help xyz homework do my homework for free do my chemistry homework
Thank you! I appreciate this.
pay to write paper pay for an essay pay for research paper buy college essays
alphabay market link black market website
Thanks a lot, I value it!
write my essay online website that writes essays for you do my essay for me who can write my essay
You said it perfectly.!
thesis paper a good thesis statement working thesis thesis statement meaning
Thank you! Helpful information.
paperhelp essay writing help free writing assistant essay writing help
Perfectly expressed really. !
essay writer website pay someone to write a paper how to write a reflection paper pay someone to write a paper
Kudos. Lots of stuff!
dissertation editing services writing dissertation doctoral dissertation phd dissertation writing
Thanks! Lots of postings!
essay help college application essay help paperhelp medical school personal statement
darknet market comparison https://dark-market-heineken.com/
darknet markets list 2023 buying credit cards on dark web
shop ccs carding darknet market list reddit
decentralized darknet market drugs on the dark web
onion market darkmarkets
cypher market darknet darknet escrow
site darknet market deep net access
deep web link 2023 top onion links
darknet markets may 2023 darknet market oxycontin
This is nicely put! !
doctoral dissertation best dissertation writing a dissertation dissertation help
current darknet market darknet markets wax weed
dark web hitman deep web links 2023
where to find darknet market links redit darknet market onions
uk darknet markets tor market
darknet site darknet market wikia
darknet market package deep web links 2023 reddit
Point very well regarded!.
essay helper help with essay writing paper writing help essay helper
Cocorico Market link darknet stock market
darknet market sites and how current list of darknet markets
bitcoin dark web darknet stock market
search darknet markets top darknet markets 2023
black market prescription drugs darknet drug store
dark web markets 2023 australia dark markets macedonia
darknet dream market dark market url
darknet websites cvv black market
best onion sites 2023 dark web market place links
legit darknet markets darknet software market
darknet search engine url best dark web markets 2023
dnm xanax bitcoin cash darknet markets
deep web addresses onion dark markets belgium
what darknet markets are still up how big is the darknet market
Cocorico url buying on dark web
darknet drugs sales brucelean darknet market
history of darknet markets tor websites reddit
what darknet markets are still open onion domain and kingdom
black market websites tor dark markets russia
best darknet gun market verified dark web links
dark web hitman for hire Heineken Express Market
most popular darknet market darknet drug store
dumps shop asap market
cypher market darknet market google
asap market link dark web market list
litecoin darknet markets counterfeit euro deep web
deep web drugs exploit market darknet
top darknet market 2023 pink versace pill
the darknet drugs how to get to the black market online
what bitcoins are accepted by darknet markets dark web poison
darknet market xanax buying things from darknet markets
best website to buy cc dark markets peru
versus project market darknet market lightning network
best darknet markets 2023 cp links dark web
deep web link 2023 what darknet markets sell fentanyl
darknet market links dark markets lithuania
how to access darknet markets reddit darknet market list
the dark web links 2023 top darknet drug sites
darkmarket website reliable darknet markets
credit card dark web links black market website names
i2p darknet markets alphabay solutions reviews
darknet drugs sites ethereum darknet markets
darknet market noobs step by step bitcoin darknet drugs
outlaw darknet market url dark markets finland
buying drugs online dark markets belgium
reddit darknet markets uk black market net
darknet drug market dark markets south korea
darknet wiki link black market website legit
dark web sites darknet market links safe
bohemia market tor market links
anadrol pills drugs dark web price
deep web software market darknet drugs malayisa
deep dot web replacement darknet markets up
market street darknet xanax darknet reddit
dread onion top ten dark web
dark web fake money black market bank account
escrow dark web deep web drug prices
buying drugs online drug market
dark net markets crypto darknet drug shop
tor markets links darkshades marketplace
darknet market alternatives darknet markets may 2023
darknet illegal market darknet drug markets
buy drugs on darknet what are darknet drug markets
how to anonymously use darknet markets vice city market
vice city market url escrow dark web
best onion sites 2023 dark web links market
reddit onion list onion directory 2023
how to buy drugs on darknet vice city link
cypher market darknet how to access the darknet market
shop ccs carding darknet drugs germany
darknet drug links reddit darknet reviews
darknet best drugs new alphabay darknet market
how to use onion sites dark markets monaco
darknet drugs germany darknet guide
adresse onion black market deepdotweb markets
dark web in spanish Abacus Market
dark web address list how to buy things off the black market
dark markets bolivia versus project darknet market
dark web steroids alphabay market darknet
history of darknet markets hidden financial services deep web
biggest darknet market darkfox link
crypto market darknet darknet market steroids
dark markets liechtenstein google black market
dark web prepaid cards reddit credit card black market websites
dark markets 2023 drugs on the deep web
hidden marketplace drug markets onion
australian darknet vendors best darknet market for weed
dark markets hungary most popular darknet market
florida darknet markets onion link search engine
dark web market place links reddit working darknet markets
tor markets i2p darknet markets
biggest darknet markets biggest darknet markets
biggest darknet markets dark net markets
You said it adequately.!
custom research paper writing services buy a paper pay someone to write your paper graduate paper writing service
You said it very well.!
what is the best essay writing service writing a persuasive essay legitimate essay writing service essay writing service blog
uk darknet markets what darknet markets are available
darknet illicit drugs dark markets bolivia
darknet markets with tobacco best dark web links
dark web shopping dark web sites xxx
current darknet market list darknet drugs germany
fresh onions link darknet selling drugs
asap url dark web live
buying from darknet market with electrum how to buy from the darknet markets lsd
darknet dream market link dynabolts pills
darknet market alaska dark markets ireland
deep web weed prices drug trading website
deep web canada which darknet markets are up
darknet black market dark web escrow service
darknet markets reddit 2023 dark web prostitution
buying credit cards on dark web darknet dream market reddit
dark web payment methods darknet search
dark markets luxembourg tor market links
how to get on the dark web reddit darknet market list 2023
how to buy from darknet markets darknet black market
darknet dream market reddit how to access the black market
what darknet market to use now deep web links updated
dark markets luxembourg reliable darknet markets
dark web shopping how to use onion sites
dark web shop tor link search engine
buying from darknet market with electrum darknet search
Abacus Market link dxm pills
best darknet markets 2023 darkmarket website
black market alternative current list of darknet markets
dark market link french deep web link
dark web markets 2023 darknet serious market
dark markets romania project versus
dark web drugs ireland dark markets norge
dark markets norway biggest darknet market
black market net incognito market link
ordering drugs on dark web top darknet market now
penny slots for free live casino slots lona wms slots free online free reel slots online
darknet markets working links buying drugs on darknet reddit
darknet markets ranked 2023 what darknet markets are up
tormarket onion popular darknet markets
decabol pills dark web payment methods
deep web directory onion darknet market
drugs onion darknet market controlled delivery
top 10 dark websites darknet market carding
how to get on darknet market deep web updated links
reddit darknet market deals dark web directory
darknet markets up alphabay link
tma drug outlaw market darknet
darknet market google onion deep web search
darknet illegal market dark markets uruguay
search deep web engine darknet market oz
reddit darknet market deals dark web step by step
dark markets moldova black market alternative
current darknet market market links darknet
monero darknet market buying darknet drugs
tma drug darknet market get pills
darknet drugs guide reddit biggest darknet market place
dark web payment methods tfmpp pills
darknet market alphabay what darknet markets sell fentanyl
onion linkek buy bank accounts darknet
tor market links 2023 decentralized darknet market
shop online without cvv code dark markets bosnia
tor market list onion deep web search
darknet markets norge darknet market package
asap market darknet deep web links reddit
which darknet market are still up illegal black market
darknet stock market reliable darknet markets reddit
deep web markets how to get to the black market online
tor market links 2023 asap link
cp onion dark net market list reddit
russian darknet market pink versace pill
new alphabay darknet market dark markets ireland
best darknet markets guns dark market
what is the best darknet market active darknet markets
top darknet market 2023 top 10 dark web url
best dark web counterfeit money darknet drugs sales
dark markets estonia bohemia url
darknet markets may 2023 asap darknet market
tfmpp pills darknet markets guide
marijuana dark web monero darknet markets
how to buy drugs dark web darknet links markets
reddit darknet market how to darknet market oxycontin
darknet drug market list black market online website
darknet websites list 2023 dream market darknet url
darknet market links safe darkweb market
cannabis dark web darknet drug trafficking
deep web drugs archetyp market darknet
hidden financial services deep web dark web uk
dark web market place links shop ccs carding
dark markets united kingdom darknet reddit market
deep web drug prices new darknet markets
superlist darknet markets good dark web search engines
alphabay market onion link best darknet market australia
best black market websites darknet market avengers
You actually said that adequately.
write essay persuasive essay writer essay writer review essay writer website
darknet markets dread drugs on deep web
which darknet markets are up wired darknet markets
darknet guide dnm market
Nicely expressed indeed. !
professional essay writers write an essay for me what should i write my college essay about make an essay
darknet markets with tobacco reddit darknet market australia
legit darknet sites dark web fake money
verified darknet market darknet market guide reddit
alphabay solutions reviews deep web deb
buy drugs from darknet best websites dark web
dark web address list darknet drugs india
alphabay url hacking tools darknet markets
dark markets usa versus darknet market
darknet black market sites tor darknet markets
buying drugs online dark web onion markets
darknet market noobs guide best website to buy cc
counterfeit euro deep web darknet new market link
deep web search engine url darknet live stream
dark web prostitution archetyp market link
tor drugs grey market link
deep net websites dma drug
buy bitcoin for dark web darknet drug vendors
what darknet markets are still up darknet market superlist
onion seiten best darknet market for weed 2023
sichere darknet markets 2023 alphabay link
which darknet markets are still open shop valid cvv
best darknet markets reddit dark web illegal links
dark web buy credit cards onion market
what is the darknet market site darknet market
credit card dark web links drugs darknet vendors
black market website legit how to get on the dark web on laptop
dark markets korea darknet markets may 2023
guide to darknet markets outlaw market darknet
darknet search engine dark markets iceland
black market online website best websites dark web
black market reddit deep web links reddit 2023
dark web in spanish darknet market google
new alphabay darknet market dark markets australia
darknet market lists brick market
darknet drugs best darknet markets
Cocorico darknet Market 2023 darknet market
darkmarket link tor markets 2023
darknet search engine dark web link
darknet seiten darknet site
deep web markets darkweb marketplace
deep web drug markets how to access dark web
drug markets onion tor markets 2023
blackweb official website dark web sites
tor market links dark web access
darkmarket 2023 darkmarket list
blackweb tor market links
tor dark web tor dark web
deep dark web dark web websites
deep web drug markets darknet drug market
deep web drug markets dark markets 2023
darkweb marketplace darknet market
dark web drug marketplace dark markets
dark web sites free dark web
deep dark web dark web sites
darkmarket dark web markets
tor dark web deep web drug store
how to access dark web darkmarket list
dark markets 2023 darknet seiten
darknet market list dark markets 2023
onion market deep web sites
darkmarket list darkmarket list
darknet market dark market onion
darknet market links tor marketplace
deep web drug store tor dark web
dark market url darknet seiten
dark web link dark web links
darknet market links dark web search engines
dark web sites dark web links
tor markets black internet
darknet markets dark markets
bitcoin dark web dark market url
tor market links deep web search
bitcoin dark web dark web search engine
darknet sites dark market list
deep web drug url darknet drugs
tor dark web dark web market list
dark web sites links dark internet
black internet dark web link
tor market black internet
darkweb marketplace dark market list
dark markets darknet market lists
tor market deep web markets
blackweb dark websites
darknet links tor dark web
bitcoin dark web tor dark web
darknet seiten deep web drug markets
dark web market list darknet drug links
deep web drug markets free dark web
darknet markets 2023 tor marketplace
tor markets dark web sites links
dark web sites darknet market
darknet seiten dark market link
darknet sites tor darknet
darknet links darknet search engine
tor darknet deep web markets
dark web link darknet markets
Great facts, Thanks.
pay for essay reviews pay for college papers pay for research paper buy an essay online
darkmarkets blackweb official website
dark internet dark web websites
darknet websites how to access dark web
dark market dark web websites
tor markets dark web market
darkweb marketplace how to get on dark web
darkmarkets dark websites
blackweb darknet market
darknet site deep web markets
Fine advice. Regards.
essay paper writing services coursework writing service writing an essay best essay writing service reddit
darkmarket url deep web drug url
darkmarket link tor marketplace
bitcoin dark web deep web links
darknet search engine dark web link
dark market darknet market links
dark markets 2023 best darknet markets
deep web search tor market
tor darknet deep web drug markets
dark web access dark web market links
bitcoin dark web deep web search
deep web drug links darknet market links
darknet drugs deep dark web
drug markets dark web darknet links
darknet market deep web links
how to access dark web darknet drug links
tor markets 2023 dark web links
dark web search engines best darknet markets
dark web link dark web links
deep web drug links darknet drug store
deep web sites darkmarket list
darknet drug store tor darknet
darknet search engine dark web sites links
deep web drug links drug markets dark web
tor market links the dark internet
darkmarkets darknet marketplace
darknet marketplace dark market
darknet site darknet links
tor market darknet sites
dark web drug marketplace dark markets 2023
dark web market list darkmarket 2023
darknet market darknet market links
blackweb dark web sites links
deep web sites dark market 2023
darkmarket list deep web drug links
darknet links darknet market
dark net tor market
dark web market links drug markets dark web
dark market tor markets
blackweb official website deep web drug markets
deep web drug url dark web markets
black internet how to access dark web
darknet drug store drug markets onion
darknet market links darknet websites
dark net darknet site
darkweb marketplace darkmarket link
tor dark web dark website
dark market darknet market lists
deep web drug url deep web markets
deep web drug url darknet links
tor market darknet market lists
deep web sites deep web sites
darkmarkets darkmarket url
dark market 2023 darkmarket list
onion market darkmarket 2023
dark web search engine deep web drug url
dark market url best darknet markets
darknet links darknet drug market
dark market 2023 darkmarket list
black internet deep dark web
dark websites darknet drugs
deep web drug url dark websites
dark web websites dark websites
dark web sites links the dark internet
dark web site darknet search engine
dark markets 2023 dark web site
dark web market links darkmarkets
tor marketplace dark web markets
darknet drugs tor market links
darkmarkets dark web market links
darknet markets dark web websites
bitcoin dark web tor marketplace
dark web markets dark web access
deep dark web darkmarket 2023
darkmarket url dark markets 2023
dark web search engine darknet market
dark websites drug markets dark web
deep web drug url darknet markets 2023
darkweb marketplace best darknet markets
darknet search engine drug markets onion
dark market link darknet sites
darknet drug links black internet
dark website dark web market
dark markets 2023 dark web access
dark web sites links deep web drug store
Thanks a lot. I appreciate it!
buy essay online order essay pay to write my essay pay for an essay
how to get on dark web deep web sites
drug markets dark web the dark internet
deep web drug store deep web drug store
deep web search deep web drug store
darknet markets 2023 onion market
darknet drug store dark web market
dark internet dark internet
dark web access how to access dark web
darkmarket link tor dark web
tor dark web darknet search engine
dark websites dark web search engines
how to access dark web tor market url
darknet drug store tor markets links
the dark internet dark internet
tor markets 2023 darknet marketplace
darknet drug market dark market list
Thanks a lot! Loads of facts!
cheap custom essay writing service online essay writing service writing a conclusion for an essay essay writing service uk
darknet sites dark web link
tor dark web darkmarket
deep web links darknet market lists
dark market dark net
dark market link dark websites
darknet websites dark markets
dark market darkmarket url
darknet markets 2023 dark market link
darkmarket list black internet
dark market url dark markets 2023
bitcoin dark web deep web search
darknet drugs onion market
deep web drug links darkmarket link
tor darknet how to get on dark web
darknet sites blackweb
tor market tor market url
darknet market links deep web markets
blackweb tor market
dark web sites links deep web sites
dark web websites darkmarket
dark web drug marketplace tor market
deep dark web deep web sites
dark web drug marketplace dark market 2023
dark market 2023 tor markets links
dark internet darkmarket link
best darknet markets tor markets links
best darknet markets dark web access
black internet dark market link
deep web drug store deep web links
dark market list drug markets dark web
how to get on dark web darkmarket
tor darknet dark markets 2023
tor markets links darknet site
deep web sites dark web search engines
darknet market dark web market links
darknet drug store darknet site
darkmarket dark web market
dark web sites how to access dark web
darknet drugs darknet websites
darkweb marketplace darkweb marketplace
dark net deep web search
dark web search engine deep web markets
deep web drug store dark web link
tor markets darkweb marketplace
tor markets links darkweb marketplace
darkweb marketplace deep web drug url
darknet market list darknet market links
blackweb official website dark web market
tor market darknet search engine
deep web search dark internet
blackweb official website darknet market links
darknet markets 2023 tor dark web
dark website dark market list
darknet markets darknet search engine
tor markets 2023 dark market url
deep web links dark market list
dark market 2023 deep web sites
dark markets deep web sites
tor markets 2023 tor markets links
the dark internet darkmarkets
how to get on dark web dark web site
dark web market drug markets onion
dark markets dark net
tor marketplace dark web sites links
dark websites dark web links
dark markets dark web sites links
dark market url darknet drug store
deep web drug url darkmarket list
deep web drug markets dark market url
deep web sites blackweb official website
dark web drug marketplace darkmarket link
dark market link deep web markets
dark web links dark market link
dark web drug marketplace darkmarkets
the dark internet dark web sites
tor markets how to get on dark web
dark web sites darknet market list
darknet market lists dark web search engine
dark markets dark market onion
drug markets dark web darknet sites
dark web link dark web links
blackweb the dark internet
deep web search best darknet markets
drug markets onion dark web link
darkmarkets deep web search
dark website deep web drug url
darknet drug market dark web access
tor dark web dark web link
You said it adequately.!
proposal writing buy a research paper online proposal elements of a research proposal
dark market list dark websites
bitcoin dark web deep web drug markets
dark market dark internet
darknet websites dark market 2023
darknet markets darkmarket link
free dark web dark market
deep web drug url darkmarkets
darknet market bitcoin dark web
dark web websites bitcoin dark web
darkmarket list tor darknet
dark internet dark web websites
dark web link darknet links
darknet markets tor markets links
how to get on dark web dark web market
darkmarket list dark web link
darknet websites tor marketplace
darknet drug store darknet drug market
best darknet markets darknet links
dark websites darknet market lists
tor markets deep web drug url
dark markets deep web drug markets
tor darknet deep web drug links
deep web drug url deep web drug store
tor market darkmarkets
darknet site darknet market list
deep dark web dark website
dark websites dark web access
darknet drug market dark market list
deep web drug markets deep dark web
dark markets 2023 blackweb official website
deep web drug links darknet drugs
dark web markets tor dark web
drug markets onion dark net
darkmarket url dark web market list
dark web link darkmarket 2023
the dark internet darknet marketplace
dark website dark net
darknet markets 2023 dark websites
black internet dark web access
deep web links darknet seiten
dark market url tor darknet
bitcoin dark web drug markets dark web
tor markets links dark web websites
deep web drug links dark market url
tor market dark web search engine
darkmarket black internet
free dark web deep web search
dark web access dark market 2023
dark web links darknet drugs
dark market onion dark market list
dark web markets dark market url
dark website deep web markets
deep web drug url best darknet markets
deep web drug url deep web drug url
deep web links dark web market links
dark web websites how to access dark web
dark net deep web sites
darknet market darknet seiten
how to access dark web darknet markets
dark market onion onion market
tor market url tor markets 2023
dark market list dark web sites links
dark market list dark web links
deep dark web dark website
tor darknet deep web search
dark web market darknet markets 2023
dark web markets dark web markets
dark markets 2023 darknet markets 2023
how to get on dark web darknet links
darkmarket 2023 darkmarket
dark internet darkmarket link
darknet websites darkmarket
dark net tor markets 2023
darknet drug market bitcoin dark web
dark market 2023 darkmarket 2023
darknet search engine dark internet
dark web link darknet websites
darknet drug links blackweb
deep web sites dark web markets
tor darknet tor market
darknet markets 2023 deep web drug links
darkmarket bitcoin dark web
free dark web dark web market list
tor markets darknet drug market
Thank you, I like it.
research paper help buy research paper parts of a research proposal proposal essay
dark web sites dark web search engine
darknet market lists the dark internet
dark market url how to get on dark web
dark web sites links onion market
tor markets bitcoin dark web
deep dark web dark markets 2023
dark market darkmarkets
darkmarket link dark web websites
darknet drugs darkmarkets
dark web markets drug markets onion
how to access dark web dark web market list
darknet drugs deep web search
darknet market list dark market url
darknet sites darknet market links
tor darknet tor markets 2023
darkmarket list darknet market list
darknet drug store dark web market links
blackweb official website dark web market links
tor darknet free dark web
darknet markets tor marketplace
blackweb official website dark market list
darknet sites tor markets links
tor market links darknet drugs
free dark web dark market url
bitcoin dark web darknet market lists
dark websites deep dark web
darknet sites darknet drugs
tor markets links blackweb official website
tor market darknet markets 2023
drug markets onion tor market links
dark web search engines darknet drug market
dark web websites darkmarket url
tor darknet onion market
Nicely put. Thank you!
pay for research paper pay someone to write your paper paper help order custom paper
dark internet drug markets dark web
darknet websites darknet markets
dark web drug marketplace deep web drug store
darkmarket link deep web drug markets
dark market list drug markets dark web
deep web drug url darkweb marketplace
tor markets 2023 drug markets onion
dark web links drug markets dark web
dark market onion dark web market links
deep web search dark web sites
dark web market dark market url
darknet drug store dark market list
darknet site black internet
darkmarket link blackweb official website
deep web links onion market
dark web sites links dark web access
tor darknet deep web drug markets
dark net dark net
dark web market list drug markets onion
dark website tor market links
dark web sites free dark web
deep web drug links dark web websites
deep web search dark market onion
dark market 2023 dark market link
dark market dark web sites links
darkmarket url darknet sites
dark web search engines dark market 2023
drug markets onion best darknet markets
deep web markets darknet seiten
dark market list dark web market list
dark web sites dark market link
darkmarket url dark web link
tor markets 2023 darknet search engine
dark web sites links bitcoin dark web
darknet drug store tor markets links
darknet drug store dark websites
dark market 2023 darknet drug market
drug markets dark web dark market link
dark web market links tor markets
tor market onion market
how to get on dark web dark web market
tor darknet tor market links
deep web drug store dark website
dark net tor markets 2023
dark markets dark web link
dark web access tor market
tor markets dark web access
darknet links darknet market list
dark web links how to get on dark web
dark web search engine dark web market links
black internet tor market links
drug markets onion tor marketplace
deep web markets tor markets links
dark market list dark website
dark web sites drug markets onion
the dark internet darkweb marketplace
darknet drug store onion market
darkmarket darknet links
dark web market links dark web market links
tor darknet tor markets 2023
darknet drugs dark market url
black internet dark market link
the dark internet deep web drug store
tor markets 2023 darknet markets 2023
darknet seiten dark market onion
drug markets dark web onion market
how to access dark web darknet drug links
darknet seiten darkmarket link
dark web market links drug markets dark web
how to get on dark web darknet search engine
darknet links deep dark web
deep web search dark website
tor darknet dark net
black internet dark market 2023
tor markets darknet drug links
darkmarket black internet
Really quite a lot of superb tips.
pay to do my homework do my finance homework do my finance homework homework help cpm
dark market list dark market link
dark web markets drug markets dark web
tor markets links tor darknet
dark internet darkmarket url
tor dark web dark web access
darknet drug store darknet drug links
dark web markets dark web search engine
dark net dark web links
darknet market deep web drug url
dark web drug marketplace deep dark web
dark web search engine tor markets 2023
tor market url black internet
best darknet markets dark market link
tor darknet dark web market
darknet market links dark web drug marketplace
dark market 2023 darknet market links
deep web search darknet links
darknet drug links tor market url
darknet seiten darkmarkets
deep web drug url black internet
darkmarket 2023 darknet drug links
darkmarkets darknet drug market
dark market list dark market
tor markets 2023 tor marketplace
tor markets 2023 deep web links
Whoa a good deal of superb tips!
best executive resume writing service application essay writing service essay writing service 3 hours cheap essay service
darknet market darkmarkets
how to access dark web tor markets 2023
dark web site dark web websites
deep web drug store darknet markets
darkmarket 2023 darknet drug links
dark web websites tor markets links
darknet websites the dark internet
how to access dark web blackweb official website
dark market darknet market links
deep dark web how to access dark web
tor market url deep web search
dark web site dark web drug marketplace
deep web drug url drug markets onion
tor market best darknet markets
darkweb marketplace dark web sites
free dark web darknet seiten
darknet websites darknet site
dark market 2023 dark net
dark market list how to access dark web
darknet drug market deep web drug links
tor markets tor market links
free dark web darkmarket list
how to access dark web dark market
dark web links deep web drug store
darknet market links tor market links
darknet marketplace darkmarket
dark net darkmarkets
dark web sites dark market url
darknet drug store tor market url
tor dark web dark web market links
darkmarkets blackweb
deep web drug links bitcoin dark web
darkmarket 2023 deep dark web
dark internet darknet websites
dark web markets dark website
tor markets deep web markets
tor marketplace deep web drug links
tor markets links bitcoin dark web
dark market onion darknet drug market
tor markets 2023 tor dark web
darknet seiten blackweb official website
deep web drug store darknet links
darknet markets darknet websites
deep web drug store darkmarkets
bitcoin dark web darknet sites
darknet marketplace tor markets
deep web drug markets best darknet markets
dark web websites darknet drug store
dark web search engine dark web sites
drug markets onion dark web link
darknet drug store darknet search engine
dark web search engines drug markets dark web
darkmarket link tor market url
darknet market lists black internet
dark market dark market link
darknet drug links darknet search engine
no deposit sign up bonus casino deposit bonuses casinos sites win real money online casino for free
dark web market list dark market onion
darknet marketplace dark web search engine
darknet drug market dark market
tor markets 2023 dark markets
darkmarket link deep web search
blackweb official website the dark internet
deep web drug links dark web market
tor market links dark web sites
darknet links dark web markets
dark web site darknet site
darknet drugs darknet links
the dark internet dark web market list
black internet darknet drugs
free dark web dark market url
darkmarkets dark internet
dark web access tor marketplace
darknet sites dark web site
dark websites dark web websites
dark markets 2023 tor markets 2023
With thanks, A lot of info!
parts of a research proposal proposal essay research paper helper proposal introduction
dark web link tor markets links
dark markets 2023 darknet websites
deep web drug links darknet drugs
darknet websites darknet market
tor markets links dark market
dark market list darknet drug links
darkweb marketplace tor markets 2023
dark web sites links tor markets
deep web drug markets darknet market lists
darknet search engine dark web sites links
darknet drug links dark web search engine
dark web site darkmarket link
blackweb official website dark market url
darknet market lists dark web market
deep dark web free dark web
how to access dark web deep web drug url
darknet drugs drug markets onion
darkmarket url dark market link
dark web sites links deep dark web
dark market onion dark web markets
the dark internet darkmarket 2023
how to access dark web darknet markets
tor market url darknet search engine
dark web link deep web search
deep dark web deep web drug markets
Many thanks. Numerous posts!
research paper writer research paper writing service proposal writing term paper help
darkmarket 2023 darkmarket link
dark web site dark web sites
dark net darknet market lists
dark web websites tor marketplace
deep web drug markets dark market 2023
dark web site darknet drug store
tor market darkmarkets
free dark web dark market url
dark market url dark web search engine
tor markets 2023 tor market url
darknet market dark markets 2023
dark web market links tor dark web
dark web market bitcoin dark web
dark web market list dark web market
the dark internet darknet drugs
deep web markets darknet websites
dark web drug marketplace deep web drug links
darkmarket link tor market
deep web search darkmarket
tor market links deep web search
darkmarket link darknet drugs
dark market 2023 dark internet
darknet drug links dark web market
darknet marketplace deep web markets
darkmarket how to get on dark web
tor marketplace dark market url
how to get on dark web darknet drug links
dark web access darknet sites
darknet marketplace deep web drug url
dark markets 2023 the dark internet
dark internet darknet market links
dark market list darknet links
free dark web dark web search engines
tor market links deep web drug markets
deep web drug url darkweb marketplace
deep dark web darkweb marketplace
the dark internet dark internet
blackweb official website darknet search engine
dark website dark web drug marketplace
dark web search engines darkmarket link
deep web sites drug markets onion
darknet links dark web sites links
dark internet dark market 2023
dark market 2023 tor marketplace
the dark internet darknet sites
dark web site deep web search
tor market url darknet sites
dark web site dark internet
drug markets onion darkmarket url
dark website tor market links
dark markets drug markets dark web
deep web drug store deep web markets
drug markets dark web onion market
dark internet darkweb marketplace
deep dark web darknet websites
darknet drug market darkweb marketplace
deep web markets dark markets 2023
deep web sites dark web access
dark web sites links darkmarket url
tor markets darknet market links
darknet sites darkmarket 2023
blackweb darknet drug links
darknet drug market darknet drug market
darknet drug market dark web sites links
dark websites dark net
You actually mentioned this perfectly!
write my essay essay writing service helping others essay medical school personal statement
deep web markets deep web drug markets
dark web websites dark website
deep web links dark internet
dark web sites links tor markets
dark market onion tor dark web
tor dark web darknet site
dark web websites tor darknet
dark web access dark markets
drug markets dark web darknet market links
the dark internet darknet marketplace
darkmarket darknet markets 2023
dark net blackweb official website
darknet drugs deep dark web
tor dark web dark web search engine
dark web search engines deep dark web
dark market onion darkmarket 2023
deep dark web deep web markets
This is nicely said. !
how to write a college essay the college essay guy essay helper free help essay
dark net dark web site
dark market url darkmarket list
tor markets 2023 tor market links
free dark web drug markets onion
dark web drug marketplace deep dark web
free dark web dark website
dark net tor market url
dark web access darknet drug store
deep dark web dark web access
tor market url dark web links
drug markets onion dark web drug marketplace
blackweb dark web market links
darknet markets 2023 dark websites
free dark web tor market url
deep web drug store tor dark web
deep web sites darkmarket 2023
tor markets darknet market
tor markets drug markets onion
darknet markets 2023 darknet links
dark web site dark internet
darknet websites darknet market links
dark net darknet drug store
dark web site deep web links
dark web websites dark websites
darkmarket url darknet market links
dark web search engine tor markets 2023
dark websites how to get on dark web
deep web markets tor markets links
deep dark web dark web site
bitcoin dark web deep web drug markets
dark web markets tor darknet
darknet seiten darkmarkets
darknet drug market darknet drug store
darknet links tor markets
deep web links dark websites
darknet websites how to access dark web
darknet drug store darknet seiten
dark web search engines deep web search
blackweb darknet market links
deep web sites dark market url
darkweb marketplace darknet seiten
darkmarket list dark internet
onion market dark web market list
deep web drug markets free dark web
tor dark web drug markets onion
darknet links dark web market links
dark web market links dark web markets
tor marketplace deep web sites
darknet market links onion market
tor market url dark market url
dark web websites tor markets links
tor market url onion market
tor markets links darknet websites
dark markets 2023 darknet market
darknet market list tor market url
dark web links the dark internet
darkmarket link darknet links
darknet drugs darknet sites
deep web drug markets free dark web
deep web drug url dark web link
dark market url dark markets
darkweb marketplace darknet markets 2023
the dark internet dark web sites links
darknet marketplace bitcoin dark web
darknet market deep web drug links
dark markets 2023 darknet markets
dark market list darknet market links
black internet tor darknet
darknet market dark web websites
dark web market deep web drug links
deep web sites deep web links
dark market list drug markets dark web
darknet sites darknet links
darknet seiten dark web market links
dark web markets darknet markets 2023
onion market deep dark web
bitcoin dark web dark web sites links
tor darknet bitcoin dark web
dark website darknet drug market
darknet websites how to get on dark web
tor markets links darkweb marketplace
drug markets dark web tor marketplace
darkmarket list deep web drug url
Thanks. I value this.
write my research paper term paper help research paper services custom research paper writing services
Nicely put, Kudos.
do my programming homework do my homework for money homework do my math homework
tor marketplace drug markets onion
deep web search darknet market
tor market links darkmarkets
tor darknet drug markets onion
darkmarket tor darknet
drug markets dark web best darknet markets
dark market onion dark web site
tor markets 2023 darknet drug market
dark web sites links tor markets links
darknet drug links dark web site
dark web market links dark web sites
dark websites deep web drug url
darknet drugs darkweb marketplace
Wow tons of useful advice!
paper writers for college paper writer services write my paper for cheap how to write an apa paper
how to get on dark web darkweb marketplace
dark web websites darknet market
dark market 2023 darknet market list
dark market list dark market list
how to access dark web dark web websites
darknet market links darknet markets 2023
black internet tor markets links
darknet drug store blackweb official website
how to get on dark web black internet
best darknet markets dark market link
darknet websites darkmarkets
dark net blackweb
dark market deep web drug links
dark web link darknet marketplace
dark market link darknet site
dark web markets darknet market list
darknet market lists drug markets dark web
You actually mentioned this effectively!
dissertation writer dissertation abstracts international phd dissertation writing dissertation writing services
Many thanks. Plenty of info.
professional essay writing services writing a narrative essay cheap essay writing services paper writing service college
best essay writing service review college application essay writing service writing services best college essay writing service
help with writing https://essaywritinghelperonline.com
dark net bitcoin dark web
blackweb darknet drug market
blackweb official website dark markets
tor market url darknet market lists
dark market onion dark web link
darkweb marketplace darknet market links
dark market onion darknet market
tor market darknet websites
tor markets links tor market
darknet drug links onion market
darkweb marketplace free dark web
darknet market darknet drug store
dark web access darkmarket 2023
deep web markets dark market link
black internet dark web link
tor markets links dark markets
dark web sites links dark market onion
darknet markets dark market onion
dark web access the dark internet
dark websites drug markets dark web
dark web market darkmarket 2023
black internet dark internet
dark web sites darkmarket link
darknet websites darknet markets 2023
darkmarket 2023 darknet seiten
dark web drug marketplace dark web sites
darkmarkets onion market
darknet search engine dark web search engines
dark market 2023 tor market links
darknet search engine darknet markets
darkmarket dark market link
dark web search engines deep web search
dark web link free dark web
dark website dark internet
dark web sites links darkmarkets
dark market onion darknet drugs
deep web drug links dark market link
deep web drug store dark market url
dark web market list darknet search engine
best darknet markets dark web search engines
blackweb official website darknet links
darknet drug store darknet drug links
deep web drug url tor market links
dark market list deep web sites
darknet sites darknet market
dark web market links dark market 2023
darkmarket list darknet marketplace
dark web link dark web websites
dark market 2023 dark market onion
dark web search engine dark web links
dark web sites links tor market
darkmarkets dark markets 2023
dark web search engine tor darknet
bitcoin dark web darknet websites
tor markets darkmarkets
best darknet markets dark markets 2023
dark markets 2023 dark market list
tor market links darknet marketplace
darknet drugs dark web search engines
darknet drug store darknet market
drug markets onion dark web site
dark web search engine dark web drug marketplace
how to access dark web darknet drug store
blackweb official website blackweb official website
dark web market list darkmarket link
darkmarkets blackweb
best darknet markets dark website
drug markets onion the dark internet
tor marketplace dark market link
deep web search darknet markets
darkmarkets deep web drug store
dark web search engine blackweb official website
dark markets darknet market list
dark market onion darkmarket url
dark web search engines dark websites
tor dark web darknet markets
tor marketplace darknet market lists
dark web access tor dark web
darknet marketplace dark web drug marketplace
dark websites dark market list
tor dark web deep web drug links
Terrific facts, Cheers!
pay to do my homework do my homework for free do my chemistry homework homework
blackweb darknet sites
deep web drug links how to access dark web
tor market url blackweb
tor market url drug markets onion
dark web sites dark web links
blackweb dark markets 2023
tor markets darknet drug store
dark net black internet
darkmarket url tor marketplace
dark market link darknet site
darknet drug links how to access dark web
drug markets onion dark net
darknet markets 2023 tor market url
darknet marketplace dark market url
darkmarket dark websites
Fantastic advice. Thanks.
service to others essay admission essay writing service will writing service essay review service
dark markets 2023 darknet marketplace
tor markets drug markets onion
dark web drug marketplace dark web sites
darknet markets dark website
dark market link darkmarket 2023
dark web market links tor darknet
darknet sites tor markets
dark web sites black internet
darkweb marketplace tor market links
free dark web darkmarket list
blackweb official website deep web drug markets
the dark internet dark web access
darknet market lists darknet sites
dark net dark markets 2023
deep web search onion market
black internet darknet websites
the dark internet darknet sites
darknet search engine deep dark web
onion market dark web market links
darkmarkets dark websites
darknet markets dark website
dark market list best darknet markets
darknet market darknet seiten
how to get on dark web darknet sites
dark market list dark web link
how to get on dark web deep web drug markets
dark website darknet market links
deep web sites free dark web
darkmarket 2023 dark website
deep web drug links deep web links
darkmarket dark web market
dark markets darkmarkets
the dark internet darkweb marketplace
darknet market links how to get on dark web
deep web drug url tor markets 2023
dark internet dark web search engine
darknet site deep dark web
dark net darknet links
darkmarket 2023 darkmarket url
dark web market list darknet markets
dark web links dark web sites links
darknet market lists darknet drug links
tor market url dark market
darknet market lists darknet links
best darknet markets darknet search engine
dark web search engine best darknet markets
darknet markets 2023 dark web markets
deep web sites darkmarkets
dark web market dark web websites
blackweb dark websites
darknet site dark web access
deep web sites best darknet markets
dark web market links dark markets 2023
darknet markets 2023 best darknet markets
dark web search engines darknet drug links
dark web search engine deep web sites
onion market darkmarket url
bitcoin dark web dark web sites links
darknet search engine deep web links
dark web market dark web drug marketplace
blackweb darkmarkets
darkmarket link the dark internet
darkweb marketplace darkmarket url
darknet links dark market url
deep web drug links dark web sites links
deep web drug markets darkmarket link
dark web site dark market
darknet market list dark net
darknet search engine deep web sites
darknet market dark markets 2023
dark web market list drug markets onion
darkmarket 2023 dark web sites
darknet drug market darknet sites
dark web market list darknet drug links
darknet market links blackweb
dark web markets dark website
black internet deep web drug links
tor dark web dark web sites
darknet markets dark net
darknet site dark market url
dark website tor market url
darknet market list free dark web
onion market bitcoin dark web
tor marketplace dark web link
darkweb marketplace darknet market list
dark market onion dark web sites links
tor market url darkmarket list
dark web site deep web links
darknet market list blackweb official website
dark web market links onion market
drug markets dark web dark websites
darknet seiten deep web sites
dark market list dark market
darknet marketplace how to get on dark web
dark market list free dark web
tor markets deep dark web
free dark web dark web markets
darkmarkets dark web search engines
darkmarket 2023 how to get on dark web
the dark internet dark web websites
darkweb marketplace dark web site
darkmarket link bitcoin dark web
dark web links darknet websites
darkmarket 2023 dark web links
dark website deep web markets
tor markets links dark net
how to access dark web deep web links
dark websites dark web websites
darkweb marketplace dark web sites links
dark market url dark web market list
dark web search engines dark website
onion market dark websites
dark web market links tor markets links
dark markets 2023 dark web market
tor markets dark web markets
dark markets 2023 dark web sites
deep web drug links darkweb marketplace
deep web links dark web websites
deep web search bitcoin dark web
darknet markets dark web search engine
bitcoin dark web dark web link
darknet site dark web site
drug markets dark web darknet drug store
deep web links black internet
darknet market lists dark internet
drug markets dark web deep web markets
bitcoin dark web darknet drug links
deep web drug markets dark web websites
tor market dark web search engine
deep web drug markets darknet seiten
darknet drugs tor darknet
darknet site dark website
dark internet darkmarket link
darknet marketplace dark market list
how to access dark web deep web drug url
dark net tor markets links
deep web links darknet market lists
dark web search engine tor markets links
best darknet markets dark web market list
darknet drug links dark web site
tor dark web darknet drug market
deep web links deep web drug markets
tor markets 2023 darkweb marketplace
dark web websites deep web drug url
blackweb dark web market list
darknet markets darknet market
dark web websites dark website
deep web drug store darkmarket 2023
tor markets best darknet markets
deep web drug markets best darknet markets
darknet seiten dark web links
free dark web darknet drugs
darkmarket url dark market
darknet links dark web sites links
deep web search dark markets 2023
darknet drugs dark market onion
onion market drug markets onion
darknet drug market darknet market list
tor markets links deep web search
black internet black internet
darkmarkets dark web sites
tor marketplace darkmarkets
tor markets blackweb
onion market darknet links
dark web drug marketplace darknet market list
blackweb dark web search engines
dark web links dark web drug marketplace
dark web drug marketplace tor markets links
tor dark web dark market list
bitcoin dark web tor markets links
deep web drug url deep web drug store
the dark internet dark web websites
dark market url dark market 2023
how to get on dark web dark web market list
dark market list darkmarket
dark web markets darkmarket link
deep web drug links onion market
darknet drug links tor marketplace
darknet seiten darknet drug market
dark market url deep web links
deep dark web dark market onion
deep web markets dark internet
black internet onion market
dark web drug marketplace the dark internet
tor markets 2023 darkmarket url
drug markets dark web dark net
darknet marketplace tor dark web
dark web access darkmarkets
deep web drug links deep web links
dark web market links dark market list
tor markets links dark web site
dark web search engine darknet market links
dark web websites darknet markets 2023
dark web websites dark website
dark web websites darkmarket list
best darknet markets darknet site
darknet sites onion market
blackweb official website blackweb
darkmarket tor marketplace
blackweb dark web sites
dark market onion darkweb marketplace
dark markets 2023 darknet websites
tor darknet darkmarket
dark internet the dark internet
dark web websites dark web search engines
darknet market lists dark web search engine
dark web market list onion market
dark websites deep web markets
dark market 2023 tor market url
how to access dark web darknet drug market
dark web search engines dark web websites
tor market url blackweb official website
darknet market dark web markets
tor market links dark market 2023
dark web site dark markets
deep web search dark website
the dark internet darkmarket link
deep web search tor markets links
dark web search engines dark website
darkmarkets bitcoin dark web
deep dark web tor marketplace
deep web markets darkmarket
the dark internet deep web drug links
dark website deep web drug url
how to access dark web drug markets dark web
dark internet dark web sites links
dark web market list dark web drug marketplace
blackweb darkmarket
darknet market links darknet sites
darknet market links deep web drug links
darknet marketplace dark net
dark web market list darkmarket url
darknet market lists tor market
dark market tor market links
blackweb official website dark markets
tor market links dark market 2023
deep web sites drug markets onion
dark net darkmarket
dark website darknet markets 2023
darknet market how to get on dark web
best darknet markets dark web market list
darknet sites dark web site
dark market 2023 dark market list
darknet drug links dark net
bitcoin dark web darknet drugs
deep web markets onion market
darkmarket 2023 drug markets onion
tor markets links dark net
dark web site deep web drug url
deep web search dark websites
dark market url dark market url
drug markets onion darknet websites
onion market free dark web
dark web websites darknet markets
dark web search engines darkmarket link
darknet sites dark web markets
tor markets the dark internet
how to access dark web tor market url
deep web drug url darknet market
drug markets onion tor markets links
darkmarket url deep web links
darknet drug store darknet site
dark market url dark web search engines
darkmarket 2023 dark web access
darknet market dark web link
dark market 2023 tor marketplace
dark market list dark internet
tor darknet tor markets 2023
deep web links how to get on dark web
deep web drug store blackweb
deep web drug markets dark web market list
tor darknet dark web markets
dark web sites deep web search
the dark internet black internet
darkmarket darkmarkets
dark web site dark web site
tor market url how to access dark web
darknet websites dark web market list
dark internet dark websites
tor markets links deep web drug markets
dark markets tor market
black internet darkmarket 2023
dark web market list free dark web
tor market url tor markets 2023
tor markets darkmarket
deep web search tor market links
darknet market list darknet market links
darkmarket 2023 dark web search engine
bitcoin dark web tor market url
dark websites black internet
darknet drug links darkmarket
how to get on dark web dark internet
free dark web free dark web
dark web links darknet site
dark web drug marketplace dark market url
dark web search engine darknet marketplace
darknet drug store dark market url
dark market list dark web links
best darknet markets dark web links
darkmarket url darknet drugs
blackweb darknet marketplace
darknet drug store deep web links
darknet site darknet market lists
the dark internet darknet marketplace
darknet links deep web drug links
darkmarket list darknet market links
dark web market links dark market
dark web search engines darknet site
how to get on dark web dark web markets
darkmarket list dark market 2023
black internet dark web drug marketplace
how to get on dark web dark internet
darkmarket link dark internet
blackweb dark internet
drug markets dark web deep web drug url
dark market link tor markets 2023
tor darknet darkmarket list
dark web websites dark web drug marketplace
dark web sites darknet market
darknet seiten darknet market list
tor dark web blackweb
tor market links tor market links
black internet darknet sites
darknet market lists dark web sites
dark web market list dark websites
darknet market links dark website
dark internet dark markets
dark web websites darkmarket
dark web drug marketplace darknet market links
deep web drug links dark web access
dark net darknet market lists
darknet drug store drug markets dark web
darknet sites dark web links
darknet drugs dark web search engines
deep web drug url darkmarket list
darkmarkets tor dark web
darknet markets 2023 tor market url
deep dark web darknet market
onion market darknet marketplace
darknet drug store drug markets onion
darkmarket dark net
dark web link darknet markets 2023
dark web search engines darknet drug market
drug markets onion tor dark web
deep web search dark web market links
blackweb dark web drug marketplace
tor market links darknet search engine
how to get on dark web dark web search engine
darknet drug store darknet drug market
dark market link dark web access
dark internet tor marketplace
blackweb darknet market list
dark market list dark web search engines
drug markets dark web tor market url
tor markets links the dark internet
bitcoin dark web dark market 2023
darknet market list deep web sites
darknet websites tor markets 2023
darkmarket link darkmarket 2023
dark market 2023 darknet drug links
onion market dark net
darknet links deep web markets
darknet drug links darknet market links
dark market list darknet market links
deep web links dark web markets
darknet market links darknet market list
darkweb marketplace darknet market list
onion market blackweb official website
deep web drug url drug markets onion
drug markets onion darknet site
darkmarkets deep web drug markets
deep web markets darkmarket link
darkmarket dark web market links
darknet market list dark web access
tor market url drug markets onion
dark markets darknet sites
dark market onion tor markets
darknet site darknet drug links
dark markets 2023 dark market
darkmarket 2023 darknet markets 2023
dark website deep dark web
darknet market list darknet markets
darkweb marketplace darknet markets 2023
tor market links bitcoin dark web
best darknet markets deep web search
tor market tor marketplace
dark web websites darknet websites
how to access dark web dark websites
dark market list dark web market links
dark web link darknet market list
dark market url tor marketplace
dark websites dark web search engine
darknet drug store darknet drug store
darknet drug links dark market 2023
dark web market list darknet search engine
dark internet tor marketplace
darknet markets 2023 darknet market links
dark market url deep web links
darkmarket url darkweb marketplace
dark websites the dark internet
darknet seiten darknet websites
tor market tor market url
dark web access dark market 2023
the dark internet dark market list
tor darknet tor marketplace
dark market url dark websites
darknet market darknet market list
best darknet markets dark markets 2023
darkmarket url dark web market links
how to get on dark web tor dark web
tor market links the dark internet
dark market 2023 best darknet markets
deep web links darknet marketplace
tor markets deep web sites
blackweb official website tor market
deep web drug links dark web market
darknet drugs darknet market
dark web market list tor markets 2023
dark net darknet search engine
darknet markets 2023 onion market
tor markets how to access dark web
deep web links deep dark web
dark market link darknet marketplace
darknet site darkmarkets
deep web links darknet websites
darknet marketplace dark web market links
deep dark web darknet market list
dark market list dark web links
dark market list darkmarket
tor darknet how to access dark web
dark web market list dark web search engine
dark web market dark web market
dark web site bitcoin dark web
darknet sites tor dark web
dark web search engines tor markets
dark net darkmarket 2023
dark web market list best darknet markets
dark web access blackweb official website
darknet drug links how to access dark web
darkmarket link dark net
tor market url dark web websites
darkmarket darkweb marketplace
darknet search engine how to get on dark web
tor markets 2023 dark web access
darknet market tor dark web
blackweb official website dark web sites
deep dark web dark market onion
dark market url tor market url
darknet drug store tor marketplace
dark web sites dark web market
dark web sites links tor dark web
drug markets onion dark web websites
darknet search engine darkmarkets
free dark web dark web sites links
darknet market darkmarket
darknet search engine darknet seiten
darkmarket 2023 deep web drug url
tor markets dark market
darknet sites dark internet
darkmarket 2023 deep web drug links
dark web websites best darknet markets
darknet drug store darknet seiten
onion market tor market url
dark web site dark web markets
darknet market dark market
tor darknet tor markets 2023
darknet drug market deep web markets
darknet market links dark web link
dark web access darknet markets
darknet sites deep web markets
dark web websites deep web markets
darknet market links deep web drug url
tor dark web blackweb official website
darkweb marketplace blackweb official website
how to access dark web darknet websites
the dark internet dark web links
darknet market lists tor dark web
onion market best darknet markets
blackweb official website darknet market
dark market onion tor markets 2023
drug markets onion darkmarket
darknet search engine drug markets dark web
tor markets darkmarket 2023
darknet market dark web websites
deep web drug url dark web search engines
darknet links darkmarket
darkmarket list tor dark web
darknet market lists dark internet
deep web drug markets blackweb
bitcoin dark web deep web sites
darknet drug market deep web links
the dark internet darknet marketplace
dark net dark web drug marketplace
darknet site tor markets
how to get on dark web darknet market list
dark web search engine blackweb official website
deep web drug links dark web market list
onion market dark websites
darknet search engine darknet sites
darknet marketplace tor markets 2023
dark web link deep dark web
dark internet dark web sites
darknet drug market darknet site
dark web search engine darkmarket list
drug markets dark web blackweb
dark markets dark web site
deep web markets tor darknet
dark market list darknet links
dark websites darkmarket link
tor markets dark web websites
darknet seiten deep dark web
darkmarket link dark websites
dark web search engine tor markets 2023
deep web search dark web links
tor markets dark markets
dark web websites darknet sites
darkmarket 2023 tor markets 2023
dark web site how to get on dark web
darknet market lists tor market links
dark market link darknet drug store
dark web link darknet drug store
dark market 2023 darknet markets
deep web drug links dark web market list
blackweb official website how to get on dark web
tor markets 2023 dark web links
darknet market links tor market url
darknet drugs dark web sites
tor markets 2023 tor marketplace
dark net dark web drug marketplace
deep web markets dark web search engines
deep web drug url deep web markets
dark web search engine darknet links
deep web drug markets darkmarket
dark markets dark web market links
tor markets 2023 onion market
deep web drug url dark market
the dark internet dark web drug marketplace
darkmarket list darknet site
darkmarket list darknet drugs
darknet drug links dark websites
darkmarket free dark web
dark web links tor markets links
dark web access dark market
dark markets dark market
dark web drug marketplace darkmarket list
tor marketplace darknet links
tor darknet how to access dark web
dark web search engines dark web search engines
darknet drug links tor markets links
deep web drug links darkmarket link
tor marketplace dark markets
tor markets darknet site
deep web drug url darkmarket list
deep web drug url dark web search engine
darknet market lists deep web drug store
dark web links deep web sites
blackweb official website darknet links
dark market url darknet drugs
deep web search drug markets dark web
deep dark web dark web drug marketplace
dark web market list darknet seiten
black internet darknet marketplace
darknet seiten dark web links
darknet websites darknet seiten
blackweb darknet site
blackweb darknet sites
tor market url dark web market
dark web market links tor market url
dark web drug marketplace dark web sites
darknet websites deep web search
best darknet markets dark web drug marketplace
bitcoin dark web dark websites
deep web links best darknet markets
dark web market links darkmarkets
deep web sites dark market 2023
tor markets 2023 darknet market lists
free dark web darknet markets
darknet drug store dark web sites links
tor markets darknet market list
deep dark web darknet market
darknet links darknet search engine
dark market onion darknet marketplace
deep web links deep web links
onion market dark web links
dark market 2023 deep web search
deep dark web tor markets 2023
darkmarket 2023 deep web sites
dark website darkmarket list
deep web drug url deep web drug url
dark website dark web search engine
dark internet darkmarket
dark market link darknet search engine
blackweb official website dark web sites
darknet marketplace deep dark web
darknet links tor markets links
darknet marketplace darknet drugs
deep web links dark web markets
darknet websites dark market onion
free dark web darknet seiten
blackweb official website dark web links
deep web markets darkmarket url
tor market links dark web market links
darknet drugs the dark internet
deep web markets dark markets
the dark internet darknet sites
black internet dark web market list
deep web drug store deep dark web
darknet markets 2023 dark market link
the dark internet dark web market list
tor markets darkweb marketplace
dark net darknet market list
dark web market links dark markets 2023
darknet marketplace best darknet markets
onion market bitcoin dark web
darkweb marketplace how to access dark web
dark market onion darknet markets 2023
dark market list free dark web
darknet drugs darknet drug market
dark web sites dark website
dark market onion darkmarket 2023
dark web sites links tor markets links
dark net darknet drug market
darknet websites darknet marketplace
darknet seiten darknet market links
dark web search engines dark web sites
darkmarket deep web links
dark web sites dark web market list
deep web markets darknet site
dark website dark markets 2023
darknet drug store dark web sites
dark web link darknet market lists
darknet market links darkmarket list
dark web drug marketplace dark web drug marketplace
darknet market lists tor markets
darkmarket 2023 tor markets
dark web market darknet search engine
deep web drug links darknet drugs
darknet drug store dark market 2023
dark market 2023 darknet market links
tor dark web dark web link
dark web market blackweb
dark web markets how to get on dark web
dark web sites links tor markets
tor market links deep web drug links
darknet market dark web link
darknet seiten dark markets
dark market link tor markets links
darknet markets 2023 darkmarkets
darknet seiten darknet sites
dark market url best darknet markets
darknet markets dark market list
blackweb official website deep web markets
blackweb dark web market links
dark internet drug markets dark web
darknet links darkmarket list
darknet seiten dark internet
deep web drug url dark web market list
deep web markets dark web sites links
how to get on dark web black internet
dark web drug marketplace drug markets dark web
darknet drug links bitcoin dark web
deep web drug markets darknet sites
blackweb tor market
deep web markets dark web link
dark web markets darknet market lists
darknet websites darknet market
dark web search engine darkweb marketplace
dark web access dark websites
deep web drug url deep web drug links
darkmarket dark markets
blackweb darknet links
darknet marketplace dark internet
deep web markets darknet seiten
darknet websites darknet marketplace
darknet search engine tor markets links
dark markets darkmarket url
deep web links tor markets links
darkmarket list darknet sites
darkmarket url dark web sites links
deep web drug store free dark web
free dark web tor markets
darkmarket link deep web drug links
dark web links darknet drug links
deep web drug store dark web sites
dark market link darknet marketplace
darknet links dark web search engines
tor markets links dark web websites
dark websites dark web market links
dark market url dark market 2023
dark web link darknet drug links
tor darknet how to get on dark web
darknet drugs darknet search engine
darknet seiten darknet marketplace
onion market dark websites
darkmarket url tor market url
darkmarket list tor markets
deep web drug markets tor markets
dark web search engines darknet websites
tor darknet darkmarket url
dark web link darkmarket
the dark internet darkmarket list
darknet drugs darknet search engine
dark web market links dark market list
darknet seiten darknet sites
dark market link deep web drug store
darkmarket list dark net
tor market links darknet websites
darknet market links dark markets
tor markets 2023 dark web drug marketplace
darknet drug store darknet links
dark websites bitcoin dark web
dark web links tor markets 2023
darknet drug market darkmarket 2023
darknet markets 2023 deep web markets
darknet market list blackweb
darkmarket 2023 deep web links
blackweb dark web link
darkmarket list dark market list
dark web sites links dark web link
darknet drug market tor darknet
deep web search darknet market list
deep web links deep web markets
tor marketplace tor darknet
dark net deep web drug markets
blackweb official website dark websites
dark web websites dark web sites
deep web markets drug markets dark web
darknet market links deep web drug store
dark market list black internet
deep web drug links darknet drug market
darknet drug market darkweb marketplace
tor dark web tor dark web
dark web markets dark web sites
darkmarket list dark web websites
dark web search engines dark markets 2023
free dark web drug markets dark web
darknet market lists dark web drug marketplace
dark web websites deep web search
darknet markets 2023 dark market link
dark net tor markets
dark web sites dark web sites
darknet market dark net
darknet market tor market url
darknet search engine dark web search engines
drug markets onion dark web access
deep web markets deep web drug store
tor markets tor marketplace
dark web links darknet markets
dark market 2023 darknet drug market
dark internet darkweb marketplace
dark market url dark web site
drug markets onion dark websites
dark market 2023 tor markets 2023
darknet websites darknet sites
dark market link dark web websites
darkmarket url darknet drug links
bitcoin dark web dark web sites links
dark markets 2023 onion market
darknet market lists darknet drug links
deep web links deep web sites
darkmarket tor markets links
dark web market list how to access dark web
dark net dark web sites
darknet seiten black internet
darknet site free dark web
darknet markets dark web site
dark market 2023 black internet
black internet darkmarket
dark market url blackweb official website
dark market link free dark web
best darknet markets dark web link
dark markets 2023 tor darknet
darknet site darknet marketplace
bitcoin dark web blackweb
tor darknet tor darknet
best darknet markets darkweb marketplace
darknet drugs dark internet
darkmarket 2023 dark market onion
the dark internet deep web drug markets
dark web links darkweb marketplace
dark web market list darkweb marketplace
darknet market links dark web sites
deep web drug markets darkmarket
dark web search engine tor market
drug markets onion drug markets dark web
darknet markets dark web drug marketplace
darkmarket link dark web search engine
dark web site darknet seiten
how to get on dark web dark web sites links
tor market url dark internet
darknet market lists deep web markets
dark web sites links darknet links
dark web sites darknet links
darknet markets 2023 dark web site
tor markets 2023 how to access dark web
dark web access how to access dark web
deep web drug store darknet websites
dark web links darknet search engine
darknet websites tor markets
dark market url deep dark web
free dark web darkmarket list
darkmarket url darknet links
tor market links dark web websites
blackweb official website darkweb marketplace
dark net bitcoin dark web
darkmarket dark websites
dark web link tor markets 2023
darknet site deep web search
drug markets onion best darknet markets
blackweb official website deep web drug markets
dark market deep web drug url
dark web link dark internet
darknet drugs dark web market list
deep web links deep web links
darknet drug market deep web markets
darknet links darknet sites
dark market onion dark web market links
tor market links dark web site
dark web markets deep web drug url
deep dark web onion market
dark web link dark market
darkmarket 2023 dark web market
dark web search engines darknet drugs
dark web market dark web search engines
tor market deep dark web
dark market url tor market url
dark web search engines deep web sites
darknet links dark website
deep web drug store tor darknet
dark web links onion market
dark web market list tor market url
darknet links dark web market
dark market list darkmarkets
darknet site free dark web
dark markets dark web websites
tor darknet darkweb marketplace
tor markets the dark internet
dark web market list darknet drugs
tor markets how to access dark web
darknet market dark websites
darkmarket link darknet market list
dark markets dark web websites
dark web search engines dark markets
drug markets onion dark web sites
darkmarket link dark website
drug markets dark web free dark web
darkmarket list tor market links
darkmarkets dark websites
dark market dark market
dark web markets dark web search engine
drug markets dark web dark web market
deep web search darknet markets 2023
dark web link dark market link
tor marketplace dark market 2023
dark web access dark web search engine
darknet market how to access dark web
darknet market lists darknet market
dark market list dark net
darkmarkets darknet drug links
darknet market links darknet drug links
deep web markets darknet sites
darknet drug market dark web sites
dark market url deep web search
darknet drug links dark web links
dark net tor market url
deep web sites deep web drug store
how to access dark web darknet marketplace
dark market onion dark markets 2023
darkmarket tor market links
best darknet markets tor markets
darknet websites tor markets
dark internet deep web drug links
deep web drug markets dark market onion
free dark web dark web drug marketplace
dark web links how to get on dark web
tor darknet dark web market list
darknet drug store dark markets
deep web links the dark internet
dark web drug marketplace tor dark web
darkmarket url dark markets
dark market link tor marketplace
how to get on dark web darknet drug store
free dark web darkmarket link
dark market link darknet sites
tor market links free dark web
tor market dark web search engine
dark market link dark web markets
darknet marketplace dark markets 2023
dark market onion darkmarket link
darkmarket 2023 dark market list
dark web market list darknet site
dark net dark web market links
tor darknet dark website
best darknet markets darknet market lists
how to access dark web blackweb
black internet darknet links
dark web search engine darknet markets 2023
dark web access darknet drugs
deep web search how to get on dark web
darknet drug store blackweb official website
deep web drug markets darknet markets
deep web search darknet market list
darknet marketplace dark websites
dark web markets darknet links
darkmarket list dark internet
darknet market list dark web search engines
onion market dark market 2023
deep web drug markets tor markets
dark web sites links free dark web
darkmarket 2023 bitcoin dark web
tor markets dark market 2023
darknet links darknet drug store
tor markets 2023 dark market link
darkmarket url tor markets links
best darknet markets dark web markets
deep web markets dark web site
dark markets 2023 tor markets 2023
the dark internet the dark internet
darknet sites dark market
deep web markets tor market
deep web drug store dark website
dark web access how to get on dark web
darkmarkets darknet markets
dark web search engine dark website
best darknet markets tor markets 2023
dark website darknet sites
blackweb official website deep web drug links
darknet links darkmarkets
deep web links blackweb
dark website drug markets onion
darknet drug links darknet markets 2023
free dark web dark websites
darknet drugs dark market link
tor markets 2023 deep web drug markets
dark web links blackweb official website
dark markets 2023 darknet market
how to get on dark web darknet links
dark net darknet drug links
deep web sites darknet seiten
the dark internet dark market list
darknet market lists darkmarket 2023
tor markets tor markets
tor marketplace dark market
darknet market dark internet
deep dark web dark market list
deep dark web dark market
dark net tor market
deep dark web tor markets links
drug markets dark web black internet
dark web websites tor market
dark web market links tor market links
darknet drug market darknet market links
drug markets onion darkweb marketplace
darknet market lists darknet drugs
dark web market list how to get on dark web
dark web access tor dark web
deep web sites darknet market list
dark market list dark internet
dark web access deep web drug links
dark website tor markets 2023
darknet search engine dark web market links
dark web market darknet drug links
onion market tor marketplace
darknet market lists darkmarket
dark web sites links tor market links
darkmarket 2023 dark markets 2023
drug markets onion deep web drug links
dark net dark markets 2023
dark web market links darknet site
darknet marketplace dark market link
darkmarket list blackweb
dark internet deep web sites
bitcoin dark web darkweb marketplace
how to get on dark web dark market 2023
darknet seiten dark web market links
dark net darknet marketplace
dark market url tor markets
dark market url deep web drug store
darknet sites dark web drug marketplace
tor market darkmarket link
blackweb darknet websites
dark markets dark web site
dark web market dark web sites links
darkmarkets dark web links
deep web drug links tor dark web
darkmarket list dark web sites
darknet site the dark internet
dark market list dark web link
deep web search darknet site
darknet sites darkmarket list
tor dark web deep web drug links
dark web drug marketplace dark web sites links
dark web search engines deep web search
darknet market deep web links
tor markets 2023 darknet websites
drug markets dark web deep web markets
darkmarket 2023 dark websites
deep web markets dark web search engine
tor markets links darkmarkets
dark market link tor marketplace
dark web search engines dark market list
darkmarkets dark web site
dark markets darkmarket
dark web sites links darkmarket list
darknet links dark websites
darknet drug links deep web links
darkweb marketplace dark web links
darknet search engine darknet drug store
dark web link deep web markets
dark web search engines deep web markets
dark internet dark market url
darknet drug links dark websites
deep web drug markets darknet market
darknet marketplace dark market list
dark websites best darknet markets
tor market links dark market list
dark web link darkweb marketplace
dark net dark market url
black internet darknet market list
dark web markets dark market list
darknet markets 2023 dark markets 2023
tor markets dark web sites links
darknet marketplace drug markets onion
blackweb official website darknet market links
deep web links darknet sites
darknet markets darkweb marketplace
blackweb tor market url
darknet search engine deep web sites
tor market darknet marketplace
deep web sites deep web drug markets
tor markets 2023 darknet market lists
dark net tor markets links
darknet market list tor markets 2023
deep web drug markets free dark web
dark web market list dark market list
tor markets free dark web
dark web market dark web sites links
deep web links darkmarket
dark website the dark internet
darknet drug market darknet drug store
darknet drug links darknet drug links
dark market link tor markets links
blackweb darkmarket link
darkweb marketplace darknet sites
dark web site tor marketplace
dark market url blackweb
darkmarket link darknet market lists
bitcoin dark web tor markets
dark web link darkmarket list
dark web markets dark web links
black internet darknet search engine
dark web search engines dark market list
darkmarket link how to access dark web
tor market tor market url
onion market deep web drug store
dark web link dark net
black internet dark web market
darknet site darkmarket url
deep web links dark web market
black internet darknet seiten
dark web access dark web site
darknet market darkmarket list
darknet drug store darknet drug links
darknet search engine dark markets 2023
dark net darknet markets 2023
darknet site darkmarkets
darknet links black internet
dark web drug marketplace dark market url
darkmarkets dark websites
dark web sites links dark web market links
dark web sites how to access dark web
deep web links darkmarket
darknet market links darknet market links
dark web drug marketplace drug markets onion
deep web drug markets tor market links
dark web market darknet marketplace
dark web drug marketplace black internet
the dark internet deep web drug links
tor markets blackweb official website
darkmarket 2023 deep web drug links
tor market url how to access dark web
dark markets tor marketplace
darknet marketplace deep web drug url
deep web drug markets drug markets dark web
dark web sites links dark market
dark internet darkmarkets
tor markets darknet drug store
dark market link deep web sites
deep web drug links tor market
dark web sites links free dark web
deep web drug url dark web search engines
deep web search dark website
dark markets bitcoin dark web
dark net dark market url
darknet markets 2023 dark market list
dark web sites darknet markets
deep dark web black internet
blackweb darknet site
darknet market list https://dark-market-heineken.com/ darkmarket
dark web drug marketplace https://worldmarketplacee.com/ drug markets dark web
darknet markets 2023 https://world-dark-market.com/ darkmarket list
darkmarkets https://worlddarkweb.com/ drug markets onion
tor market https://world-darkweb.com/ dark website
darkmarket link https://world-darkmarket-online.com/ tor markets links
blackweb official website https://heineken-onion-darkweb.com/ dark web drug marketplace
dark websites https://heinekendarkwebdrugstore.com/ dark web market list
onion market https://heineken-online-drugs.com/ darknet sites
darknet drug store https://worldonionmarket.com/ darknet drugs
darknet search engine https://heineken-drugs-market.com/ tor darknet
darkmarket 2023 https://cyphermarketplace24.com/ deep dark web
deep web drug url https://world-onion-darkweb.com/ darknet seiten
dark market https://heineken-onlinedrugs.com/ tor marketplace
dark web market links https://heinekendrugsonline.com/ tor market
the dark internet https://worlddarkwebdrugstore.com/ dark net
darkmarket 2023 https://heinekenoniondarkmarket.com/ dark web sites links
darknet seiten https://worldoniondarkmarket.com/ drug markets onion
bitcoin dark web https://heineken-onion-darkmarket.com/ dark market
dark web websites https://worlddrugsmarketplace.com/ free dark web
dark market onion https://world-onion-market.com/ darknet market lists
onion market https://world-drugs-market.com/ onion market
darknet search engine https://world-market-place1.com/ dark markets 2023
darkmarket list https://heinekendrugsmarket.com/ dark web websites
how to access dark web https://cypher-dark-market.com/ darknet markets
dark web market links https://world-drugs-online.com/ deep web sites
dark market 2023 https://dark-market-world.com/ darknet market
darknet markets https://cypher-darknet.com/ the dark internet
darkmarket url https://darkwebcypher.com/ best darknet markets
dark market list https://heineken-darkweb-drugstore.com/ tor marketplace
darknet seiten https://cyphermarket-darknet.com/ dark web market
dark web links https://world-darkmarketplace.com/ darknet marketplace
darkmarket https://dark-market-heineken.com/ blackweb official website
darknet markets https://kingdom-darkmarket.com/ dark net
deep web drug store https://worlddarkmarketonline.com/ dark web market
dark internet https://heinekendarknetdrugstore.com/ darknet links
darknet market https://heinekendarkwebdrugstore.com/ bitcoin dark web
tor markets https://heinekenonionmarket.com/ black internet
darknet websites https://world-onion-darkweb.com/ darknet drugs
darknet market links https://cypher-marketplace.com/ darkmarkets
tor market links https://world-online-drugs.com/ bitcoin dark web
darknet links https://dark-web-cypher.com/ tor marketplace
dark website https://heineken-drugs-online.com/ dark net
best darknet markets https://worlddrugsmarket.com/ darknet sites
darknet market lists https://heinekenonlinedrugs.com/ drug markets dark web
dark web markets https://worldoniondarkmarket.com/ darkmarket 2023
darknet markets 2023 https://heineken-onion-market.com/ the dark internet
darknet market links https://cypher-darkweb.com/ darkmarket link
darknet marketplace https://worldmarketplace24.com/ deep web sites
dark web site https://world-onion-darkmarket.com/ onion market
darknet search engine https://world-drugs-market.com/ the dark internet
how to get on dark web https://cypher-drugsonline.com/ onion market
deep dark web https://cypheronionmarket.com/ dark markets
dark market list https://cypher-darkwebmarket.com/ darknet drug links
dark market list https://darkmarketworld.com/ the dark internet
darknet sites https://kingdom-darkmarket.com/ darknet markets
drug markets dark web https://heineken-darkweb-drugstore.com/ dark web access
dark markets https://darkweb-world.com/ tor markets 2023
darkmarket 2023 https://world-onlinedrugs.com/ tor market
bitcoin dark web https://world-darkweb.com/ dark web market list
dark internet https://dark-market-heineken.com/ deep web drug links
dark web search engines https://cyphermarket-link.com/ best darknet markets
dark web site https://cypher-markett.com/ dark markets
how to access dark web https://worlddarkmarketonline.com/ darknet drug market
darknet drug store https://world-darknet-drugstore.com/ deep dark web
deep web search https://heinekenonionmarket.com/ how to get on dark web
best darknet markets https://worldonionmarket.com/ dark websites
how to access dark web https://worldonlinedrugs.com/ dark web sites links
darkmarket https://dark-market-cypher.com/ darkweb marketplace
dark website https://heinekenoniondarkmarket.com/ darkmarket list
darkmarket list https://cypherdarkweb.com/ darkmarkets
dark web search engine https://worldoniondarkweb.com/ darknet market lists
dark markets https://heineken-drugs-online.com/ how to get on dark web
free dark web https://heinekenonlinedrugs.com/ blackweb
darkweb marketplace https://heineken-onion-darkmarket.com/ blackweb
dark web access https://world-market-place1.com/ dark web websites
darkmarket 2023 https://cypher-dark-market.com/ dark website
dark web market https://cypher-drugsonline.com/ tor marketplace
dark web link https://cypher-onlinedrugs.com/ darkweb marketplace
how to access dark web https://darkwebworldmarket.com/ darknet market links
darkmarket list https://kingdomdarkwebmarket.com/ drug markets onion
darkmarket https://worldmarket-linkk.com/ dark web link
deep web drug url https://world-darkmarket.com/ deep web drug url
bitcoin dark web https://worldmarketplacee.com/ darknet market links
darknet seiten https://dark-market-world.com/ dark web websites
tor market links https://world-drugs-online.com/ dark web market
darkmarket url https://worlddarkweb.com/ dark web market list
deep web sites https://cypherdrugsmarket.com/ onion market
dark web market list https://cypher-market-onion.com/ deep web drug markets
tor markets https://cyphermarketplace24.com/ dark net
tor market url https://heinekendarknetdrugstore.com/ darknet market links
blackweb https://cyphermarket-link.com/ darkmarket list
darknet marketplace https://world-darkweb-drugstore.com/ dark web markets
darkmarket list https://worlddarkmarketonline.com/ dark markets
tor markets https://heinekenonionmarket.com/ darknet drug store
how to get on dark web https://dark-web-world.com/ dark web link
darkmarket 2023 https://worldonionmarket.com/ dark web links
dark markets 2023 https://world-drugs-market.com/ tor darknet
dark web site https://world-onion-darkmarket.com/ darknet market
dark market https://cypherdarkmarketplace.com/ darkmarket 2023
dark web market list https://darkmarketcypher.com/ darknet market list
drug markets dark web https://dark-web-cypher.com/ darknet marketplace
darkmarket url https://heinekenoniondarkmarket.com/ darknet drug market
dark market https://darkwebcypher.com/ dark web market list
tor darknet https://cypher-dark-market.com/ drug markets onion
darknet market links https://heineken-onlinedrugs.com/ dark market url
dark web websites https://heinekenonlinedrugs.com/ free dark web
deep web sites https://cypher-onion-darkweb.com/ dark web sites
darknet drug store https://worldmarket-url.com/ darknet market links
dark web link https://world-darkmarketplace.com/ onion market
drug markets dark web https://darkmarketworld.com/ tor dark web
how to get on dark web https://worldmarket-darknet.com/ darknet market links
dark markets 2023 https://world-onlinedrugs.com/ dark web search engines
tor market links https://heinekendrugsmarket.com/ darkmarket
tor dark web https://cyphermarketplace24.com/ dark web market links
darknet market lists https://cypher-market-onion.com/ darknet drug market
tor markets links https://cyphermarketplacee.com/ dark web sites
dark web drug marketplace https://cypherdrugsonline.com/ darknet market lists
deep web drug markets https://heinekendarknetdrugstore.com/ darknet drugs
darkmarket url https://worldmarketdrugsonline.com/ deep web drug url
tor market links https://world-darkmarket-online.com/ tor darknet
deep web drug markets https://worlddrugsmarketplace.com/ tor market
deep web sites https://dark-market-heineken.com/ blackweb
darknet market links https://cypher-darkmarket.com/ tor dark web
darknet market lists https://cypherdarknet.com/ dark web link
dark web search engine https://cypher-darknet.com/ dark web links
darknet market links https://heinekenoniondarkweb.com/ darkmarket list
dark web link https://heinekenonlinedrugs.com/ tor market links
drug markets onion https://dark-web-cypher.com/ darknet market lists
dark market 2023 https://cypher-dark-market.com/ dark internet
darknet search engine https://cypheronlinedrugs.com/ darknet drug store
dark web sites https://cypher-onion-market.com/ blackweb
darknet markets 2023 https://worldmarket-darknet.com/ darkmarket url
blackweb https://darkmarketworld.com/ dark web sites
dark markets https://worldmarketplacee.com/ darknet seiten
darknet websites https://world-onion-darkweb.com/ darkmarket
darknet links https://cypher-market-online.com/ deep web links
tor market url https://darkweb-world.com/ dark web market
tor markets links https://world-onlinedrugs.com/ tor markets 2023
best darknet markets https://cypheronionmarket.com/ tor darknet
dark web websites https://heinekendrugsmarketplace.com/ tor market url
dark market link https://cyphermarketplace24.com/ dark web drug marketplace
darkmarket 2023 https://heinekendarkwebdrugstore.com/ darknet drugs
bitcoin dark web https://cyphermarket-darknet.com/ dark web market links
tor market url https://cypherdrugsonline.com/ black internet
dark market url https://dark-web-world.com/ deep web drug store
tor market url https://cyphermarket-link.com/ darkmarket url
the dark internet https://world-onion-market.com/ drug markets dark web
dark web links https://worlddrugsmarketplace.com/ darkmarket 2023
dark market list https://worlddarkmarketonline.com/ dark web search engines
deep web drug links https://heinekenonionmarket.com/ dark web sites links
deep web links https://dark-market-heineken.com/ darknet markets
deep web search https://cypher-darkweb.com/ darknet market list
tor markets 2023 https://cypher-onion-darkmarket.com/ darknet market links
deep web sites https://world-darknet.com/ tor dark web
dark markets 2023 https://heinekenoniondarkweb.com/ dark web sites links
blackweb https://heineken-onion-darkmarket.com/ dark internet
dark website https://world-darkmarket.com/ darknet markets 2023
dark net https://world-onion-darkweb.com/ darknet sites
darknet seiten https://worldmarketplacee.com/ darknet drug store
darknet seiten https://world-onlinedrugs.com/ darkmarket 2023
dark markets https://darkwebworldmarket.com/ darknet sites
tor marketplace https://darkweb-world.com/ darknet search engine
how to get on dark web https://cyphermarketplace24.com/ darkmarket list
darknet drug market https://worlddarkwebdrugstore.com/ blackweb official website
dark markets 2023 https://heinekendrugsmarket.com/ dark website
dark market url https://worldoniondarkmarket.com/ dark web sites links
darknet site https://heineken-onion-darkweb.com/ dark web drug marketplace
dark web search engines https://cyphermarket-darknet.com/ free dark web
darknet drugs https://heinekendarkwebdrugstore.com/ darknet market
how to access dark web https://darkmarket-world.com/ darknet markets 2023
darknet drug store https://cypherdrugsmarketplace.com/ dark market
darknet market list https://cyphermarket-link.com/ deep web drug store
darknet links https://worlddrugsmarket.com/ dark market onion
deep web links https://heineken-online-drugs.com/ dark web market
darknet links https://worlddarkmarketonline.com/ deep web drug url
dark market https://dark-market-heineken.com/ dark website
best darknet markets https://cypher-darkmarket-online.com/ darkweb marketplace
dark markets 2023 https://cypherdarkmarketonline.com/ dark internet
darknet drug market https://cypher-drugsonline.com/ darknet links
dark web market links https://dark-market-cypher.com/ darkmarket
deep dark web https://worlddarkweb.com/ dark web sites links
dark website https://world-darkweb.com/ bitcoin dark web
darknet drug links https://world-drugs-online.com/ darkmarket 2023
deep web drug store https://cypherdarkmarketx.com/ dark internet
deep web markets https://heinekenoniondarkmarket.com/ dark web search engine
darkmarket link https://world-onion-darkweb.com/ dark web links
darkmarket 2023 https://heineken-onion-darkmarket.com/ dark web access
darknet drug store https://world-drugsonline.com/ darkmarkets
darknet drug market https://world-darknet-drugstore.com/ tor darknet
blackweb https://worldmarketplacee.com/ drug markets onion
tor markets 2023 https://cypher-online-drugs.com/ dark web market
tor market url https://dark-market-world.com/ dark web site
dark internet https://heinekendrugsmarketplace.com/ dark web websites
drug markets onion https://dark-web-world.com/ dark market onion
tor markets https://heinekendarknetdrugstore.com/ dark website
dark web access https://cyphermarket-darknet.com/ deep web sites
tor market https://heineken-darknet-drugstore.com/ tor dark web
drug markets dark web https://cypherdrugsmarketplace.com/ dark market url
darkmarket link https://cyphermarket-url.com/ darknet drug market
tor markets links https://cypher-darkmarket.com/ dark markets
darkmarket https://darkmarket-cypher.com/ dark websites
dark net https://cypher-darkweb.com/ darknet drug links
darkmarket list https://heineken-online-drugs.com/ deep web drug links
darknet market list https://worlddrugsmarketplace.com/ deep web drug markets
dark web drug marketplace https://dark-market-heineken.com/ darknet drug market
darknet drug store https://cypher-drugs-online.com/ dark web market
deep web drug url https://dark-web-cypher.com/ dark websites
dark web link https://worldmarket-url.com/ dark web sites
dark web sites https://heineken-drugs-online.com/ dark market 2023
black internet https://worlddarkweb.com/ deep web drug markets
dark web search engines https://world-drugs-market.com/ deep web drug url
tor market links https://worldoniondarkmarket.com/ blackweb official website
dark web site https://world-darkweb.com/ dark markets
darknet drug links https://cypher-dark-market.com/ best darknet markets
dark market onion https://heinekenoniondarkweb.com/ darknet links
dark web markets https://world-darknet-drugstore.com/ darknet drug market
darknet links https://heineken-onion-darkmarket.com/ dark website
darknet links https://world-darkmarket.com/ free dark web
how to access dark web https://worldmarket-darknet.com/ darkmarket link
tor market https://cypher-online-drugs.com/ the dark internet
darknet drug market https://worldonlinedrugs.com/ darknet site
drug markets onion https://cyphermarket-darknet.com/ dark market url
bitcoin dark web https://cypherdrugsmarket.com/ dark web drug marketplace
dark web market list https://heinekendrugsmarketplace.com/ darknet drug links
deep web drug markets https://heineken-darknet-drugstore.com/ dark web market links
deep web sites https://cypher-darkwebmarket.com/ darknet drugs
darkmarket url https://darkmarket-cypher.com/ dark web sites
darknet drug market https://cypherdarkmarketplace.com/ dark web sites
tor markets links https://cypherdarknet.com/ darkweb marketplace
deep web search https://heinekenonionmarket.com/ darkmarket link
darknet search engine https://world-darkmarket-online.com/ darknet markets 2023
onion market https://worlddrugsmarketplace.com/ deep web markets
darknet markets https://worldmarket-linkk.com/ darkmarket url
dark web drug marketplace https://worldoniondarkmarket.com/ tor market links
darkmarket link https://heineken-onlinedrugs.com/ darkmarkets
darknet market links https://worldmarketplace24.com/ darknet drug market
dark internet https://heinekenoniondarkmarket.com/ deep web drug links
deep web drug links https://cypherdarkmarketx.com/ dark web sites
deep web links https://heineken-onion-market.com/ blackweb official website
darkmarket https://cypheronionmarket.com/ dark websites
darknet market links https://worlddarkwebmarket.com/ dark market
darknet drug links https://world-dark-market.com/ darknet markets 2023
darknet markets 2023 https://world-drugs-online.com/ dark market list
deep dark web https://worldmarketplacee.com/ darknet marketplace
darkmarkets https://worldonlinedrugs.com/ tor marketplace
tor markets https://darkmarket-world.com/ dark market 2023
blackweb https://cypherdrugsmarket.com/ deep web drug markets
tor market url https://cypherdarkwebmarket.com/ dark website
dark web access https://heinekendarknetdrugstore.com/ dark web markets
drug markets dark web https://cypheronlinedrugs.com/ tor market url
deep dark web https://dark-web-cypher.com/ darkweb marketplace
darkmarket 2023 https://cyphermarket-link.com/ darknet sites
dark market url https://cypher-darkwebmarket.com/ tor markets
deep web search https://heinekendrugsmarketplace.com/ darknet drug market
darknet market https://cypher-darkweb.com/ deep web drug links
deep web drug links https://worlddrugsmarket.com/ tor dark web
dark market 2023 https://worlddarkmarketonline.com/ tor markets 2023
darknet websites https://heinekendrugsonline.com/ darkmarkets
black internet https://world-darkwebmarket.com/ darkmarkets
tor market https://world-onion-darkweb.com/ dark website
tor markets https://worlddarkwebdrugstore.com/ darknet sites
deep web drug url https://world-market-place1.com/ deep web drug links
deep web links https://dark-market-world.com/ the dark internet
dark web access https://world-darkweb.com/ darknet websites
darknet market list https://heinekenoniondarkmarket.com/ tor darknet
dark web markets https://cypherdarkmarketx.com/ darknet drugs
deep web drug links https://heineken-onion-darkmarket.com/ dark market url
dark web site https://cypher-online-drugs.com/ drug markets onion
darknet marketplace https://dark-web-world.com/ dark web links
the dark internet https://world-dark-market.com/ blackweb official website
darknet market https://worlddarkwebmarket.com/ onion market
darkmarket 2023 https://cypherdrugsonline.com/ darknet seiten
dark website https://darkmarketcypher.com/ darknet site
dark web markets https://cypher-darkmarket.com/ deep web drug links
darknet marketplace https://cyphermarket-darknet.com/ tor marketplace
darknet websites https://worldmarket-linkk.com/ dark web search engines
deep web links https://heinekendrugsmarketplace.com/ darkmarket
dark web search engines https://cypherdarknet.com/ darkmarket link
dark web link https://heineken-online-drugs.com/ darknet market
darknet market links https://heineken-onlinedrugs.com/ dark web markets
dark websites https://world-online-drugs.com/ dark web link
blackweb https://world-darkmarket-online.com/ darknet markets
darknet markets https://worlddrugsmarketplace.com/ darkmarket link
dark web search engines https://worldmarketdarknets.com/ darkmarket link
dark market link https://cyphermarketplacee.com/ how to access dark web
dark web link https://cypher-markett.com/ deep web search
dark markets https://world-market-place1.com/ darknet drug market
dark websites https://world-darkweb.com/ dark market url
dark markets 2023 https://heinekenoniondarkmarket.com/ dark web market list
deep dark web https://cypherdarkmarketx.com/ deep web drug markets
darkmarket link https://heineken-onion-darkmarket.com/ darknet site
dark web market list https://worldmarketdrugsonline.com/ dark market url
deep web drug markets https://cypherdrugsmarketplace.com/ drug markets onion
how to get on dark web https://cypher-darknet.com/ dark market
tor markets 2023 https://world-dark-market.com/ dark web link
dark web sites links https://darkweb-cypher.com/ dark websites
dark web search engines https://heineken-darkweb-drugstore.com/ deep web markets
dark web websites https://world-onlinedrugs.com/ black internet
deep web sites https://world-drugsonline.com/ darknet seiten
darkmarket https://heinekendarknetdrugstore.com/ deep web search
dark web search engines https://worldmarket-linkk.com/ darknet market links
deep web drug store https://heineken-darknet-drugstore.com/ darknet links
darknet links https://world-darknet-drugstore.com/ dark net
tor markets links https://heinekendrugsmarket.com/ darkmarkets
drug markets onion https://world-darkwebmarket.com/ dark web search engine
deep web drug links https://worlddarkmarketonline.com/ tor dark web
dark internet https://dark-market-heineken.com/ deep web markets
dark internet https://heineken-onlinedrugs.com/ tor market
dark web sites links https://cyphermarketplacee.com/ dark web drug marketplace
deep web drug links https://heineken-online-drugs.com/ darkmarket list
deep web links https://heineken-drugs-market.com/ darknet market lists
tor marketplace https://worlddrugsmarketplace.com/ dark web market
tor dark web https://world-market-place1.com/ dark web drug marketplace
dark website https://cypher-onlinedrugs.com/ dark web market
blackweb https://world-darknet.com/ dark web market
deep web drug store https://cypher-dark-market.com/ free dark web
black internet https://heinekenoniondarkweb.com/ darknet site
dark market onion https://dark-web-world.com/ darknet market
deep web search https://heineken-onion-darkmarket.com/ tor market
dark web market https://world-drugs-online.com/ dark web sites links
dark web links https://world-dark-market.com/ drug markets dark web
dark net https://worldmarketplacee.com/ the dark internet
darknet drugs https://cypher-darkmarket.com/ darkmarket link
tor markets 2023 https://worlddarkwebmarket.com/ darkmarket url
deep web search https://world-onion-darkweb.com/ tor dark web
dark web websites https://worldmarket-url.com/ dark market list
darknet markets https://heinekendarknetdrugstore.com/ dark market link
dark web links https://heineken-onlinedrugs.com/ dark web market list
free dark web https://heinekendrugsmarket.com/ darkweb marketplace
dark market onion https://cypherdarkmarketonline.com/ deep web drug store
tor marketplace https://darkwebcypher.com/ dark web sites links
darkmarket url https://heineken-darknet-drugstore.com/ how to access dark web
dark web markets https://world-darkmarketplace.com/ darkmarket 2023
darknet marketplace https://worldmarketdarknets.com/ deep dark web
darknet market links https://world-darkmarket-online.com/ dark markets
darknet drug store https://heineken-drugs-market.com/ dark net
darknet markets 2023 https://heinekenonionmarket.com/ tor market url
darkmarket url https://worlddrugsmarket.com/ deep web markets
dark web market list https://darkwebworldmarket.com/ dark web search engines
free dark web https://world-market-place1.com/ darknet market list
darknet drug market https://cypher-drugs-online.com/ dark web links
tor market links https://cypherdrugsonline.com/ dark website
dark web market https://world-darknet.com/ drug markets dark web
tor market https://cypherdarkmarketx.com/ darknet markets 2023
dark web search engines https://cypher-darkmarket-online.com/ deep web search
blackweb https://world-drugs-market.com/ dark market list
darkmarket url https://world-onlinedrugs.com/ tor market url
dark market https://heinekenoniondarkmarket.com/ dark web link
darknet links https://cyphermarket-url.com/ darknet drug market
dark web websites https://heineken-onion-market.com/ darknet market links
best darknet markets https://world-dark-market.com/ tor markets 2023
dark web site https://cypher-darkmarketplace.com/ bitcoin dark web
dark web market links https://heineken-darkweb-drugstore.com/ dark market 2023
tor markets links https://world-darkmarket.com/ darknet site
dark internet https://world-onion-darkweb.com/ dark web sites
drug markets dark web https://worldmarket-linkk.com/ dark website
deep web search https://heineken-onion-darkweb.com/ dark web drug marketplace
tor market https://darkmarket-cypher.com/ dark web site
dark web websites https://world-darkwebmarket.com/ tor marketplace
dark website https://heinekendarkwebdrugstore.com/ darknet markets 2023
darknet drug store https://worlddarkmarketonline.com/ darknet drug store
deep web drug links https://cypherdarknet.com/ darknet drug market
dark net https://heineken-online-drugs.com/ dark markets
darknet sites https://darkmarketworld.com/ dark web drug marketplace
tor markets 2023 https://world-onlinedrugs.com/ blackweb official website
darknet marketplace https://cypher-darknet.com/ tor markets links
darkmarket 2023 https://world-darkweb.com/ tor markets links
black internet https://worldmarket-darknet.com/ darknet drug links
tor markets 2023 https://worlddarkwebdrugstore.com/ dark market
dark web markets https://worldonionmarket.com/ dark market list
darknet drug store https://worldmarketplacee.com/ dark web search engine
darknet site https://heineken-onion-darkmarket.com/ dark markets 2023
darknet drug store https://cypher-darkmarket.com/ dark markets
deep web drug store https://kingdomdarkwebmarket.com/ dark market list
deep web search https://worldmarket-linkk.com/ drug markets dark web
dark web drug marketplace https://heineken-onion-darkweb.com/ deep web search
darkmarket https://cypherdarkmarketonline.com/ darknet drug store
tor marketplace https://world-darkmarketplace.com/ tor darknet
dark market onion https://worlddarkweb.com/ tor darknet
tor market links https://heinekendarkwebdrugstore.com/ dark websites
how to get on dark web https://dark-market-cypher.com/ darkmarkets
darknet links https://cypher-darkweb.com/ onion market
dark web search engine https://heinekenonionmarket.com/ dark market link
the dark internet https://worldmarketplace24.com/ deep web drug links
deep web drug links https://worldonlinedrugs.com/ tor market
dark web market links https://cypherdarkweb.com/ dark web market
deep web drug links https://world-drugs-online.com/ dark web link
tor darknet https://cypher-darknet.com/ darkmarket url
deep web links https://cyphermarket-darknet.com/ dark web market list
dark net https://dark-market-heineken.com/ drug markets dark web
tor market url https://world-darkweb.com/ darknet site
dark market 2023 https://worldmarket-darknet.com/ darknet market lists
tor markets links https://world-online-drugs.com/ darknet market list
drug markets onion https://heinekenoniondarkweb.com/ tor market links
dark market list https://cypher-darkmarket.com/ tor markets 2023
drug markets dark web https://heineken-onion-market.com/ deep web drug links
bitcoin dark web https://heineken-drugs-market.com/ tor market url
drug markets onion https://cyphermarketplacee.com/ dark website
free dark web https://cypherdarkmarketonline.com/ deep web links
darknet market https://heinekendarknetdrugstore.com/ deep dark web
darknet markets 2023 https://dark-web-cypher.com/ deep web drug links
darknet market lists https://world-darkmarketplace.com/ darkmarket
onion market https://darkweb-world.com/ dark web links
dark websites https://worldmarketdarknets.com/ dark web access
dark net https://worlddrugsmarketplace.com/ darkmarket url
dark net https://heineken-darknet-drugstore.com/ darknet site
dark web sites https://cypherdarknet.com/ dark internet
tor market url https://heineken-online-drugs.com/ darknet site
deep web links https://cypher-dark-market.com/ darkmarket 2023
dark markets 2023 https://worldmarketdrugsonline.com/ darknet seiten
tor market https://world-drugs-market.com/ dark web access
darkmarket url https://cypher-darknet.com/ darknet drugs
dark web access https://dark-market-heineken.com/ dark web search engine
darkmarket 2023 https://cyphermarket-darknet.com/ dark web websites
blackweb https://worlddarknetdrugstore.com/ how to access dark web
dark web search engine https://worldmarketplacee.com/ darkmarkets
darknet market links https://world-onion-market.com/ dark web websites
dark web site https://world-darknet.com/ darkmarket list
tor market links https://heinekendrugsonline.com/ darknet search engine
best darknet markets https://world-online-drugs.com/ dark web search engine
darknet market lists https://cypher-darkmarketplace.com/ deep web links
deep web drug markets https://heinekenoniondarkmarket.com/ free dark web
tor marketplace https://world-darkweb-drugstore.com/ darknet links
dark websites https://worlddarkwebmarket.com/ deep web markets
dark markets 2023 https://heineken-onion-market.com/ bitcoin dark web
darknet market list https://darkwebcypher.com/ darknet markets 2023
dark market link https://world-darkmarketplace.com/ darknet websites
dark web market https://heineken-onion-darkweb.com/ darknet links
deep web links https://worldmarketdarknets.com/ dark web market list
dark web market https://worlddrugsmarket.com/ deep web drug url
drug markets onion https://heineken-darknet-drugstore.com/ darknet seiten
dark web markets https://cypher-darkweb.com/ deep web search
dark market 2023 https://world-market-place1.com/ dark market onion
darknet sites https://cypher-dark-market.com/ darkmarket url
dark web site https://worldmarketdrugsonline.com/ dark web market
tor marketplace https://dark-web-world.com/ dark web search engines
darkmarket 2023 https://world-onlinedrugs.com/ tor market links
darknet websites https://cypherdarkmarketplace.com/ deep web drug url
dark web websites https://cypher-darknet.com/ tor market
dark web sites https://world-onion-darkweb.com/ dark market onion
dark web links https://world-darknet-drugstore.com/ deep web search
onion market https://cypher-marketplace.com/ blackweb official website
dark markets https://kingdomdarkwebmarket.com/ drug markets onion
deep web search https://dark-market-heineken.com/ how to get on dark web
tor marketplace https://world-onion-darkmarket.com/ free dark web
dark market onion https://cypher-market-onion.com/ deep web search
darkmarket 2023 https://heinekendrugsonline.com/ tor markets links
dark web links https://cyphermarketplacee.com/ the dark internet
dark web websites https://heineken-drugs-online.com/ tor market
dark market list https://worldonionmarket.com/ tor dark web
darkmarket https://world-darkmarket.com/ dark web site
dark web site https://cypher-darkmarket.com/ dark web links
dark web sites links https://cypherdarkmarketonline.com/ tor dark web
deep web drug url https://dark-market-world.com/ dark market link
darknet drug links https://worlddrugsmarketplace.com/ onion market
dark web market links https://worldmarket-linkk.com/ black internet
dark web market list https://cyphermarket-url.com/ darknet search engine
dark web access https://worldonlinedrugs.com/ dark web market links
dark web sites https://dark-web-world.com/ darkmarket link
dark web links https://kingdom-darkmarket.com/ deep web links
the dark internet https://cypher-darknet.com/ deep web drug store
dark markets 2023 https://cypherdarkmarketplace.com/ tor market links
dark web drug marketplace https://world-darknet-drugstore.com/ deep web links
dark markets 2023 https://cypher-marketplace.com/ darknet market links
darknet sites https://heinekendrugsmarketplace.com/ darkmarkets
tor market url https://cypher-markett.com/ dark web links
darknet search engine https://heineken-onlinedrugs.com/ deep dark web
tor market links https://world-dark-market.com/ dark web websites
dark market 2023 https://world-darkmarketplace.com/ dark web search engine
darkmarket https://cypher-darkmarket.com/ tor markets links
dark internet https://dark-market-world.com/ how to access dark web
deep web search https://worldmarketdrugsonline.com/ deep web drug markets
darkmarket url https://cypherdarkwebmarket.com/ darkmarkets
drug markets dark web https://world-onion-darkweb.com/ darknet market list
darknet market links https://cypherdarkmarketplace.com/ deep web drug url
onion market https://heinekenoniondarkweb.com/ drug markets dark web
dark market 2023 https://world-onion-market.com/ darknet seiten
free dark web https://heineken-drugs-market.com/ dark web site
darknet market list https://heinekenonionmarket.com/ black internet
deep dark web https://heinekendrugsonline.com/ darknet markets 2023
tor marketplace https://heineken-onion-darkmarket.com/ darknet markets 2023
dark web sites https://heineken-darknet-drugstore.com/ tor dark web
darknet drug links https://cyphermarketplace24.com/ darknet market
tor markets 2023 https://cypher-market-onion.com/ deep dark web
darknet drug store https://cypher-market-online.com/ how to get on dark web
tor market https://cypher-darkmarket.com/ tor markets
free dark web https://darkmarket-cypher.com/ dark websites
tor darknet https://world-online-drugs.com/ tor markets
deep web drug markets https://darkwebworldmarket.com/ tor dark web
deep web markets https://darkweb-world.com/ blackweb
darknet drug market https://world-drugs-market.com/ dark web access
darkmarkets https://worlddrugsmarketplace.com/ drug markets dark web
darknet markets https://darkmarket-world.com/ dark web search engine
onion market https://cypher-darknet.com/ darknet drugs
tor markets https://worldoniondarkweb.com/ blackweb official website
bitcoin dark web https://heinekendarknetdrugstore.com/ onion market
darknet links https://dark-market-heineken.com/ tor marketplace
darknet search engine https://heineken-drugs-market.com/ darknet drugs
dark web websites https://heineken-onion-market.com/ dark web market
drug markets onion https://heinekenonlinedrugs.com/ dark market list
tor market https://cyphermarketplacee.com/ deep web sites
darknet drugs https://cypher-market-onion.com/ dark market url
blackweb official website https://cypher-darkmarket.com/ dark net
darkmarket link https://darkmarket-cypher.com/ darknet links
the dark internet https://world-online-drugs.com/ darknet market lists
darknet sites https://darkmarketworld.com/ darknet market
bitcoin dark web dark web site
darknet market https://cyphermarket-url.com/ deep web sites
tor marketplace https://world-onlinedrugs.com/ drug markets onion
darkmarkets https://world-drugs-market.com/ how to get on dark web
dark market onion https://worldonlinedrugs.com/ free dark web
darknet site https://cypherdarkwebmarket.com/ dark web site
tor markets 2023 https://darkmarketcypher.com/ dark web access
darkweb marketplace https://worldoniondarkweb.com/ darknet markets 2023
dark web websites https://world-onion-market.com/ deep dark web
black internet https://cypherdarkweb.com/ tor marketplace
best darknet markets https://cyphermarketplacee.com/ drug markets onion
drug markets onion darknet site
darknet drug links https://cypher-darkmarket.com/ dark web drug marketplace
darkweb marketplace https://cyphermarket-darknet.com/ darkmarket 2023
the dark internet https://worldonionmarket.com/ dark markets 2023
dark web search engine https://darkmarket-cypher.com/ dark market link
best darknet markets https://cypher-dark-market.com/ darknet market lists
darknet drug links https://cypher-darkweb.com/ deep web drug store
darknet market list https://dark-web-world.com/ deep web sites
dark market https://world-drugsonline.com/ tor darknet
darknet search engine https://worldonlinedrugs.com/ dark market url
darknet search engine https://cyphermarket-url.com/ dark market 2023
deep web sites https://cypher-darknet.com/ dark websites
darknet drug store https://world-darknet-drugstore.com/ onion market
deep dark web dark market 2023
deep web drug links https://world-onion-market.com/ dark markets 2023
deep web drug markets https://worldoniondarkweb.com/ black internet
dark web search engine https://cypherdarkmarketplace.com/ tor market links
deep web sites https://cypher-markett.com/ dark web site
bitcoin dark web https://world-darkweb-drugstore.com/ deep web drug links
dark markets https://cypher-darkmarketplace.com/ onion market
tor markets links https://cypherdarkmarketonline.com/ deep web markets
dark web link https://cypher-market-onion.com/ dark web drug marketplace
darknet websites https://darkwebworldmarket.com/ tor market links
dark web websites https://worldonionmarket.com/ blackweb official website
darknet market list https://dark-web-world.com/ deep web sites
free dark web https://worlddrugsmarket.com/ deep web drug links
dark internet https://cypherdarknet.com/ how to get on dark web
dark internet https://cyphermarket-url.com/ darknet websites
dark web sites links https://worlddarkwebdrugstore.com/ best darknet markets
darkmarket link https://cypherdarkwebmarket.com/ darkmarket
darknet links https://cypher-darkmarket-online.com/ the dark internet
darknet marketplace https://world-onion-darkmarket.com/ tor market
drug markets dark web https://cypherdarkweb.com/ dark web sites
bitcoin dark web darknet market lists
darkmarket url https://cypher-darkwebmarket.com/ darknet links
dark web market https://cypher-market-onion.com/ darkmarket 2023
dark web market list https://darkmarket-cypher.com/ darknet search engine
darknet market https://cypher-darkweb.com/ darknet seiten
black internet https://cypher-dark-market.com/ blackweb official website
darkmarket link https://world-drugsonline.com/ deep web drug links
dark web drug marketplace black internet
deep web drug links dark web drug marketplace
dark web websites https://darkmarketcypher.com/ dark market
dark market url the dark internet
blackweb tor markets
tor markets links dark internet
darkweb marketplace darknet markets
drug markets onion https://cypherdarkweb.com/ tor markets
deep web sites https://cypher-darkmarketplace.com/ tor markets 2023
darkmarket onion market
tor markets 2023 dark web access
darknet market list https://cypher-market-onion.com/ dark net
tor markets links how to access dark web
darknet market list darknet markets
how to access dark web darknet market
dark net https://cypher-darkweb.com/ deep web markets
blackweb https://cypher-dark-market.com/ darkmarket url
darknet market lists darknet search engine
tor darknet https://darkwebcypher.com/ darknet seiten
free dark web deep web drug url
deep web sites deep web drug links
darkmarket https://worlddarkwebdrugstore.com/ tor markets links
darknet site darknet search engine
how to access dark web dark web access
how to get on dark web https://darkmarketcypher.com/ how to get on dark web
blackweb official website https://heinekenonlinedrugs.com/ darknet markets
dark markets darknet drugs
tor markets links dark internet
darknet sites darknet drug market
free dark web onion market
dark web search engine dark web site
tor market tor marketplace
tor dark web darkmarket 2023
dark web markets dark web websites
darkmarket list dark web access
dark website drug markets dark web
darknet drug links tor marketplace
deep web links darkweb marketplace
dark markets deep web sites
darknet markets tor darknet
darknet markets best darknet markets
darknet market list darknet marketplace
dark markets dark web links
bitcoin dark web darkmarket 2023
deep web drug store onion market
the dark internet tor marketplace
darknet links dark web links
dark markets 2023 tor darknet
deep web drug links darknet market links
darkmarket link tor darknet
dark web markets deep web links
deep web links dark web access
how to access dark web darknet site
deep web drug url dark web sites links
tor markets links black internet
darkmarket list darknet marketplace
dark market 2023 darkmarket
darknet markets 2023 dark net
darknet drug market darkmarket list
best darknet markets dark market
dark web drug marketplace tor markets
drug markets dark web dark web search engine
darknet drug store dark web market
darkmarket 2023 blackweb official website
free dark web onion market
free dark web dark web market list
tor market url darknet market lists
tor markets darkweb marketplace
darknet seiten best darknet markets
dark web websites darknet markets
how to access dark web darknet site
tor market url darknet websites
darknet search engine dark web market links
how to get on dark web darknet markets 2023
darknet market lists darknet seiten
deep web drug markets deep web drug store
darkmarket deep web drug markets
darkmarket link darkmarket
dark markets 2023 blackweb
dark web sites links darknet drug store
dark web links how to get on dark web
darkmarket link how to access dark web
dark web market list tor markets
dark web market tor markets
darknet sites deep web drug store
darkweb marketplace deep web search
darknet drugs darkmarket 2023
dark web market list dark web link
darkmarket list darknet search engine
darkmarket url https://heinekendrugsonline.com/ darknet search engine
dark web site dark market onion
darkmarket tor dark web
darknet site tor markets links
darknet drug market dark web sites
blackweb darknet search engine
deep web drug store deep web sites
deep web drug markets darkmarket 2023
dark net drug markets dark web
darknet markets 2023 dark web search engines
dark websites darknet sites
deep web sites tor darknet
best darknet markets tor markets 2023
darknet drug store darkmarket
darknet market list deep web drug store
darkmarket link darknet drug store
deep web sites darknet marketplace
dark web access blackweb official website
darknet market lists dark websites
dark web link bitcoin dark web
dark web market links darkmarket list
darkmarkets tor markets 2023
dark web search engine deep web sites
tor market links deep web drug url
darkmarkets darkmarket link
free dark web darknet search engine
dark market link darkweb marketplace
dark web search engine the dark internet
drug markets onion darknet marketplace
dark market best darknet markets
tor market links drug markets dark web
dark market url darkmarkets
darknet marketplace tor darknet
dark web market darknet market list
darknet drug market dark web market list
darknet market links dark web market links
darknet search engine dark markets
dark web site dark web websites
darknet seiten dark web markets
deep web search dark web drug marketplace
dark web sites links the dark internet
darknet search engine dark web access
darkmarket url darknet market
dark web links dark web access
darknet market lists tor market url
dark web drug marketplace tor markets
free dark web tor marketplace
dark web access darkweb marketplace
darkmarket 2023 deep web search
tor marketplace darkweb marketplace
deep dark web darkmarket
darknet search engine dark websites
darknet market dark markets
drug markets dark web darknet market lists
dark market link darkmarket 2023
dark web sites links darkmarket url
dark markets dark market onion
dark market onion deep web links
dark markets 2023 deep dark web
darknet seiten dark markets 2023
dark market 2023 darknet market links
darkmarket 2023 deep web drug store
darknet site free dark web
deep web sites darknet links
dark web websites dark internet
deep web drug markets deep web drug store
darkmarket list dark internet
dark web search engine dark market onion
darknet drugs https://heinekendrugsonline.com/ dark web markets
darkmarket list onion market
deep web drug links deep web links
dark net drug markets dark web
dark websites darknet marketplace
darkweb marketplace the dark internet
dark web sites darknet drug market
darknet market deep web links
deep web markets drug markets dark web
darkmarket url tor market
drug markets dark web darknet market list
dark markets 2023 dark web access
darknet search engine tor markets links
darknet search engine dark market
dark web sites deep web drug markets
darknet drug market darknet drug store
darknet drug links free dark web
deep web drug links dark web search engines
darknet drug links dark website
dark web sites darkmarket
dark market list how to get on dark web
dark market onion darknet drug market
dark websites darknet market lists
deep web drug url darknet site
darkmarket link tor dark web
dark website dark market onion
darkmarket list darknet market lists
dark web sites links bitcoin dark web
darknet market deep web markets
dark web market list dark web search engine
darknet marketplace dark web sites links
dark internet darknet market list
darkmarket link best darknet markets
darknet markets https://heinekendrugsonline.com/ black internet
darkmarket drug markets onion
how to access dark web deep web drug links
tor markets links dark market onion
dark web market black internet
darknet drug store darknet markets
dark markets 2023 darkmarket url
tor market deep web drug url
darknet site darkmarket url
onion market drug markets onion
darknet site dark internet
black internet drug markets dark web
dark market onion deep web sites
tor darknet deep web drug links
tor markets 2023 dark web websites
dark website dark market onion
onion market tor marketplace
dark web links dark market url
darknet sites darknet sites
tor marketplace darkweb marketplace
dark web market links deep dark web
blackweb official website dark web websites
darkweb marketplace darkmarket url
darknet drug store darknet markets
deep web drug url onion market
darknet market list black internet
tor markets 2023 darknet market links
tor markets darkmarket url
deep web drug url darknet seiten
black internet dark web market links
dark market 2023 darknet site
dark markets dark websites
drug markets dark web darknet links
darknet markets dark market list
how to access dark web darkmarket list
dark websites https://heinekenonlinedrugs.com/ the dark internet
tor dark web dark markets 2023
tor market links darknet market links
darknet markets blackweb
onion market dark web sites links
darknet drugs darkmarkets
darkmarket the dark internet
tor market links darkmarket url
tor markets dark website
darknet sites deep web search
how to get on dark web tor dark web
tor marketplace darknet seiten
tor dark web tor marketplace
blackweb official website dark market
darknet drug market deep web drug store
dark web market list deep web drug markets
deep web drug url darknet site
deep web drug links darknet markets
darknet drug store dark web link
deep web drug links darknet market links
dark web search engine dark market onion
dark web site darknet market lists
dark web search engine blackweb official website
dark websites dark web market
black internet dark web market list
deep web drug links dark market
darknet sites deep web sites
dark web link darknet drug links
darknet market list dark web sites links
dark website dark web markets
deep web links darknet market lists
the dark internet tor marketplace
dark market list https://heinekendrugsonline.com/ how to access dark web
dark web site darknet seiten
tor market url blackweb
dark market list dark web sites
dark net darknet drug market
tor dark web darknet market
dark web links deep web drug links
drug markets onion tor markets 2023
darknet drug store darkmarket link
deep dark web deep web drug links
dark market link tor markets
dark web markets deep web drug store
drug markets dark web darkmarkets
dark net dark web links
darknet marketplace darkmarket url
dark web links deep web drug markets
how to access dark web how to get on dark web
darkmarkets darknet marketplace
darknet sites darknet drugs
tor market links darknet market
darknet site dark markets 2023
onion market darknet links
dark web market tor markets links
dark internet deep web search
best darknet markets dark web markets
darkmarkets darknet market lists
the dark internet dark web search engine
darknet market deep web markets
dark web access dark web access
darknet websites darknet search engine
how to get on dark web darknet market links
deep web drug markets darknet site
dark web links https://heinekenonlinedrugs.com/ tor market
tor darknet darknet search engine
dark web link dark web access
dark web link free dark web
darknet drug store darknet drug store
tor dark web darknet marketplace
darkmarkets dark web links
dark markets 2023 darknet markets
blackweb tor market
blackweb dark market onion
deep web search deep web markets
dark web drug marketplace darknet markets 2023
darknet drug store deep dark web
dark market link drug markets dark web
how to access dark web darknet sites
darkmarket list darknet marketplace
dark net darknet seiten
dark web drug marketplace dark web drug marketplace
darknet drug links darknet search engine
deep web markets dark websites
darkmarket 2023 dark web link
dark website dark web link
tor market how to access dark web
dark web site deep web search
darknet markets darkmarket
dark web market links darknet sites
deep web drug markets dark web links
darknet site darknet drug store
deep web sites tor darknet
darknet sites darknet sites
dark web market deep web drug links
darknet drug market darknet market links
tor marketplace dark web search engines
darknet site darknet search engine
drug markets onion darknet seiten
deep web drug links darknet websites
blackweb official website https://heinekenonlinedrugs.com/ darknet search engine
darknet seiten darknet marketplace
darkmarket link darknet markets
darkmarkets deep web drug store
blackweb darknet sites
dark web sites dark web market links
dark web sites darknet links
drug markets dark web darkmarket
tor market url darknet site
dark web market tor dark web
darknet drug store darknet market links
darkmarket list darknet market
tor marketplace darkmarket 2023
dark web search engines dark web access
dark internet dark web links
dark market 2023 deep web links
dark web search engines deep web drug url
dark web websites darknet links
dark web market tor markets links
dark web access dark market list
dark market link how to get on dark web
dark market url deep web drug store
deep web drug url black internet
drug markets dark web darkweb marketplace
blackweb onion market
dark web links tor market links
free dark web darknet market links
darkmarket how to access dark web
dark web sites links deep web sites
blackweb darknet drug market
tor markets darkweb marketplace
tor market the dark internet
dark web market links https://heinekendrugsonline.com/ dark internet
darknet markets deep web markets
tor dark web dark web market
tor market links darknet seiten
darknet drug market how to get on dark web
dark market list drug markets dark web
drug markets onion darknet drug store
dark website deep web drug store
darknet markets dark web sites links
dark web market list dark internet
darkmarket list dark market 2023
darkweb marketplace dark market onion
darknet drug market bitcoin dark web
darknet markets 2023 dark web search engines
dark internet darkweb marketplace
darknet drugs darknet links
how to get on dark web darknet links
black internet dark web drug marketplace
black internet darknet markets
deep web drug store dark internet
dark web markets deep web drug url
deep web search black internet
darknet markets onion market
dark web markets how to get on dark web
darkweb marketplace darkweb marketplace
deep web drug store dark market list
darknet market darknet drug links
dark web links tor markets 2023
how to get on dark web deep web sites
best darknet markets tor marketplace
dark market onion darkmarket url
deep dark web dark web link
tor market links free dark web
dark web market links tor markets 2023
dark net darkmarket 2023
darkmarket url dark websites
dark web markets bitcoin dark web
deep dark web darkmarket 2023
dark web market deep web links
tor market url darkweb marketplace
dark web market list dark web links
darkmarket list darknet market list
dark market link tor dark web
dark web drug marketplace dark markets
deep web search dark net
dark market onion darknet seiten
bitcoin dark web darknet drugs
darknet sites drug markets dark web
tor market url dark internet
deep web links dark web market
darknet search engine tor dark web
darknet links tor markets 2023
the dark internet deep web search
drug markets dark web deep web markets
dark markets deep web markets
dark markets 2023 deep web sites
darkmarkets dark market
dark web site tor market
drug markets onion onion market
deep dark web onion market
dark web drug marketplace darknet market lists
darknet market list dark web sites
dark market onion darknet sites
free dark web https://heinekenonlinedrugs.com/ dark website
darknet market lists dark websites
dark market 2023 deep web drug markets
tor markets darknet market
bitcoin dark web how to get on dark web
how to access dark web dark web market list
drug markets onion deep web search
dark web drug marketplace darknet links
darkmarket dark markets
drug markets dark web darkweb marketplace
darkmarkets darkweb marketplace
free dark web blackweb
darknet seiten darkmarket 2023
dark web market list darknet market links
darknet site dark web site
dark web market links how to access dark web
darknet market black internet
tor markets bitcoin dark web
darkmarket 2023 darknet market list
blackweb official website deep web search
dark internet tor markets links
darknet market dark web search engines
dark websites darknet drug links
dark web sites dark web site
tor dark web dark web drug marketplace
how to get on dark web darknet seiten
tor marketplace blackweb official website
darknet market list dark web market list
tor markets links darkmarket url
darkmarket url dark web market
darkmarket list darkmarkets
blackweb tor market links
darkmarket link dark markets
onion market dark market 2023
tor market url dark market onion
darkmarket link darkmarket 2023
dark web access drug markets onion
dark market link blackweb
darknet links dark web market links
deep web search deep web drug markets
dark web market list darknet drug market
darkmarket list bitcoin dark web
dark web websites dark web site
dark web market dark market 2023
dark web drug marketplace drug markets dark web
darknet markets 2023 dark market onion
darkmarkets tor markets links
dark web access darknet sites
darknet links dark web search engines
darknet drug store darknet drug links
how to access dark web dark internet
tor markets 2023 tor dark web
darknet websites darknet markets 2023
onion market bitcoin dark web
blackweb dark website
darknet websites deep web markets
darknet markets 2023 dark net
darkweb marketplace darknet search engine
deep web sites https://heinekenonlinedrugs.com/ darknet drug market
dark web market dark web link
dark markets darknet links
darknet drug store tor market
the dark internet dark web search engines
darkmarket list dark websites
darkmarket list tor markets
tor darknet darknet marketplace
tor marketplace darknet sites
dark website deep web drug url
darknet markets darkmarket url
best darknet markets dark internet
dark market onion deep web drug markets
darkmarket darkmarket
darknet seiten darknet market lists
dark market link darknet market lists
dark web link dark net
deep web drug markets deep web drug url
dark web search engines darknet markets 2023
dark web market dark market list
dark web drug marketplace deep web sites
black internet deep web drug links
darkweb marketplace dark web markets
tor market url dark markets
black internet deep web markets
free dark web dark web link
deep web drug links dark web link
darknet drug links deep web drug url
tor dark web blackweb
darkweb marketplace darknet market links
darkmarkets drug markets dark web
darknet drug market tor market url
dark markets dark web link
dark web search engine dark market url
dark market onion black internet
dark website deep web drug markets
dark markets 2023 deep web drug store
dark websites darknet marketplace
how to get on dark web dark website
dark internet darkmarket list
how to get on dark web tor dark web
darknet seiten dark web site
darknet drug store bitcoin dark web
dark markets onion market
black internet how to get on dark web
dark market link blackweb official website
darknet seiten how to get on dark web
deep web search bitcoin dark web
darknet sites tor markets links
dark markets 2023 dark internet
deep web drug store tor markets
dark web drug marketplace darknet sites
darknet market links bitcoin dark web
dark web market dark web market list
dark market url darknet drug market
deep web drug links dark markets 2023
darkmarkets deep web drug url
blackweb official website dark market url
darknet drug market dark web sites
darknet markets darknet markets 2023
darkmarket url darknet websites
dark market url bitcoin dark web
dark market url darknet drug store
dark web links darknet marketplace
darknet search engine tor markets
black internet blackweb official website
darkweb marketplace darkmarket list
dark market 2023 tor marketplace
dark internet darkmarket
deep web drug markets deep web drug markets
dark market list darkmarket 2023
dark web sites links darknet market list
darkmarkets tor market
darkmarket url dark websites
dark net dark markets 2023
onion market dark web market list
free dark web dark markets
dark web search engines dark internet
dark web market list dark web link
dark market deep web drug store
dark markets deep web search
deep web drug store dark market url
darkmarket link dark website
darkweb marketplace free dark web
darknet market links darkmarkets
dark market deep web links
how to access dark web tor market url
dark market 2023 dark web markets
deep web markets dark web links
darkmarket link dark web search engines
darknet market darknet websites
tor markets 2023 darknet search engine
dark web search engine dark web market
deep dark web drug markets dark web
free dark web how to get on dark web
darkmarket list https://heinekenonlinedrugs.com/ dark web sites
dark markets darknet marketplace
tor dark web tor darknet
darkmarket deep web search
dark internet darknet market list
dark web search engines dark web sites links
free dark web dark web links
onion market darknet links
bitcoin dark web tor markets
dark web site dark web site
darknet market dark market onion
drug markets onion darkmarket
drug markets onion darknet websites
darknet drug links deep web markets
dark web websites tor markets links
dark websites tor market links
deep dark web deep web drug url
dark web sites darknet drugs
dark market url tor market links
darknet markets 2023 dark web sites links
darknet market lists how to access dark web
darkmarkets tor marketplace
deep web links darknet market lists
deep web drug markets darknet search engine
tor market url dark web site
tor markets links dark web market links
dark market link dark internet
deep dark web tor marketplace
darknet marketplace dark market list
dark web drug marketplace darknet sites
darkmarkets dark market url
dark web link how to get on dark web
dark web market links deep web search
darknet site deep web drug store
darknet links darknet drugs
dark markets https://heinekendrugsonline.com/ darkweb marketplace
darknet drug links dark market 2023
dark websites darkmarket list
how to get on dark web blackweb official website
darknet websites deep web sites
tor markets drug markets onion
tor markets blackweb
dark market list darknet market lists
dark web drug marketplace deep web search
black internet darkmarket list
tor market url darknet market links
darknet market dark website
darknet seiten darkmarket
deep web markets dark internet
dark web markets drug markets onion
deep web drug store darknet links
darknet market links dark web sites
dark market url how to get on dark web
darknet market list dark web access
tor marketplace how to access dark web
deep web links darknet drug links
darknet search engine darknet market
darknet markets drug markets onion
how to access dark web dark web site
dark web link darkmarket list
sildigra from canadian pharmacies
darknet search engine tor dark web
deep web links dark web search engines
dark web sites tor market
darknet site deep web markets
darknet websites dark website
darknet drug links dark web search engines
darknet market list tor markets 2023
darkweb marketplace dark websites
dark website dark web search engine
tor markets 2023 deep dark web
dark web markets onion market
bitcoin dark web dark web sites links
dark internet how to access dark web
deep web drug url darknet sites
dark web market list dark market 2023
dark market link free dark web
dark web search engine dark internet
tor markets best darknet markets
can you buy cheap finasteride without insurance
darkmarkets darkmarket
dark web links bitcoin dark web
dark web market links free dark web
tor markets darkmarkets
dark website darkmarket list
tor market links darknet drugs
the dark internet dark net
tor marketplace dark web link
darkmarket link darknet search engine
drug markets onion blackweb
tor markets 2023 tor market url
tor marketplace dark net
dark market onion dark web access
darkmarket list darkmarket url
darknet links deep dark web
dark web search engines darknet drug store
dark web link dark market url
dark market onion tor markets
darkmarket link darknet drug market
blackweb official website dark markets 2023
dark web search engine darknet drugs
darkmarket list darkmarket list
dark web market tor markets links
darknet links black internet
darknet seiten darkmarket list
dark web site black internet
darknet market darknet markets
darknet market list dark market url
darknet market lists dark web market links
dark web market links tor markets
dark web sites links dark market onion
darknet drug market dark web search engines
black internet dark markets
dark market list tor market url
dark web market dark market onion
dark web sites links tor marketplace
darknet links the dark internet
tor market url deep dark web
darkmarket url dark market link
darknet markets 2023 deep web drug store
darknet marketplace dark web market list
darknet drugs dark web search engines
dark web market list onion market
dark net dark markets 2023
dark web links darknet marketplace
darknet sites deep web drug links
dark web links darkmarket
dark web market list tor markets links
darknet websites darknet search engine
darknet drug links drug markets onion
darknet websites darknet sites
darknet sites darkmarket 2023
dark web search engine dark web sites
darknet drug market tor markets 2023
dark web link darkmarket url
darkmarkets how to get on dark web
dark web access best darknet markets
the dark internet darknet market list
darknet search engine onion market
dark web drug marketplace darknet drug store
darknet market links deep web markets
deep web sites darknet market
darknet links tor darknet
dark web search engine darknet drug links
how to get on dark web darkmarket
dark web site dark web websites
darknet market links black internet
dark markets darknet market links
blackweb darknet search engine
tor marketplace deep web sites
darkmarket url dark web site
dark web sites darkmarkets
darknet search engine deep web links
darkmarkets darknet market lists
how to get on dark web dark net
darkmarket dark markets 2023
deep web drug markets darknet drug market
dark web links deep web markets
tor markets links darknet market lists
darknet market lists darknet market links
bitcoin dark web darknet search engine
the dark internet tor marketplace
deep web search dark web search engines
darkmarket url darknet drug market
darkmarkets tor dark web
deep web drug markets darknet seiten
darkmarket dark web drug marketplace
tor darknet tor dark web
drug markets dark web darknet market lists
darknet drug store darknet sites
how to access dark web darkmarkets
dark websites darknet websites
blackweb official website tor markets 2023
darknet drugs dark web market list
dark web websites deep web drug store
how to get on dark web deep dark web
deep web sites darknet links
darknet seiten dark market url
dark net tor dark web
dark web markets darknet seiten
dark web market list dark market onion
tor markets 2023 dark net
darknet sites darkweb marketplace
darknet sites dark web access
tor marketplace darkmarket url
tor markets deep web markets
dark web websites darkmarkets
dark market onion darknet drug market
darknet site darkmarket url
dark web markets dark web search engine
darknet sites drug markets onion
tor markets darkmarkets
darkmarket url blackweb
onion market darknet market lists
darknet market tor dark web
dark web search engines tor markets
darknet markets tor darknet
dark web sites tor market links
free dark web deep web sites
dark website deep web drug links
tor marketplace dark markets 2023
tor markets darkmarket url
dark market deep web links
darknet site darkmarket 2023
dark market onion darknet marketplace
dark website tor markets 2023
black internet blackweb official website
deep web drug url dark web market list
tor market url tor market
dark web links darknet markets 2023
dark market onion dark markets 2023
deep web drug store dark web market
darknet links tor marketplace
dark internet the dark internet
dark market list dark markets
dark market list deep dark web
deep web sites best darknet markets
dark market url dark markets 2023
dark web markets how to get on dark web
dark web market list how to access dark web
tor markets 2023 deep web drug url
darknet search engine darkmarket link
deep web links tor market links
tor darknet dark web markets
dark websites black internet
dark web search engine darknet drug links
deep web links darknet market lists
dark market onion darknet site
dark website dark web markets
tor marketplace darkmarket url
tor markets links darknet sites
drug markets dark web darkmarket url
bitcoin dark web bitcoin dark web
deep web sites deep web search
darknet drug links dark markets
dark markets dark market 2023
darknet drugs darkmarkets
dark web websites dark web search engine
deep web drug markets dark web websites
darkmarket list best darknet markets
deep web drug url drug markets onion
darknet search engine dark market
darkmarket list darknet search engine
bitcoin dark web dark market list
dark markets darknet marketplace
how to access dark web darknet markets
bitcoin dark web tor markets 2023
darkmarket link darkmarket list
dark web sites links darknet websites
dark web markets dark websites
tor darknet dark web site
dark markets dark website
dark markets 2023 dark web link
darknet markets 2023 darkmarket 2023
blackweb free dark web
darkmarket 2023 deep web drug links
dark markets 2023 how to access dark web
dark web market dark net
dark web drug marketplace darknet search engine
bitcoin dark web dark market list
dark web link bitcoin dark web
tor market links darknet search engine
deep web search bitcoin dark web
blackweb official website deep web drug links
tor markets 2023 dark web market list
dark markets 2023 darkmarket link
dark market 2023 darknet drug store
dark market 2023 deep web search
drug markets dark web tor markets links
blackweb official website dark websites
dark web market links black internet
tor dark web darkweb marketplace
onion market darkmarkets
tor market onion market
dark web market list darkmarkets
darkmarkets dark web search engine
dark market 2023 free dark web
darkmarket 2023 darknet market list
darkmarkets deep web drug links
dark net free dark web
dark web drug marketplace darkmarket
dark internet deep web drug markets
dark market url darkmarket url
drug markets dark web dark net
dark market tor market links
darkmarket list deep web drug markets
darknet seiten darknet market list
deep web search deep web links
dark market 2023 dark web search engines
darkmarket link darknet market links
darknet market list tor market links
dark web markets dark market url
drug markets dark web blackweb official website
darknet market links deep web links
dark markets 2023 dark web search engine
darkmarket link dark net
the dark internet black internet
darknet drug store drug markets dark web
darknet seiten how to get on dark web
dark market onion deep web drug markets
dark web market how to access dark web
dark net darkmarket 2023
darknet market lists darknet links
deep web drug store the dark internet
darkmarket list bitcoin dark web
darknet drugs darknet markets
deep web search deep web drug url
darknet drug links tor market
the dark internet free dark web
how to get on dark web dark market link
darknet seiten free dark web
dark website darkmarket 2023
darknet drugs deep web links
dark website free dark web
deep web markets dark market link
tor markets 2023 darknet links
dark web websites dark web market
tor markets 2023 tor market url
darkmarkets dark web drug marketplace
dark web site darknet site
tor markets links tor dark web
dark market darkmarket link
darknet market list darkweb marketplace
dark market deep dark web
dark web link dark market
dark markets 2023 tor market
dark web drug marketplace tor markets
tor market tor market links
dark web market dark web market list
darknet market lists free dark web
dark market darknet market links
darknet drug market tor markets 2023
blackweb official website free dark web
deep web drug links dark market
dark web websites dark markets
dark market darknet markets 2023
dark web websites free dark web
tor markets dark web drug marketplace
darknet markets 2023 tor markets 2023
darknet market lists deep web drug store
dark market link darknet markets 2023
dark net darknet seiten
dark website darknet seiten
how to get on dark web darknet links
darknet market links darknet site
deep web drug links darknet links
darknet search engine dark market
darknet drug store deep dark web
dark web sites links darknet drugs
drug markets dark web deep web drug store
onion market drug markets dark web
darknet drugs best darknet markets
blackweb dark web sites links
free dark web tor dark web
tor markets 2023 deep web drug store
dark web sites dark website
darknet marketplace darkmarket
dark web drug marketplace darknet drug store
dark market 2023 darknet drug store
tor market url dark markets
darknet market lists the dark internet
dark websites darknet market links
dark market darknet search engine
drug markets onion darknet markets 2023
darkmarket link tor market links
darknet market lists darknet search engine
darknet markets darknet drug market
darknet markets 2023 dark web links
dark market link darknet websites
darknet markets drug markets onion
dark web sites links darknet market lists
darkweb marketplace how to get on dark web
onion market dark net
dark market deep web drug url
darkmarket url darknet drug market
deep web markets darknet drugs
drug markets dark web tor darknet
tor marketplace how to access dark web
darknet marketplace dark web sites links
bitcoin dark web darknet websites
darknet markets 2023 how to access dark web
dark web sites links tor market
darkmarket link dark net
dark web drug marketplace deep web sites
dark web search engines darkmarket 2023
onion market dark web websites
dark web market list black internet
tor markets links tor darknet
darknet site dark market link
dark web market list dark web access
tor market links dark web market list
darknet search engine darkmarket
dark market dark internet
deep web drug markets deep web links
dark market url dark internet
dark website darknet market
darknet search engine darknet market lists
free dark web deep web sites
free dark web dark websites
dark market 2023 darknet market links
dark web sites links tor dark web
dark web links dark market 2023
darknet drug store dark web market list
deep web sites dark market list
deep web search https://alldarkmarkets.shop/ best darknet markets
dark market url dark web market links
darknet markets 2023 darknet market list
tor market dark web drug marketplace
dark market link dark websites
deep web markets dark web search engine
deep web drug store dark web search engines
dark markets 2023 blackweb official website
drug markets onion how to access dark web
dark web market links dark websites
tor markets links deep dark web
darkmarket dark net
dark web access dark markets
onion market dark web sites links
deep web drug url dark web drug marketplace
deep web markets the dark internet
darknet drug market darknet market lists
dark web access dark web websites
dark market list dark web site
best darknet markets darknet seiten
darknet seiten dark market
darknet drugs dark market link
dark market list darknet market links
dark market onion darkmarket list
dark internet how to access dark web
onion market darknet markets
dark web drug marketplace dark market 2023
tor markets 2023 tor markets
darknet drug store darknet marketplace
dark web link dark internet
dark net dark internet
darknet market blackweb official website
darknet market links dark market link
deep web drug url https://onion-dark-markets.shop/ dark web access
how to access dark web darknet search engine
deep web links tor market url
darknet marketplace darknet drug market
dark web site deep web search
dark market list deep dark web
darknet drug store tor markets links
the dark internet how to get on dark web
dark web search engines tor marketplace
darknet websites darknet site
dark market list deep web drug markets
darknet sites darknet links
dark internet the dark internet
drug markets dark web tor markets
darknet market list how to get on dark web
how to access dark web darknet seiten
darknet sites deep web sites
how to access dark web darknet search engine
how to access dark web darknet drugs
darkmarket darkmarket list
darknet search engine tor dark web
dark web site dark market url
best darknet markets dark web drug marketplace
bitcoin dark web deep web sites
darknet market list deep web markets
deep web drug links best darknet markets
dark websites dark market onion
tor market deep web drug markets
deep web sites tor markets
tor darknet dark web links
dark market bitcoin dark web
the dark internet tor markets
dark web link deep web search
darknet markets darknet market list
dark web market list tor market url
deep web drug links darknet markets 2023
dark market dark web search engines
darknet websites deep web drug links
tor darknet deep web drug links
tor markets links bitcoin dark web
dark market onion deep web drug markets
darknet markets 2023 dark market list
darknet drug links dark web sites links
dark website tor darknet
how to access dark web tor markets
dark web websites dark market
tor markets links darkmarket list
darkmarket link black internet
darknet market list dark market onion
darknet drugs darknet drug store
darkmarket link best darknet markets
darknet market links darkmarket 2023
darkmarket url tor market url
darknet market lists darkweb marketplace
darknet drug links dark market onion
tor markets 2023 deep web markets
dark web websites tor markets 2023
dark web markets darknet marketplace
dark web market links the dark internet
darkweb marketplace dark web search engines
deep web links darknet market
drug markets dark web darknet search engine
darkmarket list black internet
bitcoin dark web tor market links
dark web links darknet drug store
darknet sites dark web market list
darknet sites darknet links
dark web link dark website
how to get on dark web dark web websites
deep web drug markets https://alldarkmarkets.shop/ dark market
best darknet markets dark markets
dark market url deep web drug links
dark web drug marketplace darknet websites
darknet market list drug markets dark web
darknet market dark web market links
dark web link tor darknet
darknet drug links deep dark web
dark market link dark web market links
dark web market links dark web market links
dark market url the dark internet
dark market link darknet websites
drug markets onion tor markets
darknet site dark web market links
darkmarket list darkmarket url
blackweb deep web drug markets
tor market darkmarket 2023
darknet drug links darknet markets 2023
tor darknet the dark internet
dark web sites links dark web drug marketplace
dark web sites dark internet
free dark web darkmarket url
darknet markets 2023 drug markets dark web
darknet drug market dark web markets
darknet markets darknet markets
drug markets onion dark markets
dark market darknet drug store
darknet marketplace darknet drug links
tor market url darkweb marketplace
tor markets links tor market links
tor marketplace dark web links
darknet markets 2023 darknet drug market
tor dark web deep web sites
dark web sites links darknet search engine
darkmarket free dark web
darknet market links bitcoin dark web
dark markets 2023 https://alldarkmarkets.shop/ darknet links
dark web market list tor darknet
dark web sites darknet drug store
dark web sites links tor markets
dark web links darknet seiten
deep web drug store darknet marketplace
darknet websites deep web markets
tor marketplace dark market list
deep web sites the dark internet
dark web search engine darknet market
darknet drug links deep web drug store
dark web access darkmarket
dark market dark websites
blackweb dark web sites
bitcoin dark web dark markets
deep dark web dark market onion
blackweb official website dark market 2023
black internet tor market links
drug markets dark web how to get on dark web
dark web market links darknet marketplace
darkmarket 2023 darknet seiten
bitcoin dark web tor markets 2023
tor marketplace deep web search
dark web access tor market
darkmarket 2023 dark markets
dark market 2023 tor markets
dark web links free dark web
darknet sites deep web sites
darknet drug store dark web market
best darknet markets dark markets
deep web drug url dark web search engine
dark web link tor markets 2023
dark web sites links tor marketplace
deep web sites dark markets
how to get on dark web https://alldarkmarkets.shop/ dark market
drug markets onion the dark internet
blackweb dark web link
darknet marketplace darknet drug store
deep web drug links dark market 2023
darknet market dark market link
dark net deep web sites
dark market url darknet market list
tor markets links deep web markets
dark web access dark website
dark web market links darknet search engine
dark web site dark web sites
darknet markets dark web sites links
deep dark web deep web drug store
dark web links dark web sites links
dark internet dark web sites links
bitcoin dark web darkmarket list
darknet marketplace bitcoin dark web
onion market darknet drug market
tor markets dark web market list
drug markets onion tor dark web
dark web market list dark markets 2023
dark web market list darkmarkets
darkmarket 2023 darkweb marketplace
drug markets dark web tor markets links
dark net dark markets
darkmarkets darknet search engine
dark web market best darknet markets
deep web links darknet drug links
blackweb best darknet markets
how to access dark web darknet sites
deep web drug url tor markets
dark web search engine dark markets 2023
dark market darknet market
deep web drug store dark web websites
dark websites darkmarket
deep web drug markets tor dark web
the dark internet darkmarket link
how to access dark web darknet seiten
darkmarket dark web drug marketplace
tor markets 2023 free dark web
deep web drug links tor markets links
deep web drug url deep web drug url
free dark web dark web market
dark market link blackweb
darknet drug market darknet markets 2023
how to get on dark web tor darknet
dark market list dark web websites
how to access dark web darkmarket
tor dark web deep web drug url
darknet marketplace the dark internet
deep web drug markets deep web drug url
tor market url dark websites
deep dark web best darknet markets
dark web market dark web links
darknet markets darknet drugs
dark market link https://alldarkmarkets.shop/ darknet market links
tor markets links tor market links
blackweb official website tor markets links
tor dark web darknet market links
dark internet darknet sites
dark web link tor market
dark net dark web search engines
darknet drugs deep web search
dark web sites dark market
dark market link darkmarkets
dark web market links tor markets
dark web markets dark website
tor markets links tor market
darkmarket list dark market list
dark web markets darknet market
darknet drug links dark market link
darkmarket dark web access
darknet drugs drug markets dark web
darkmarket darknet drug links
deep dark web dark website
darknet links deep web drug links
dark market link best darknet markets
dark net how to access dark web
darkmarket 2023 dark markets
darknet markets 2023 dark markets
dark web market links darknet search engine
dark web links dark web market links
dark market free dark web
dark web link the dark internet
darknet market list darknet market links
darkmarket 2023 darknet drug links
tor market url dark markets 2023
onion market darknet links
tor markets 2023 dark market 2023
dark web link https://alldarkmarkets.shop/ darknet links
darknet drug links darknet market links
deep web search darknet search engine
dark web link dark web markets
tor market dark market list
deep web markets darknet drug store
tor darknet onion market
deep web drug markets darknet markets
deep web sites dark web market links
dark website darknet market lists
darknet sites darkmarket link
black internet deep web drug url
dark web links dark internet
darknet websites tor market
darknet websites dark web market
dark net dark web websites
black internet dark web websites
dark market onion deep web sites
deep web sites tor markets links
darknet markets dark markets
dark websites tor dark web
the dark internet deep web sites
darknet market best darknet markets
deep web drug markets dark market url
darknet market list dark internet
deep web drug links darknet websites
darkmarkets best darknet markets
darkmarkets dark web market list
how to get on dark web tor markets 2023
darkweb marketplace bitcoin dark web
darknet markets 2023 https://onion-dark-markets.shop/ darknet site
onion market darkweb marketplace
darkmarket darknet drug store
darknet site darknet drugs
dark web drug marketplace free dark web
dark web markets darknet websites
dark web websites darkmarket link
dark web sites darknet drug links
tor market links deep web sites
blackweb darknet marketplace
tor dark web dark websites
darknet market list drug markets dark web
darkmarket tor markets
dark market url best darknet markets
blackweb official website dark web market links
dark website deep web drug links
dark web market links darknet drug market
deep dark web dark web search engines
deep web search tor markets links
darkmarket 2023 drug markets onion
deep web drug links darkmarket 2023
deep web markets dark market link
bitcoin dark web dark market onion
darkmarket list dark web search engine
tor markets darknet market links
darknet seiten dark internet
dark web search engines dark market onion
tor marketplace dark market url
dark web access dark web sites links
free dark web onion market
dark net dark web search engine
darkmarket link dark market onion
deep web sites darkmarket
darknet market https://onion-dark-markets.shop/ deep web links
darknet drug market dark website
dark websites deep web sites
darknet drug store dark website
darknet site dark website
tor dark web tor darknet
darknet websites dark net
darknet market list dark market
darknet markets dark markets
best darknet markets darknet drug store
dark market link dark web market
dark web search engine dark markets 2023
deep web links darkmarket link
best darknet markets tor market url
bitcoin dark web darknet seiten
bitcoin dark web darknet market
dark web site dark web link
darkweb marketplace darknet marketplace
deep web drug markets dark web websites
dark web access dark markets 2023
deep dark web deep web drug links
darknet links darknet market
darknet market links dark net
best darknet markets darknet websites
darknet sites drug markets dark web
tor market dark web sites
dark web links deep web markets
dark market list tor markets links
darkmarket link dark markets 2023
darknet search engine tor market
dark web sites https://alldarkmarkets.shop/ deep web drug links
tor market url tor markets 2023
dark web search engine drug markets dark web
free dark web deep web search
deep web search darknet sites
deep web markets darknet marketplace
dark markets dark web market
darknet market dark web markets
darkmarket link darknet market links
darknet drug links deep web drug markets
darknet search engine dark internet
dark web search engine darkmarket url
dark web sites deep web drug markets
deep web markets dark web market list
blackweb the dark internet
darknet drug store darknet drug links
dark market onion tor markets
darknet markets 2023 tor market
tor dark web darkmarket 2023
dark markets dark websites
darknet markets tor markets links
tor market links drug markets dark web
darknet drug market tor market links
deep web drug url dark internet
black internet black internet
darkmarket 2023 darknet drugs
deep web drug url best darknet markets
deep web drug store dark market list
dark market 2023 tor market links
dark website https://alldarkmarkets.shop/ darkmarket 2023
deep dark web darkmarket 2023
deep web links darkmarket url
deep web drug links blackweb
dark websites darknet drug links
tor darknet darkmarket url
blackweb official website blackweb
dark web site dark web site
dark net how to access dark web
darknet search engine tor markets links
darknet search engine tor dark web
deep web drug markets dark web markets
darknet market list dark internet
dark web access darkmarket list
free dark web the dark internet
darkmarket url darkmarket url
deep dark web dark web market
the dark internet deep web markets
dark market link tor markets 2023
dark market onion darknet market list
deep web markets dark market onion
tor darknet darknet search engine
darknet marketplace darkmarket
deep web drug links tor dark web
darknet markets 2023 deep web drug links
dark web market darknet markets
darknet market darknet drug links
tor markets deep web drug markets
dark web link tor market links
deep dark web deep web search
blackweb official website dark market list
dark web search engines darknet websites
drug markets dark web dark web drug marketplace
dark internet free dark web
darknet market lists dark web link
deep web drug store dark website
deep web drug store https://onion-dark-markets.shop/ darkmarket 2023
darkmarket link darkmarkets
darknet sites darkmarket list
darkmarket darkmarkets
darknet sites dark web search engines
dark internet deep web links
deep web drug markets dark web market
darknet drug store darknet markets
darknet market list darknet marketplace
dark web sites links tor market links
darknet markets 2023 darknet drugs
darknet markets dark net
deep web links darknet websites
darknet websites black internet
darknet markets drug markets onion
the dark internet dark market
darkmarket 2023 dark web sites
darknet markets 2023 drug markets onion
darkmarket link darknet drug market
dark website dark web link
darknet websites dark market link
dark market list tor markets links
darknet market lists tor markets 2023
dark market url free dark web
dark markets dark market url
darknet market lists darknet drugs
dark web markets dark web links
darknet market list tor darknet
darknet market links how to access dark web
deep web search deep web search
darkmarket link darknet drugs
dark web search engines darknet drugs
tor market darknet drug store
tor market links https://alldarkmarkets.shop/ dark website
blackweb darkmarket url
tor markets links dark websites
dark websites darknet links
tor markets 2023 dark web market
deep web drug url blackweb
dark web websites dark web market list
deep web sites darknet markets 2023
dark web links darknet markets
darknet drugs dark web market links
dark website darkmarket list
deep web sites darknet site
darknet market list darknet drugs
dark web markets deep web markets
tor market links deep dark web
deep web drug store tor market url
dark web sites darkweb marketplace
darkmarket link darknet drug links
best darknet markets darknet websites
dark internet dark web sites links
the dark internet dark web links
dark web market links dark web site
tor markets 2023 tor darknet
deep web drug links deep web drug markets
deep web links darkmarket 2023
darknet market lists deep web links
dark market onion deep web drug links
dark market url dark web drug marketplace
tor market dark internet
dark website darknet sites
dark internet dark web market list
deep web drug store dark market list
darkmarket list tor market links
dark website darknet drug store
dark websites darkmarkets
best darknet markets darknet seiten
darknet drugs darknet drug market
dark market deep web drug store
darknet drug links tor dark web
dark web market list best darknet markets
dark market 2023 darkweb marketplace
darknet drugs darknet drug links
darknet search engine deep web sites
dark market list deep web sites
darknet site tor market links
dark market url darknet drug store
deep web markets darknet marketplace
how to access dark web tor market url
black internet dark web websites
tor market url onion market
tor markets dark internet
dark web websites tor market url
darkmarket 2023 tor dark web
dark web sites tor market
darknet drug links dark web markets
darkmarket 2023 onion market
dark web market links https://onion-dark-markets.shop/ deep web markets
dark web search engines darknet markets 2023
dark website dark web access
tor markets links deep web search
darknet drug market https://alldarkmarkets.shop/ dark markets 2023
blackweb official website dark web access
darknet sites darknet links
tor markets 2023 onion market
dark web markets https://alldarkmarkets.shop/ darknet sites
dark web links tor market url
dark web drug marketplace darknet markets
darknet market list darkmarkets
dark web site https://onion-dark-markets.shop/ darknet drug market
dark web market dark web site
dark web market darknet seiten
tor market links dark web sites links
dark market onion black internet
dark web site https://onion-dark-markets.shop/ darknet search engine
blackweb official website darknet drugs
deep web drug links drug markets onion
dark website darknet sites
dark web market links bitcoin dark web
onion market dark website
darkweb marketplace dark websites
blackweb darknet markets 2023
dark web drug marketplace dark web drug marketplace
darknet markets 2023 how to get on dark web
dark web search engines darknet links
darknet drugs the dark internet
dark market url darkmarket
tor market url darknet drugs
darkweb marketplace tor market
dark market link dark web link
darknet links darkmarket list
darkmarket link dark websites
dark web drug marketplace https://onion-dark-markets.shop/ deep web drug links
dark web links darknet markets
dark market link darknet drug market
drug markets dark web dark web drug marketplace
deep web drug url bitcoin dark web
darknet markets 2023 dark market link
drug markets dark web dark web market list
tor markets links dark markets
black internet deep web drug store
deep web drug links darknet websites
dark internet tor dark web
dark web market links deep web drug markets
darkmarket link darknet search engine
deep web links how to access dark web
deep web drug store deep web drug store
deep web drug url darknet drug store
dark web markets darknet site
darknet market blackweb
free dark web tor markets 2023
dark markets 2023 deep web links
deep web search the dark internet
dark web market links dark web market links
darknet market list tor market links
drug markets dark web dark web search engines
dark market list dark web search engines
deep web drug store dark web market links
dark website drug markets dark web
tor market links dark internet
dark market url dark web market
dark web links deep web drug markets
drug markets onion dark net
dark web links black internet
darknet drug links dark market list
darkmarkets dark net
bitcoin dark web darknet links
dark web access dark web site
deep web search bitcoin dark web
dark market dark web markets
darknet drug store darkweb marketplace
black internet darknet drugs
darknet markets 2023 dark market onion
tor market links darknet site
darkmarket 2023 dark web markets
dark market dark net
dark markets 2023 dark markets
dark market 2023 dark web market links
the dark internet darknet market
darkmarket url darknet drugs
how to get on dark web darkmarket list
dark web market links darknet drugs
dark web markets dark web market
onion market darknet drug store
dark market onion darknet market lists
dark web websites darknet drug market
dark web sites links tor market
dark market dark net
dark web websites dark market onion
tor market how to get on dark web
how to get on dark web darknet site
tor market links dark web site
onion market best darknet markets
dark market list dark web market links
tor markets 2023 deep web drug links
darknet market links deep web drug url
dark market link darknet markets 2023
darkweb marketplace dark market onion
blackweb darknet sites
darkmarket darknet markets
deep web drug links deep web drug links
black internet dark market link
onion market deep web drug url
deep web drug store deep web drug markets
deep web drug links dark web markets
black internet darkweb marketplace
tor markets 2023 darknet markets 2023
deep web drug markets the dark internet
blackweb darkmarket
dark web market links deep web drug markets
tor dark web deep web sites
darknet drug store darkmarket url
tor darknet deep dark web
tor markets links darkmarket link
free dark web tor darknet
dark web link tor markets
drug markets onion dark web search engines
dark web websites dark market link
darkmarket dark web markets
tor market links darkmarket
tor marketplace tor dark web
dark web link darknet websites
dark web link darknet sites
dark market onion deep web links
dark web market links https://onion-dark-markets.shop/ darknet site
deep web drug url best darknet markets
bitcoin dark web dark market list
darknet drug links dark web market
blackweb dark websites
darknet market list deep web markets
dark market 2023 deep web links
dark market link how to access dark web
dark web websites free dark web
deep dark web dark web market links
darknet markets 2023 darkmarket url
dark market 2023 darknet market
darkweb marketplace dark market url
how to access dark web dark markets
deep dark web dark web market
darknet seiten dark market link
deep dark web dark markets
darknet search engine black internet
tor markets links darknet market list
dark market darknet drugs
darkweb marketplace darknet marketplace
dark web market list darknet seiten
darknet market links onion market
best darknet markets tor marketplace
darkmarket link darknet market
darknet drug market dark markets
darknet search engine dark web search engines
dark market dark net
dark market link darknet site
dark web sites dark web drug marketplace
dark web search engines https://onion-dark-markets.shop/ darknet marketplace
deep web drug markets tor market url
tor markets links tor marketplace
drug markets onion how to get on dark web
tor market links deep web sites
deep web drug url dark web site
darkmarket 2023 deep web drug store
dark web market links dark markets
dark net drug markets onion
best darknet markets free dark web
tor markets 2023 dark markets
bitcoin dark web tor markets
tor market url deep dark web
dark web links darknet markets 2023
deep dark web deep dark web
darknet markets 2023 dark website
onion market dark web drug marketplace
deep web drug links tor markets links
dark market link tor market url
deep web markets onion market
deep web drug store darknet marketplace
tor markets dark market list
dark web access tor marketplace
black internet dark web sites
dark market onion how to access dark web
the dark internet darkweb marketplace
darknet marketplace how to access dark web
deep web drug markets tor darknet
deep web links dark market list
dark web link dark web sites
drug markets dark web https://alldarkmarkets.shop/ blackweb official website
darknet links best darknet markets
dark web market list deep web links
dark web search engine darknet market
darknet marketplace tor markets
free dark web dark web websites
dark web search engine darknet market lists
dark internet dark web market
deep dark web darkmarket list
tor marketplace how to get on dark web
darknet search engine deep dark web
dark web sites links dark market onion
dark web markets darknet drugs
dark market link darknet site
darkmarket url darknet search engine
best darknet markets darkmarkets
how to access dark web dark web link
dark web market list darknet markets
dark web market deep web drug url
the dark internet darknet markets
onion market darkmarket link
dark markets 2023 darknet drug market
deep web links tor market url
drug markets onion darknet site
how to get on dark web darkmarkets
tor market darkmarket url
how to access dark web dark web sites
tor market darknet market lists
dark web sites darknet drug market
darkmarket list black internet
dark markets 2023 darknet marketplace
black internet dark web links
dark market 2023 https://alldarkmarkets.shop/ darknet markets 2023
darknet market lists deep web drug store
darknet marketplace blackweb official website
deep web links dark web market list
darkweb marketplace deep dark web
deep web sites drug markets onion
darknet marketplace tor market url
tor markets links deep web links
dark web search engine deep web drug store
how to access dark web darknet sites
free dark web dark net
dark web sites links dark net
darknet drugs free dark web
best darknet markets dark markets
black internet deep web markets
darkmarket list darkmarket 2023
dark market 2023 dark web drug marketplace
darknet drug links darknet market lists
darknet site tor marketplace
darkmarket dark net
dark market link dark net
darknet seiten darkmarket list
darknet sites deep web drug url
dark web search engines dark web access
dark web links deep web links
deep web drug url best darknet markets
darknet drug market https://alldarkmarkets.shop/ blackweb official website
dark web link tor market url
dark market dark markets 2023
darknet drug store tor darknet
deep web drug markets deep web links
tor markets 2023 tor darknet
darkmarket link deep web drug store
darknet marketplace darkmarket 2023
dark websites dark web sites links
dark web drug marketplace tor dark web
free dark web dark web market
darknet drug store deep web markets
dark market darknet drug store
darkmarkets darknet site
darkmarket tor market url
darknet sites deep web drug url
onion market darkmarkets
tor market links dark web link
dark web markets blackweb official website
darknet drug store how to get on dark web
darknet markets 2023 tor darknet
dark net dark web access
deep web search dark web search engines
best darknet markets darknet websites
dark market 2023 dark internet
darknet market lists dark net
dark web drug marketplace darknet market lists
darknet market list dark web websites
tor market darknet market lists
darknet market lists how to get on dark web
dark market link https://alldarkmarkets.shop/ darknet drug market
deep web markets tor market url
darknet drugs dark net
darknet seiten tor darknet
tor darknet darknet markets
darknet markets drug markets onion
darkweb marketplace darkmarket 2023
darknet market links dark web drug marketplace
dark web access dark web sites links
the dark internet dark market url
deep web links dark web links
dark websites dark market 2023
tor markets tor dark web
tor market url dark markets 2023
dark market dark net
dark web search engine dark web link
darkmarkets dark web market
dark market 2023 tor markets
drug markets dark web deep dark web
the dark internet darknet links
deep web markets dark web search engines
deep web search darknet drug store
dark internet black internet
deep dark web dark web market list
tor market links dark web link
dark web market dark web link
free dark web tor markets 2023
dark web search engine dark web access
blackweb darkmarket
darknet websites darkmarket link
dark web link dark internet
dark web sites links darkmarket
how to access dark web dark web access
tor market dark web link
darknet drug market darknet markets
darknet market links darknet market
dark web drug marketplace darknet market lists
deep web drug markets dark web site
tor dark web how to get on dark web
darkmarket 2023 dark web search engine
how to access dark web dark market url
tor markets links darkmarket list
darkmarket link darkmarket
free dark web dark web links
tor darknet dark web market list
darknet site dark markets 2023
darkmarket url deep web links
drug markets dark web tor markets links
dark web sites links darknet seiten
dark market link deep web search
darknet marketplace tor market
deep web links how to access dark web
tor market tor darknet
darkweb marketplace darknet search engine
darknet markets 2023 bitcoin dark web
darkmarket list tor darknet
dark internet dark web markets
deep dark web deep web drug url
darknet marketplace dark web search engine
dark web search engines drug markets onion
deep web drug store darknet marketplace
darknet market list dark market onion
deep web search blackweb official website
darkmarkets drug markets dark web
drug markets dark web https://alldarkmarkets.shop/ darknet drug links
darknet market lists how to access dark web
dark web sites links darkmarket
darknet markets 2023 deep web search
dark internet tor market
dark web market links dark website
darknet seiten darkmarket 2023
darkmarket link deep web drug links
dark web market darknet drugs
bitcoin dark web free dark web
blackweb official website dark web market
dark market dark websites
tor market dark web access
dark market list darknet drug store
darknet search engine dark internet
dark markets 2023 dark web search engine
darknet drug links dark web search engine
dark market onion deep web drug links
darknet markets drug markets onion
darknet site dark web market links
dark web site darknet site
darkmarket 2023 dark web market list
darkweb marketplace dark market list
dark web markets dark website
deep web drug markets darknet market
darknet links darkmarket
tor markets links dark web links
tor market links tor markets
tor markets 2023 deep dark web
dark web markets dark markets 2023
darknet markets darknet market lists
deep web sites deep web drug store
darknet markets dark market
dark websites darknet market list
deep web search darkweb marketplace
dark web search engines darknet site
darknet marketplace tor darknet
best darknet markets dark market onion
deep web links deep web sites
dark web sites how to get on dark web
tor markets dark web search engines
darknet links black internet
deep web drug url blackweb official website
darknet markets the dark internet
dark web drug marketplace dark web market links
drug markets onion drug markets dark web
dark web link tor markets 2023
darknet site tor market
darknet site darknet marketplace
darknet markets 2023 darknet markets 2023
darkmarkets darknet market list
darknet search engine deep web drug store
deep web drug store dark markets
dark net darkmarket url
dark web websites the dark internet
darknet market lists how to get on dark web
dark web markets dark market link
darkweb marketplace darknet search engine
darkmarket link tor darknet
darkmarket link darknet market
tor markets darknet seiten
darknet market links dark markets 2023
deep web drug links bitcoin dark web
dark websites drug markets dark web
darknet search engine dark web market
deep web drug store deep web drug markets
darknet market links the dark internet
tor market links dark markets
tor markets https://onion-dark-markets.shop/ darknet seiten
darknet drug links dark markets
deep web links deep web links
tor markets 2023 darkmarket list
darknet marketplace dark web links
dark market url dark web drug marketplace
black internet dark web websites
dark internet dark market 2023
darknet drug links darkmarket link
tor markets the dark internet
tor market blackweb official website
dark web markets dark internet
dark market url deep dark web
tor markets dark web access
darknet seiten darknet market list
deep web markets darknet drug store
darkmarket dark market 2023
dark web sites links darkweb marketplace
dark website dark net
how to access dark web tor marketplace
tor market url dark markets
deep web drug markets dark websites
darknet sites dark market link
darknet seiten tor dark web
dark web sites links deep web search
free dark web darkmarket 2023
dark markets 2023 dark web search engine
drug markets dark web darkweb marketplace
darknet markets 2023 dark web drug marketplace
dark web site best darknet markets
deep web sites tor dark web
bitcoin dark web dark web market links
tor market url https://alldarkmarkets.shop/ tor darknet
dark web link tor market url
dark markets tor markets
deep web drug markets darknet links
dark web access tor marketplace
darkmarket darkmarket link
darkmarket list tor market links
dark web market links dark web sites links
dark web sites deep web drug store
deep dark web onion market
tor marketplace darknet market list
darknet websites dark web search engines
deep web markets darknet drugs
darknet market lists tor market links
drug markets onion dark market 2023
darknet market dark web websites
darknet market free dark web
tor market url dark market link
dark web drug marketplace darkmarket list
darknet market deep web sites
darknet marketplace dark markets
darkmarkets dark market url
darknet market list tor markets 2023
darknet drugs how to get on dark web
darkmarket onion market
the dark internet darknet site
darknet websites dark market url
onion market blackweb
deep web drug links https://alldarkmarkets.shop/ darknet site
tor dark web dark market link
dark web market darknet seiten
darknet site tor market url
darknet seiten darknet markets 2023
darkmarket url darknet market links
darkweb marketplace darkmarket list
drug markets dark web onion market
tor dark web darknet market
darknet markets 2023 blackweb
dark website tor market links
tor market links darkmarket 2023
the dark internet dark market
deep web sites free dark web
dark web sites how to get on dark web
dark market onion darknet markets 2023
dark internet dark web market links
darkmarket deep web sites
dark web drug marketplace darkmarket
dark market list darkmarket url
dark internet best darknet markets
dark web drug marketplace deep dark web
drug markets dark web tor market url
dark website darknet websites
dark web sites links tor dark web
darknet markets darkmarket link
dark markets 2023 deep web drug url
darkweb marketplace black internet
tor dark web darknet site
dark web market darknet marketplace
drug markets onion https://onion-dark-markets.shop/ tor market links
dark web access dark web sites links
how to get on dark web deep web drug markets
deep web markets tor marketplace
dark web search engine dark markets
darknet drug links darknet sites
deep dark web best darknet markets
tor dark web dark web site
dark web links darkmarkets
dark web market list the dark internet
darkmarkets darknet seiten
darknet marketplace darknet websites
dark net blackweb official website
deep web drug markets darknet links
darknet market list darknet search engine
deep web search darknet seiten
dark internet darkmarket
dark web links tor markets links
dark market url onion market
deep web search dark web drug marketplace
deep web markets dark web link
drug markets onion dark web access
darknet search engine dark web markets
dark web drug marketplace drug markets dark web
dark markets 2023 drug markets dark web
drug markets onion how to get on dark web
darknet market darknet marketplace
dark web sites links https://onion-dark-markets.shop/ dark markets
dark web link tor market links
dark web sites dark market list
drug markets onion the dark internet
blackweb dark web search engines
dark website bitcoin dark web
deep web links darknet market
darknet marketplace darkmarket url
darkmarket list bitcoin dark web
dark web site dark web search engine
tor dark web black internet
darknet drug links dark market url
darknet market lists darknet markets
tor market deep web drug url
dark market 2023 darkweb marketplace
dark internet darkweb marketplace
dark markets darknet markets 2023
dark web market links tor markets links
bitcoin dark web free dark web
darkweb marketplace tor marketplace
tor markets links dark markets
tor darknet tor markets links
darknet seiten dark web markets
dark website dark web access
darknet drug market free dark web
darknet site darknet websites
dark web drug marketplace deep web sites
dark web market darknet markets
dark market 2023 free dark web
dark markets darknet markets
blackweb official website onion market
how to get on dark web darkmarket 2023
deep web drug markets dark market url
dark market list how to access dark web
darknet drug market dark internet
dark net dark web search engine
dark markets darknet market list
darknet drug links deep dark web
darkmarket url darknet marketplace
dark website black internet
darkmarket url deep web links
blackweb darkmarket url
dark web market links drug markets onion
tor darknet deep web drug url
dark market list tor markets
darkmarket list black internet
darknet market links dark web site
darknet market lists darknet market links
tor market url darknet market list
dark websites darknet markets
darknet drug store tor market
darkweb marketplace darkmarket url
dark market onion tor darknet
darknet drugs dark web markets
darknet markets 2023 darknet market
tor market links how to access dark web
dark web drug marketplace deep web drug store
dark market list tor dark web
tor market darknet market lists
dark web sites links darknet search engine
darkweb marketplace tor markets
darkmarket 2023 dark market list
tor markets 2023 dark market url
tor dark web deep web markets
dark websites dark web search engines
darknet markets dark web sites
blackweb official website deep web drug url
drug markets onion dark market url
dark web markets https://alldarkmarkets.shop/ darknet market links
dark net deep web drug links
dark web sites links free dark web
darknet links dark market
darknet websites darknet links
tor marketplace tor market url
dark markets dark websites
how to get on dark web darknet market links
dark websites how to access dark web
bitcoin dark web dark market
dark market link dark website
dark market link darknet seiten
darkmarket list dark market onion
tor markets links deep web sites
how to get on dark web tor markets
dark web markets deep web drug url
darknet drug links darknet drug links
darknet seiten deep web drug store
dark websites dark internet
dark web site darknet drug store
dark web websites dark web markets
dark web market links tor darknet
dark web link deep web search
dark web links tor markets links
tor dark web darkmarket link
dark web sites how to get on dark web
dark markets tor marketplace
dark web markets the dark internet
dark web markets dark web site
darknet drug links darknet markets 2023
darknet links tor market url
dark websites blackweb official website
darkmarket 2023 deep web search
darknet links deep web markets
dark market onion darkweb marketplace
darknet drug market dark web sites
blackweb official website blackweb official website
blackweb official website deep dark web
tor markets links dark website
darknet websites dark web links
dark web market links darkmarket 2023
dark markets dark internet
bitcoin dark web darknet markets
darknet search engine dark web search engines
dark markets 2023 blackweb
darkmarket 2023 darknet sites
tor market dark market list
darknet market list tor markets 2023
darknet seiten deep web drug markets
dark web links dark web links
dark internet darkweb marketplace
darknet markets dark website
best darknet markets bitcoin dark web
dark net deep web drug links
tor market links blackweb official website
deep dark web darknet links
bitcoin dark web darkmarket list
dark web sites dark market link
drug markets dark web darknet seiten
tor market darknet drug market
dark web websites dark web site
the dark internet tor markets
darkmarket list dark net
darknet links darknet market links
tor market links dark market
deep web drug url deep web links
darknet links https://alldarkmarkets.shop/ dark web search engine
darknet markets 2023 darknet drug store
the dark internet darknet links
drug markets dark web tor marketplace
darkmarket dark website
drug markets dark web deep web search
best darknet markets dark website
darkmarket url blackweb
darknet seiten dark websites
tor market links tor market url
dark markets darknet market list
tor markets links deep dark web
free dark web darknet sites
dark web market list dark web market list
dark web market list darkmarket list
dark web site blackweb
how to get on dark web deep web drug store
darknet market lists tor market url
drug markets onion dark web site
dark market url dark web site
dark markets 2023 deep web drug links
darknet market darknet market lists
deep web drug markets darknet drug market
deep web search onion market
tor market url darknet drugs
blackweb dark web site
darknet marketplace dark web site
dark web search engines blackweb official website
darkmarket tor markets 2023
deep web drug store darkmarket url
tor markets the dark internet
dark market tor dark web
dark market onion darknet sites
deep web drug store dark web drug marketplace
dark markets 2023 darkmarket list
tor markets 2023 darknet marketplace
dark web search engines black internet
darkmarket 2023 deep web markets
onion market dark market url
darknet seiten tor market
dark markets dark market list
tor marketplace darknet drug market
darknet drug links dark web link
darknet seiten dark markets
dark website dark market 2023
dark web links darknet markets
darknet links tor markets links
tor market url dark web market
deep web drug markets dark net
deep web drug url deep web drug markets
dark web search engines drug markets dark web
dark web sites links dark market
darkmarket dark web market list
best darknet markets dark website
deep web links free dark web
darkmarket list drug markets onion
dark web markets deep web drug url
dark net darknet drug links
black internet darkmarket
darknet seiten dark web drug marketplace
deep web sites blackweb
darknet market links dark web markets
blackweb official website deep web sites
tor market url darknet drug links
dark web sites deep dark web
dark market 2023 dark web links
tor market url darknet seiten
dark web links dark internet
dark market url deep web drug url
darkmarket link drug markets dark web
dark market 2023 the dark internet
bitcoin dark web how to get on dark web
darknet search engine dark market link
dark web search engine tor market url
best darknet markets tor market url
dark internet darknet drug store
darknet websites dark web sites
darknet drug store darknet drug market
darknet drug store darknet marketplace
blackweb official website dark web drug marketplace
tor markets dark web market links
dark market onion darknet marketplace
tor market darkweb marketplace
darknet marketplace darknet drugs
dark web market darkweb marketplace
darkmarket 2023 darknet market lists
dark market 2023 dark web links
tor markets links dark web links
dark market url deep web drug store
dark web market list dark web sites
dark web sites darknet markets 2023
dark web search engine darknet links
dark web market links darkmarket 2023
dark web sites links drug markets onion
dark market url best darknet markets
how to access dark web darknet markets 2023
darkmarket deep web drug links
dark web site darknet websites
how to get on dark web dark website
darkweb marketplace deep dark web
tor markets links darkmarkets
how to access dark web dark web links
darkmarket tor dark web
darknet drug store tor marketplace
the dark internet darknet market links
darknet markets dark market onion
dark market url drug markets onion
darkmarket dark market url
tor market url darknet seiten
darknet marketplace dark web drug marketplace
dark web market list darknet market
darknet market links deep web drug store
dark market link the dark internet
darkmarkets darknet market links
darknet sites darkmarket list
darknet marketplace darkmarket 2023
blackweb official website free dark web
darknet drugs dark web site
dark market onion deep web markets
deep web drug url best darknet markets
tor dark web deep web links
deep web drug url darkmarket
darknet markets 2023 tor darknet
best darknet markets darknet market lists
dark web market list dark market url
dark market darknet links
dark web market links darkmarket list
dark web market list darknet markets
dark web search engine darkmarket link
tor market url darknet seiten
dark web sites drug markets onion
tor market links dark market list
dark web access dark web search engines
darknet websites tor dark web
dark web websites dark web sites links
drug markets dark web dark websites
dark markets 2023 darknet market
darkmarket dark web market list
darknet links dark website
deep web search dark web market links
dark market tor marketplace
darkmarket blackweb official website
darknet markets 2023 darkmarket 2023
dark market link dark website
dark market darknet markets 2023
dark market list deep web drug url
darknet market lists darknet site
dark websites darknet drugs
darknet markets 2023 deep dark web
deep dark web dark market 2023
darknet drug store darkmarket link
darkmarket url deep web search
dark web search engine dark markets 2023
dark web link dark web market links
dark web sites links free dark web
dark market dark net
dark market onion onion market
darknet markets 2023 dark market url
deep web search bitcoin dark web
how to get on dark web tor market
darknet drug links the dark internet
tor market url how to access dark web
tor market url darknet links
darknet websites bitcoin dark web
darknet drug store dark websites
darknet markets deep web drug store
deep web sites darknet websites
dark web sites how to access dark web
darknet drug links darkmarket url
darknet drug links darknet site
dark web links darknet drug market
dark web market links dark market onion
darkmarket link darkmarket
darknet markets 2023 tor dark web
darkmarket list dark web links
tor markets dark markets 2023
dark web markets bitcoin dark web
dark web site tor dark web
tor marketplace tor market url
darknet links dark web markets
dark market onion tor darknet
dark web sites links drug markets dark web
black internet darknet websites
the dark internet tor dark web
darknet websites dark web links
darknet market links deep web drug url
dark internet dark web site
deep web drug links deep web markets
tor dark web dark web websites
deep web drug links deep web sites
dark market 2023 dark internet
darkweb marketplace how to access dark web
tor markets 2023 darknet websites
dark market onion dark web market list
dark websites dark web search engine
darknet drug market deep web drug links
dark internet dark internet
darknet seiten dark web site
dark web sites links bitcoin dark web
dark website darkmarket url
darknet sites dark web market links
darknet market links darknet drugs
dark market onion darknet drug market
deep web drug url dark market 2023
dark web market links dark markets 2023
dark web drug marketplace dark web links
dark market list darknet markets
dark market onion dark web search engines
blackweb darknet market
dark net dark market 2023
darknet market links darkmarkets
darknet sites dark web websites
darkweb marketplace drug markets onion
darknet drug store darknet drug market
dark web market list darknet market links
deep web drug url dark websites
tor market how to get on dark web
tor darknet darkweb marketplace
tor markets drug markets dark web
darkmarket list dark web site
darknet drugs the dark internet
dark market darkmarket list
darknet market list dark web links
dark market url tor darknet
dark web sites dark market list
blackweb how to access dark web
darknet seiten darknet market
deep web drug links how to access dark web
darkmarket list dark web access
dark web links darknet market list
deep web drug links darknet drug store
drug markets dark web dark web markets
dark web search engine darknet markets
tor markets dark web link
dark web sites links drug markets dark web
tor markets 2023 dark web access
dark market 2023 dark markets 2023
dark website deep web drug store
deep web links dark market url
tor markets 2023 how to access dark web
tor marketplace deep web search
dark markets dark market
dark web market darknet markets
darkmarket 2023 darkmarkets
darknet websites deep web drug store
dark market list blackweb official website
darkmarket list darknet drug store
dark web market tor market links
tor market links darknet websites
dark web market links deep web drug url
darknet market links darknet marketplace
dark web search engines dark website
deep web drug markets tor markets links
dark web markets dark web sites
blackweb official website darknet seiten
dark market link dark web search engine
darknet market lists darknet sites
darknet websites dark web search engines
dark web sites darkmarket
dark web sites links darknet site
dark market list dark websites
dark web drug marketplace how to get on dark web
dark market list dark market list
bitcoin dark web bitcoin dark web
tor markets darknet markets
darknet markets dark web link
onion market how to get on dark web
darkmarket 2023 deep web drug links
darknet market darkmarket 2023
dark web markets darknet markets
dark market list deep web markets
darknet market tor market
how to get on dark web darkmarket url
dark web site darknet market
tor markets 2023 tor market url
deep web drug store darkmarket url
deep web drug links darknet marketplace
darknet site darknet market list
deep web drug store darknet market list
dark web markets blackweb
dark market 2023 darknet drugs
blackweb dark markets
dark markets blackweb
dark market list tor market url
bitcoin dark web the dark internet
dark web market links deep dark web
free dark web darkmarket
dark internet dark web market links
darkweb marketplace deep web drug markets
dark web site deep web drug store
darknet markets 2023 tor marketplace
deep web search tor market url
darknet drug market deep web drug url
deep web markets dark websites
darkmarkets dark internet
how to access dark web deep web drug markets
tor dark web dark web market links
dark market onion dark web markets
dark web access onion market
deep web sites dark web market
dark web access dark web market
darknet marketplace dark markets
deep web sites drug markets dark web
darknet marketplace darkweb marketplace
darknet market links tor markets
darknet drug links deep dark web
dark web market links free dark web
darknet drug links tor marketplace
tor market dark web market links
dark web websites dark web link
dark web link dark web market links
drug markets onion tor darknet
tor markets 2023 dark web websites
darknet drug market darknet drugs
darknet markets dark web site
dark web search engine dark market 2023
dark web links free dark web
tor markets onion market
onion market dark web site
darknet market lists black internet
blackweb dark markets 2023
tor marketplace tor market
darkmarkets darkmarkets
dark websites darknet drug market
dark market 2023 darknet marketplace
darknet sites darknet markets 2023
dark market url darkmarket link
darknet site darknet market lists
darknet market lists dark web site
drug markets onion deep web search
how to access dark web tor market
blackweb tor market links
darknet markets dark markets 2023
deep web drug links darknet market
dark web links tor marketplace
dark markets deep web links
darknet marketplace darknet market list
dark market 2023 how to access dark web
dark web sites links dark web market list
dark web search engines darkmarket url
the dark internet blackweb
darkmarket 2023 the dark internet
deep web drug url dark web websites
dark web search engine blackweb
darknet drug market darknet site
dark website deep web drug links
dark websites deep web links
blackweb official website deep web sites
best darknet markets dark web search engines
blackweb darknet drugs
darkmarket list how to access dark web
how to get on dark web dark markets 2023
darkweb marketplace darknet marketplace
deep web links dark web market
deep web sites dark web links
darkmarket 2023 dark market link
deep web drug url darknet site
tor market url blackweb official website
darknet drug market onion market
dark market dark web market list
darknet drug store dark net
blackweb official website blackweb
darknet drug store tor dark web
tor marketplace dark markets 2023
dark web market links darkmarket
bitcoin dark web onion market
best darknet markets darknet drug links
tor marketplace dark market url
dark market onion dark web market list
tor markets links darknet site
darkmarket link onion market
dark website deep web drug markets
darknet drug links free dark web
darkmarkets darkmarket
darknet marketplace best darknet markets
darknet market list dark web search engines
deep web markets darknet drug links
deep web links deep web markets
dark website darknet websites
darkmarket 2023 dark web links
darkmarket list dark market url
dark web markets dark web search engine
dark web drug marketplace dark web sites links
deep web sites darkmarket 2023
darkmarket dark market list
dark markets 2023 darknet markets
darkmarkets drug markets onion
darknet sites deep dark web
the dark internet dark web sites
bitcoin dark web darknet marketplace
the dark internet deep web search
dark market dark markets
how to get on dark web dark web site
bitcoin dark web darknet search engine
how to access dark web dark web markets
deep web links tor markets links
how to get on dark web tor markets 2023
darknet marketplace darkmarkets
dark market dark web links
the dark internet darkmarket url
darknet drug market dark market onion
drug markets dark web darknet drug market
dark web markets tor market
darkmarket link dark net
tor markets links dark web markets
darknet market links darknet drug market
drug markets onion darknet drugs
dark market link darkmarket 2023
free dark web deep web drug markets
dark market 2023 dark market 2023
dark market onion tor markets
darkmarket link darknet markets
darknet markets 2023 dark web websites
darkmarket 2023 dark web sites
dark web access dark web drug marketplace
darknet markets 2023 onion market
darkweb marketplace deep web drug url
tor marketplace deep web sites
dark web drug marketplace darkmarket 2023
dark web markets tor market url
dark web market list dark internet
black internet deep web drug markets
deep web drug links dark web drug marketplace
darknet site tor darknet
You definitely made the point.
write my paper for me free essay writers online write my essay for free write my resume for me
This is nicely said. !
writing essays online essays writing service essay review service easy essay writing
Whoa many of wonderful tips.
dissertation writing help dissertations online dissertation assistance what is a phd
dissertation uk phd dissertation help phd dissertation writing dissertation writing help
computer science dissertations https://essaywritinghelperonline.com
Thanks a lot, Quite a lot of data!
essay on service customer service essay writing a persuasive essay college essay writing tips
You expressed it very well.
online coursework homework help hire someone to do my homework do my homework for free
Regards! Great information.
how to write a college essay best essay writing service best essay writing service paper writing help
real cialis no generic In certain embodiments, R Z5a is iso propyl
Terrific stuff. Regards.
buy essay essays for sale pay someone to write my college essay buy college essays
Thanks a lot! I enjoy it.
essay writing tips writing a scholarship essay professional cv writing service best resume writing service 2020
research paper writer services buy research paper research paper writer proposal writer
how can i write essay https://helpwithdissertationwriting.com
Awesome content, Cheers!
thesis titles thesis statements thesis topic thesis creator
Very good postings. Cheers.
buy an essay essay for sale pay to write essay pay for research paper
Valuable information. Thanks!
thesis writer a thesis writing a thesis statement research thesis
write my essays online writing essays for money write my essay for me essay writer no plagiarism
ghostwriters for hire https://buyanessayscheaponline.com
Valuable facts. With thanks.
a thesis doctoral thesis argumentative thesis a thesis
Regards, I appreciate it!
coursework writing service writing a scholarship essay legit essay writing service best essays writing service
pay someone to write a paper buy a paper paper writing service reviews order custom paper
social science dissertation https://writingthesistops.com
Thank you! Wonderful stuff.
thesis help thesis statements writing a thesis statement a thesis statement
help with writing an essay essay helper online college application essay help assignment help
master thesis writer https://dissertationwritingtops.com
Thanks! A good amount of postings!
do my essay write my paper for me do my essay for me write my resume for me
You actually said this well!
research thesis thesis sentence argumentative thesis thesis template
Incredible lots of helpful facts.
essay writing service buy best online essay writing service custom essay service
Nicely put, Many thanks!
dissertation abstracts dissertation abstracts international best dissertation best dissertation
Lovely forum posts. Kudos.
essay writing service hong kong quality essay writing services online dating profile writing service uk
Seriously a good deal of awesome advice.
dissertation help dissertation help dissertations dissertation data analysis help
paper writing services for college students buy essay online writing service essay paper writing service admission essay writing service
how to write a good scholarship essay https://writinganessaycollegeservice.com
Great write ups. Thanks.
writing service writing essay service essay writing sites easy essay writing
Nicely put. Regards!
buy college paper paper writing service reviews graduate paper writing service custom research paper writing services
Many thanks! Excellent information!
the college essay guy paperhelp essay helper writing help
Kudos, I enjoy this.
thesis statement meaning thesis creator thesis creator thesis statement
Nicely put. Thanks a lot!
military service writing college admissions essay writing service best essay writing website
Wonderful forum posts. Regards.
fast hour essay writing service legit essay writing services term paper writing service
Cheers, Awesome information!
report writing service best online will writing service linkedin profile writing service uk
You actually stated that terrifically.
content writing service in bangladesh best law essay writing service uk best cover letter writing service
Thanks. I appreciate it.
best essay writing website content writing service in bangladesh cv writing service london
Nicely put. Kudos.
affordable essay writing service joint service writing manual pdf essay writing services reviews blog
Thanks! Plenty of content.
best statement of purpose writing service writing essay meme essay writing software
Thanks, A lot of material.
essay writting service best academic essay writing service writing a persuasive essay
Nicely put. Appreciate it!
customer service business email writing which resume writing service is best essay service review
Thanks a lot, Excellent stuff!
essay writing service 3 hours non profit resume writing service best essay writing service yahoo
Appreciate it, A lot of advice.
best online essay writing service writing a reflective essay writing a 5 paragraph essay
Many thanks. Wonderful information!
nursing essay writing what is essay writing fake essay writing service
You actually revealed it well.
law essay writing service australia custom paper writing service essay writing sites
You actually mentioned that really well.
custom essay writing service business essay writing service essay writing service usa
Excellent posts. Regards!
example thesis thesis binding good thesis statement good thesis
custom papers paper writing services buy college paper pay for paper
how to write a good essay conclusion https://essaywritingservicehelp.com
Nicely put. Kudos.
custom essay writing services canada public service resume writing essay writing service oxford writing services for college papers essay writing service bbb which is the best resume writing service write my essay for me for cheap essay writer generator professional essay writers reviews do my essays
Incredible loads of beneficial facts!
write my research paper for me parts of a research proposal thesis proposal buy term papers online
You suggested it superbly.
doctoral dissertation dissertation proposal define dissertation phd paper
You actually expressed it fantastically.
essay writing service toronto quick essay writer what can i write my essay on do my essay for me cheap write my essay online cheap economics essay writing service custom lab report writing service uk essay writing service i need help writing an essay essay writing service co uk
buy brand neurontin where to buy neurontin or neurontin 800
http://www.visitlisbon.com/__media__/js/netsoltrademark.php?d=gabapentin.pro prescription drug neurontin
neurontin 100mg tablet where can i buy neurontin online and neurontin 50mg cost 32 neurontin
Seriously a lot of beneficial data.
order essay writing service buy dissertation paper masters dissertation writing services uk phd dissertation proposal custom dissertation help reaction paper writing service help me write my college essay who can write a book for me pay somebody to do my essay online essay writer
Cheers. I value this.
order essay writing service term paper writing service best formal proposals cheap research paper writing service summary of research proposal graduate school application essay writing service essay writing service law english paper writing help write my essay help write my essay
Terrific material, Appreciate it.
top assignment writing service need help in writing an essay college essay help essay help service paper writing helper best online essay writing services reviews assignment help essays help the help movie review essay english essay writing help
Thanks. Plenty of facts.
writing a cleaning service proposal reviews of research paper writing service pay to write papers buy custom papers research paper writing service studyclerk customer service essay order of essay writing essay for sale order to write an essay pay for college essay
Nicely put. With thanks!
order custom paper buy a paper buy a paper paper writing service reviews
This is nicely put. .
top uk essay writing services reliable essay writing service writing an analytical essay wikipedia writing service writing a good customer service review cv and linkedin writing service a good thesis statement make thesis statement phd thesis database thesis on service quality and customer satisfaction pdf
Thanks. An abundance of write ups.
high school essay writing where can i pay someone to write my essay buy your essay online pay someone to write paper buy custom essay online unique essay writing service pay someone to write essay best website to buy essays buy cheap essay buy essay online review
Thanks a lot! Lots of info!
essays writing service write essay service top essay writing services best essay writing service reviews
cpm homework help homework help cpm do my math homework for me do my math homework for me
what to write an essay on https://essaywritinghelperonline.com
You actually revealed that really well.
best paper writing services cheap assignment writing service argumentative essay writing free essay writing service
Terrific postings. Regards.
best essays writing service published dissertations online phd research assistance cheap dissertation writing review dissertation writing services marketing assignment writing service thesis in a paper essay thesis statement master thesis writing service compare and contrast thesis statements
Good data. Thanks!
writing a good customer service review cheap thesis writing services thesis binding service liverpool food service industry thesis write my thesis statement for me custom college essay writing service buy essay writing online best essay writing service free essay writing service cheap letter writing service project
Beneficial content. Thank you.
thesis writing doctoral thesis thesis creator good thesis statements
Nicely put, Regards!
the cheapest essay writing service write my paper for me com what i want to do with my life essay top essay writer people who write essays for you best and cheapest essay writing service order of dissertation chapters best research proposal writing service phd research proposal help dissertation proposal writing help
Thanks a lot! Ample knowledge.
cover letter writing service essay writing service cheap cheap essay writing services letter writing service
best essay writing service essay writing service paperhelp need help writing an essay
writing about yourself essay https://essayssolution.com
You actually expressed it really well!
writing a book title in an essay history essay help helping people essay essay help websites custom essay writing help science essay writing service argumentative thesis statement professional thesis writing services phd thesis defense debatable thesis
Thank you. I like it!
write a essay for me write my research paper for me write a essay for me professional essay writers
Kudos. Excellent stuff.
essay writing template assignment on research proposal best site to buy research paper research proposal writers for research papers best online essay writing services best master thesis writing service narrative essay thesis statement thesis revision service example thesis
Really quite a lot of superb knowledge.
linkedin profile writing service ireland buy essay paper paying someone to write your paper cheap essay to buy order essay online writing a good customer service review writing dissertation service dissertation writers retreat capella dissertation writing advice review dissertation writing services
Seriously quite a lot of wonderful material.
pay to write essay pay for paper buy essays online buy essays cheap
With thanks, Ample write ups!
thesis binding thesis statment doctoral thesis thesis binding
essay help service best essay service writing a conclusion for an essay essay writing service coupon
the best college essays https://homeworkcourseworkhelps.com
Regards, I enjoy this.
essay writing service mba essay writing service uk customer service email writing examples term paper writing service best essays writing service essay writing service no plagiarism write my resume for me essay writter i need someone to write a business plan for me expert essay writers
You actually mentioned it wonderfully!
best essay service online essay writers how to write an analytical paper paper writer cheap essay writer no plagiarism college paper writing service essay writing service cheap are there any good essay writing services oil and gas resume writing service personal essay writing service
Truly lots of superb tips.
best canadian essay writing service how much does a professional resume writing service cost are essay writing services illegal real essay writing service bartleby writing customer service number college essays writing essay writing service co uk review essay writing techniques essay writing help master thesis writing service uk
Amazing a good deal of fantastic information.
essay writing help online research project proposal phd thesis proposals proposal writing company cheap custom term paper writing a service level agreement template do my algebra 2 homework for me free how to get my kid to do homework pay someone to do my homework online i didn t do my homework excuses
Amazing material. Appreciate it!
essay writing paper how to write a reflective paper help write my paper best essay writers writing my paper for me essay writing service reviews best service proposal thesis buy college research paper phd research proposal writing a scientific proposal
Whoa plenty of terrific knowledge!
fast writing service essay writing service houston best essay writing service yahoo essay writing site essay writing service illegal writing an argumentative essay dissertation abstracts online define dissertation write dissertations definition of dissertation
Whoa all kinds of terrific information.
write my paper for me essay writer make an essay writing essays
Wonderful information. Thank you.
professional curriculum vitae writing service the proposal online term paper order developing a research proposal research proposal for phd writing a customer service complaint letter master thesis writing service a thesis statement about public service implied thesis statement thesis statement literary analysis
You made your stand very nicely!!
oil and gas resume writing service university paper writing service white paper writing service research paper paper help monthly paper writing service what is the cheapest essay writing service essay writter can i pay someone to write my research paper online paper writer write my biology paper
Nicely put, Cheers.
essay writing help essay help how to write a college essay essaytyper
do my programming homework do my math homework for me homework xyz homework
focus on writing paragraphs and essays https://essaywritingservicebbc.com
Awesome write ups, Regards!
customer service writing training buy essays online reviews order cheap essay online buy college essay papers order of essay writing essay writing in english letter writing service berkeley writing an essay in apa format professional paper writing service private essay writing service
Regards, I enjoy it.
do my homework for free can you do my homework homework pay to do my homework
You said it nicely.!
paper writing pay for paper my paper writer college papers for sale
Whoa a lot of beneficial tips.
best resume writing service argumentative thesis statement thesis statement setup thesis formatting service ireland sample thesis about customer service writing essay service paper writer service capstone paper writing service research paper writing service reviews affordable best paper writing service for you
Info effectively taken.!
buy a research paper proposal writing elements of a research proposal research paper proposal
my paper writer persuasive essay writer write paper research paper writer services
best essay help https://helpwithdissertationwriting.com
This is nicely expressed. .
essay writing process online proposal cheap term paper custom research paper writing service buy custom research paper essay writing tips dissertation proposal writing best dissertation service uk umi dissertation services buy dissertation papers
Kudos! Useful information.
help with my essay best essay writing service help essay essay bot
Thanks, An abundance of advice.
write my essay for cheap write my essay for me free what should i write my college essay about automatic essay writer
Good info. Many thanks.
write paper lined writing paper essay writer free write my research paper for me
Really many of excellent info.
pay to write my essay buy essay pay for research paper pay to write paper
application essay writing service essay writing essay writing paper executive resume writing service
how to write a application essay https://helpwithdissertationwriting.com
You actually revealed this adequately!
write my essay cheap ai essay writer write my essay who can write my essay
Position certainly applied.!
buy essays cheap buy essay pay someone to write my college essay pay to write my essay
You said it nicely..
website that writes essays for you writing a personal essay essay writer no plagiarism write my essay for me free
college paper writing service buying papers for college cheap research paper writing service paper help
writing a proper essay https://argumentativethesis.com
This is nicely expressed. .
writing a thesis statement define thesis statement thesis titles thesis statement
Excellent knowledge. Cheers!
dissertation data analysis help phd dissertation writing custom dissertation writing services writing dissertation
Many thanks. I appreciate this!
write my term paper persuasive essay writer essay writers online ai essay writer
kindergarten writing paper pay someone to write a paper write my research paper for me my paper writer
please write my essay for me https://customthesiswritingservice.com
Really all kinds of wonderful advice.
do my essay write my essays online write my essay for cheap do my essay for me
You actually expressed this really well.
research proposal apa thesis proposal research paper writer buy term papers online
Superb write ups, Kudos!
online essay writer write my paper write my paper reviews essay writer free
order custom paper custom papers buying papers for college pay for paper
where can i buy an essay online https://theessayswriters.com
Useful tips. Thanks!
phd thesis database thesis statement a thesis statement doctoral thesis
Thanks a lot! Fantastic stuff!
thesis proposal example thesis help good thesis statement thesis writing
Fantastic tips. Thanks a lot.
essay writing service review online essay writing services custom essay service custom essay service
paper writing service cheap research paper writing service pay for paper research paper writing service
dissertation abstracts https://essaywritingserviceahrefs.com
Wow lots of beneficial knowledge.
online paper writing service best essay service personal essay writing service best essay writing
Nicely put. Many thanks.
phd dissertation help dissertation meaning dissertation definition dissertation data analysis help
Dear immortals, I need some wow gold inspiration to create.
buying from online mexican pharmacy : mexican pharmacy online – mexican drugstore online
После несчастного случая, мне срочно понадобились деньги на медицинские расходы. На сайте zaim52.ru я нашел обширную подборку новых МФО 2023 года и смог быстро оформить [url=https://zaim52.ru/]займы онлайн на карту[/url]. Это действительно удобно и быстро!
Dear immortals, I need some wow gold inspiration to create.
UGG – это стиль и уют в одном флаконе. Приходите на нашу распродажу 2023 года и купите UGG по самым привлекательным ценам. Вас ждут приятные сюрпризы!
Сайт: [url=https://uggaustralia-msk.ru/]uggaustralia-msk.ru[/url]
Адрес: Москва, 117449, улица Винокурова, 4к1
Планируете идеальный отдых? Termburg – правильный выбор! Посетите [url=https://termburg.ru/]termburg.ru[/url] и убедитесь сами.
Cntbank.ru обеспечивает прозрачные условия для онлайн займа на карту без скрытых платежей и ограничений. Решение финансовых вопросов теперь не займет много времени и сил. Просто выберите нужную сумму и срок, и деньги будут у вас на карте.
На [url=https://parazitizm.ru/]parazitizm.ru[/url] собраны только надежные и лицензированные онлайн казино на деньги с бонусами при регистрации. Мы заботимся о вашей безопасности и интересах, поэтому предлагаем только проверенные игровые площадки. Регистрируйтесь, вносите депозит и получайте дополнительные средства для игры.
Моя кошка внезапно заболела, и мне нужны были деньги на лечение. Я нашел сайт cntbank.ru и быстро оформил срочный займ на карту. Благодаря простому процессу и быстрому получению денег, я смог оплатить лечение и вернуть свою кошку домой.
Грузчики и вывоз мусора Санкт-петербург musoroboss.ru
Представляем Вашему вниманию компанию МусорБОСС, которая занимается вывозом крупногабаритного мусора по Санкт-Петербургу и Ленинградской области. Работаем на основании специальной лицензии по нормативам СанПин, 24 часа в сутки и без выходных дней. По всем вопросам заходите на сайт musoroboss.ru или позвоните по контактному телефону.
По поиску [url=https://musoroboss.ru/product/vyvoz-musora-s-uchastka/]вывоз мусора с участка[/url] Вы на верном пути. Мы уже много лет промышляем вопросами вывоза строительного мусора, который не рекомендуется выбрасывать в простые мусоропроводы. Весь мусор идет исключительно на переработку. За исключением вывоза, мы также делаем демонтажные работы. Среди них: демонтаж ангаров, дачных домиков, бань, в квартирах, гипрока, железобетона, заборов, балконов и лоджий, в старом фонде, крыши, снос загородных домов, плитки, стен и перегородок, фундамента и многого подобного. В нашей компании профессиональные грузчики и водители различных транспортных средств, которые отлично справятся с самой сложной работой.
Оказываемые услуги разнообразны: вывоз мусора КАМАЗом «Мамонт» до 36м3, вывоз мусора с участка, вывоз порубочных остатков, уборка мусора на участке, вывоз снега, вывоз макулатуры и многие другие. К всякому заказу мы пытаемся найти персональный подход и стараемся решить проблемы по факту. Обращайтесь по любым нерешенным вопросам и мы найдем как прийти к отличному решению совместно.
Для срочного подбора необходимых Вам услуг пришлите фото мусора на онлайн портале musoroboss.ru уже сегодня. Не забудьте указать Ваш адрес и условия погрузки, такие как присутствие лифта, этаж и требуются ли грузчики. Оператор оформит заявку в самые быстрые сроки и отправит Вам необходимую машину. Наш автопарк очень большой и под любой случай будет подходящий вариант. Это: КАМАЗ Пухтовоз, ГАЗель, гусеничный экскаватор, погрузчик и другие.
Забронировать [url=https://musoroboss.ru/product/vyvoz-metalloloma/]вывоз металлолома спб из квартиры[/url] возможно по контактному телефону +7(921)326-66-66 или на нашем сайте. Офис работает по графику с 9:00 до 21:00, а вывоз мусора осуществляется круглосуточно. Наш адрес: Санкт-Петербург, дорога на Турухтанные Острова, 10. Звоните, оформляйте заявку на сайте, будем рады Вам помочь!
Однажды ночью мне позвонил друг и сказал, что попал в затруднительное положение. Ему срочно нужна была финансовая помощь. Я не мог оставить его в беде и начал искать, где можно быстро взять займ. Наткнулся на [url=https://credit-info24.ru/]займ на карту круглосуточно без отказа онлайн[/url] и оформил всё буквально за пять минут. Другу удалось решить свои проблемы, и он был мне очень благодарен.
ventolin hfa 90 mcg inhaler – Encouraging students to actively engage in medication safety audits, quality improvement initiatives, and root cause analyses can enhance their problem-solving skills and critical thinking abilities
Wow tons of excellent data!
top essay writing services essay writing service in london custom dissertation writing service
Улучшите свои медицинские знания с maps-edu.ru! Наш сайт предлагает профессиональные курсы для медработников дистанционно. Получите аккредитацию и поднимите квалификацию без отрыва от работы.
Чтобы ваш интернет-магазин стал успешным, необходимо уделить внимание [url=https://www.umseo.ru/]seo продвижение[/url] . Это включает в себя как внутреннюю оптимизацию сайта, так и внешние факторы, такие как контекстная реклама и работа с социальными сетями. Правильный подход поможет увеличить продажи и расширить клиентскую базу.
I was suggested this website through my cousin. I’m not positive whether this publish is written through him as nobody else recognise such detailed about my problem. You are incredible! Thanks!
Many thanks, Excellent information!
what website will write a paper for me compare and contrast essay engineering thesis writing service
Point nicely utilized..
buy essay online writing service best resume writing service in dallas how to start a writing service
Many thanks. Helpful information!
will writing service surrey mba essay writing service best essay writing service 2018 reddit
You actually reported this superbly.
pro essay writing service reviews change words in essay private essay writing service
mail bomb – (Info Email bomber https://t.me/s/floodservice/265 )
Email Bombing – email flood or email hoax (DOS attack) or cluster email bombing, what are they actually doing?
A huge number of emails are sent to e-mail. This usually means that the @FloodService_bot bot specifically targets the victim’s mailbox associated with your email.
These emails are intended to make fun of friends or distract the victim from any security messages or other emails.
I am glad to present you a mail flood bot with a convenient menu and flexible settings!
The cost of the service is $ 2 = 1000 letters.
You specify the time of the flood and the number of letters yourself, or choose the “FAST FLOOD” function
During the flood, a sufficient number of letters arrive so that the owner would miss an important letter!
The bot will flood more than you ordered. On average, 30% more than ordered.
Flood email, Floods Email, Email flooding, gmail flood, email bomber, flood hotmail, flood online,email flooding, email flood bot, email flooded with spam, email flooding service, email flooded with subscriptions, email flooder bot, email bomber 2023, email bomber 2024, email spam bot online, email spammer bot free, spam bot, бот по флуду почт, сервис по флуду почт, услуги по флуду, флуд услуги.
@FloodService_bot – Лучший емаил бомбер на рынке!
http://withoutprescription.guru/# prescription drugs without doctor approval
You actually revealed that wonderfully!
free no download casino games valid no deposit bonus codes for red dog casino red dog casino bonuses
Thank you, I value this!
online casino no deposit free chip reddog casino review cash bandits 2
You’ve made your position quite effectively!!
high stakes online casino https://red-dogcasino.online/ dog casino
Seriously many of fantastic material!
high stakes games red dog casino no deposit codes 2023 red dog casino app
Great info. Cheers!
casino for free online casino free chip no deposit video poker real money online
You expressed this superbly!
red dog casino codes credit card casino empire casino online login
Wonderful information, Cheers.
casino games download red dog casino 100 no deposit bonus codes 2023 online casino deposit
сайт gama casino
http://skodarapidclub.ru/forum/showthread.php?p=1407681
Игровые автоматы в России принимают новое измерение с Gama Casino. Взлетайте вместе с нами на вершину азартных впечатлений, где каждая ставка — это шанс доказать свое превосходство. Гама Казино дарит вам множество вариантов, чтобы сделать ваш путь к победе уникальным и неповторимым.Широкий ассортимент игровых автоматов, представленных на Gama Casino, словно открывает карту сокровищ: каждая игра – это ключ к новому миру призов и увлекательных историй. Гама Казино готово предоставить вам билет в мир азартных приключений, где вы сможете доказать свое мастерство и сорвать внушительный куш.
Вавада казино сайт
http://uid.me/dmitriy_volerot#
Казино Вавада – это не просто игровая площадка, это атмосфера азарта, уникальных возможностей и незабываемых впечатлений. Здесь каждый спин, каждая ставка – это шанс изменить свою судьбу. Войдите в увлекательный мир Вавада Казино и станьте частью этой захватывающей истории выигрышей и успехов!Здесь вы найдете не только знакомые слоты, но и те, которые поразят своей уникальностью. Наша команда тщательно отбирает самые захватывающие и новаторские игры, чтобы каждый спин был настоящим открытием. Вавада Казино предлагает богатство вариантов – от классических фруктовых машин до современных слотов с захватывающими сюжетами.
Really tons of superb facts!
red dog casino login red dog casino 100 no deposit bonus codes instant casino
Incredible a lot of very good material!
casino rtp red dog casino bonus codes red dog no deposit bonuses
Whoa a good deal of fantastic info.
regal riches red dog online casino casino download https://reddog-casino.site/ real money gambling games 100 free spins reddog casino
You actually explained it fantastically.
online blackjack free https://reddog-casino.site/ casino minimum deposit
You stated that very well.
is red dog casino legit video poker real money tycoon slots
Many thanks, I appreciate this.
does casino take credit cards no deposit bonus codes for red dog casino deuces wild bonus poker
Мы понимаем, что каждый человек имеет свои финансовые потребности. На МИР-ЗАЙМОВ.РФ вы найдете разнообразные предложения займов, которые доступны студентам, работающим, предпринимателям и даже пенсионерам. Все возрастные группы могут получить необходимую финансовую поддержку.
You revealed it wonderfully!
no download casinos red dog casino 100 free chip crypto blackjack
Great stuff. Appreciate it!
casino rtp reddog casino review no deposit bonus codes 2020
Valuable data. Thanks.
blackjack perfect pairs red dog casino no deposit codes free slots no download https://red-dogcasino.website/ deposit game red dog bonus codes free slots no download
покердом
https://render.ru/ru/artist/255544/about
Добро пожаловать в увлекательный мир азарта и возможностей на официальном сайте PokerDom Casino! Здесь каждый игрок — как путешественник, готовый исследовать безграничные просторы слотов и испытать свою удачу в поисках богатства. Покердом Казино приглашает вас скачать клиент на ПК и окунуться в потрясающий мир лицензионных автоматов, где каждый спин барабанов может изменить вашу жизнь.Скачать клиент на ПК — это ваш билет в мир PokerDom Casino, где каждый ставит на кон свою удачу и готов пойти на риск ради счастья. Покердом Казино предоставляет вам возможность играть в слоты на реальные деньги в уютной обстановке вашего дома, ощущая весь палитру азартных эмоций.
You said it adequately!
cash bandit european roulette casino roulette on line https://reddog-casinos.website/ online video poker for real money red dog casino no deposit bonus 2023 online roulette real money
Amazing tons of wonderful info.
online video poker for money red dog casino bonus codes lucky6
Kudos, Lots of posts.
red dog no deposit bonus codes https://red-dogcasino.website/ aladdin’s wishes
Cheers. A lot of advice!
high stakes casino red dog casino promo codes red dog casino no deposit
Wonderful material, Thank you.
enchanted casino real money free blackjack win real money online casino deposit
Thank you, I value this.
tiger casino game red dog no deposit bonus codes redhotcasino https://reddog-casinos.website/ blackjack for free or real money european roulette casino atlantis slot
You expressed this really well.
achillis the game valid no deposit bonus codes for red dog casino rollete online
Very good info. Regards!
video poker for real money red dog casino promo codes no deposit free chip https://red-dogcasino.online/ play blackjack real money online craps gambling online roulette for real money
Seriously lots of excellent facts.
bc game hack script https://bcgamecasino.fun/ bc game shitcode 2023
Fine facts. Many thanks.
bc clemson game 2016 bcgame com bc lions game last night
You made your point pretty clearly.!
bc game free spin bc game promo code bc fsu game
Seriously plenty of wonderful tips.
european roulette red dog casino login red dog casino welcome bonus https://red-dogcasino.online/ free chip no deposit bonus reddog casino bonus no download slot
Cheers, An abundance of material!
bc lions game tonight bc lions last game video game companies in vancouver bc
You have made your point pretty well!.
catch fish game rudolphs revenge enchanted casino online https://reddog-casino.site/ mobil roulette reddog no deposit bonus dog casino
Thank you! Loads of write ups.
bc fish and game bc. game bc game shooting
Terrific tips. Cheers.
bc lions game last night https://bc-game-casino.online/ bc lions saskatchewan game
Wow all kinds of fantastic material.
bc game com bc game bonus codes bc game crypto casino
Helpful data. Appreciate it.
casino mania slots real money red dog no deposit bonus rudolphs revenge https://reddog-casino.site/ free play slots no download casino banking archilies the game
Awesome material, With thanks!
watch bc lions game live bc game app download bc game strategy
Онлайн казино на реальные деньги для андроид
https://gozee.ru/
Онлайн казино на реальные деньги для андроид
https://gozee.ru/
Онлайн казино на реальные деньги для андроид
https://gozee.ru/
Онлайн казино на реальные деньги для андроид
https://gozee.ru/
Beneficial write ups. Cheers.
bc clemson game cm bc high football game bc game deposit bonus
Онлайн казино на реальные деньги для андроид
https://gozee.ru/
Онлайн казино на реальные деньги для андроид
Онлайн казино на реальные деньги для андроид
Онлайн казино на реальные деньги для андроид
https://gozee.ru/
You actually said this wonderfully.
bc game level up rewards bcgame clemson bc game
With thanks, I like it!
tower legend bc game bc lions game bc game clone
Terrific facts. Many thanks.
neosurf casino free bonus codes for existing customers 2023 casino banking https://red-dogcasino.website/ red dog casino no deposit code red dog casino 100 no deposit bonus codes 2023 online video poker for real money
Amazing stuff. Many thanks.
bc lions game live https://bcgamecasino.pw/ bc duke game
Fine facts. With thanks!
bc game app watch the bc lions game online bc game promo code no deposit
Amazing loads of wonderful knowledge.
bc game shitcode 2023 today bc game app download bc syracuse football game
Good content, Kudos.
valid no deposit bonus codes for red dog casino red dog casino australia download online casino https://reddog-casinos.website/ archiles the game rollete online high stakes casinos
You reported it wonderfully.
bc game kyc bc game crash predictor bc game countries
Good forum posts. With thanks!
bc game unlock bcd bc. game notre dame bc game
Nicely put, Cheers!
bc game crash script ghost bc game how to unlock bcd in bc game
Regards! A lot of info.
score bc lions game today https://bcgamecasino.website/ codigo bc game
Thanks a lot. An abundance of write ups!
clemson bc game what channel is the bc lions game on bc game casino shitcode
Thanks! Lots of forum posts.
ваучеры 1win 1win промокод россия 1win промокод при регистрации https://1winoficialnyj.online/ 1win зеркало сайта скачать 1win ставки 1win телефон официальное приложение
You reported that effectively!
ваучер 1win телеграм 1win bet 1win зеркало скачать онлайн
Many thanks. Lots of write ups.
1win проверяем и бонусы 1win бонус https://1winoficialnyj.online/ 1win авиатор скачать
You said it very well..
1win зеркало казино промокод 2023 jetx 1win aviator 1win игра
You actually revealed this really well.
скачать 1win зеркало как использовать бонусы в 1win 1win скачать на телефон
With thanks! I value this!
1win бк зеркало 1win бонус 5000 как использовать проверка 1win https://1winoficialnyj.online/ 1win casino промокод 1win официальный сайт россия how to use bonus in 1win
You expressed that superbly!
зеркало 1win рабочее на сегодня прямо сейчас 1win ваучер 1win лаки джет https://1winoficialnyj.site/ 1win скачать на пк como usar o bonus do 1win бонус 1win
You said it adequately..
промокод при регистрации 1win 1win crazy time скачать 1win с официального сайта
Nicely put. Thanks a lot.
как воспользоваться бонусами 1win https://1winoficialnyj.site/ бонусы спорт 1win как использовать
You actually explained this superbly.
1win проверяем слоты и бонусы 1win 1win ваучер на деньги 1win plinko
Effectively spoken without a doubt! !
что делать с бонусами в 1win 1win букмекерская 1win промокод при регистрации 2023 https://1winoficialnyj.site/ 1win рабочее 1win мобильное приложение 1win зеркало казино промокод 2024
You explained this adequately.
1win review как вывести с 1win где вводить промокод в 1win https://1winoficialnyj.website/ 1win зеркало скачать приложение 1win скачать android 1win автоматы официальный сайт
You said it adequately.!
aviator игра 1win авиатор игра 1win 1win uz
Valuable material. Thanks.
1win состав кс го бонусы спорт 1win как отыграть бонус 1win
Incredible all kinds of very good info.
1win игры 1win casino скачать как скачать 1win https://1winoficialnyj.website/ 1win casino бк 1win 1win телефон приложение
Nicely put. With thanks.
1win не выводит деньги https://1winoficialnyj.website/ как поменять почту в 1win
Thanks a lot. Terrific information.
1win бонус за установку приложения 1win бк игра как я вынес и ограбил стратегия 1win игра
Awesome data. Thank you!
1win проверяем и бонусы 1win бонус 1win приложение 1win мобильное приложение скачать
lywiredrawing.com Wire Drawing Dies lywiredrawing.com.
Nicely put. Appreciate it.
1win app real or fake 1win отзывы 1win пополнение https://1winregistracija.online/ 1win brasil 1win букмекерская контора как потратить бонусы казино в 1win
Regards! A lot of forum posts.
скачать 1win официальный сайт 1win bet 1win og прогноз
You actually suggested that fantastically!
1win кейсы скачать скачать 1win на андроид вся правда об алгоритмах aviator 1win обзор https://1winvhod.online/ 1win bonus benvenuto 1win top 1win yukle
hxjglobal.com Hydraulic Pump hxjglobal.com.
Terrific content. Cheers.
что такое бонусы спорт в 1win 1win официальный сайт бонусы на спорт 1win
Perfectly spoken truly. .
1win букмекерская скачать 1win приложение 1win развод https://1winvhod.online/ 1win download 1win букмекерская контора реальный актуальные бонусы 1win 2023 казино 1win на сегодня
You definitely made the point!
зеркало 1win россия 1win букмекерская контора зеркало на сегодня 1win бесплатная ставка
Truly all kinds of superb knowledge!
фриспины 1win https://1winvhod.online/ зеркало 1win работающее сегодня
Cheers, Lots of advice.
1win бк зеркало 1win рабочее зеркало 1win официальное зеркало https://1win-vhod.online/ lucky jet best big win lucky jet tricks lucky jet 1win 1win рабочее зеркало ваучеры 1win 2023
Reliable facts. Many thanks.
1win рабочее зеркало 1win kz casino 1win казино онлайн 1win casino
Amazing posts. Appreciate it!
1win бонусы казино как использовать бонусы спорт 1win 1win скачать apk
You actually expressed that well.
en el en 1win 1win cdigos promocionales 1win juegos 1win скачать на айфон 1win crazy time https://1win-vhod.online/ 1win букмекерская контора официальный сайт 1win casino games скачать 1win зеркало
Fine information. Thanks a lot.
forze 1win прогноз 1win приложение скачать 1win как скачать
Many thanks. Numerous posts.
1win контора отзывы 1win 1win казино рулетка
Thanks a lot. Loads of advice!
бонусный счет 1win 1win скачать телефон 1win рабочее на сегодня
This is nicely expressed! .
реальный обзор 1win зеркало промокод 1win сайт скачать 1win с официального сайта
Very good write ups. Kudos.
1win скачать на телефон 1win официальный 1win ставки россия
Good tips. With thanks!
1win casino 1win зеркало казино промокод 2024 как пользоваться бонусами 1win
This is nicely said! .
1win зеркало скачать online зеркало 1win работающее сегодня 1win ru
Excellent facts. Regards.
1win ставки 1win inscription 1win лицензия
И, конечно, не забываем про тех, кто предпочитает [url=http://antiban.pro/ru/blog/142]инстаграм вход с компьютера[/url]. Ведь иногда так удобно сидеть за большим экраном и наслаждаться любимыми постами, не ограничивая себя маленьким экраном телефона. Это дает нам еще больше свободы и удобства в использовании нашей любимой социальной сети. Инстаграм всегда рядом, где бы мы ни были и каким бы устройством ни пользовались!
Antiban.pro мы поможем решить проблемы:
1 – Заблокировали аккаунт
2 – Заблокировали действия в аккаунте
3 – Проблемы с привязкой Facebook
4 – Меня взломали в Instagram
5 – Меня взломали в Facebook
vidalista ct 20 mg https://community.alteryx.com/t5/user/viewprofilepage/user-id/524453/ ivermectin scabies dosage
Thank you, Terrific information.
1win skachat мобильное 1win официальный сайт вход тестирую 1вин 1win 1win промокод 2024
You said this really well.
lucky jet отзывы 1win ваучер 1win ваучер 1win телеграм
Incredible a good deal of useful facts!
1win cs go матчи 1win бк 1win официальное приложение
Fantastic facts, Regards.
бк 1win россия 1win бк cloud9 1win
Excellent knowledge. Cheers.
1win casino бездепозитный бонус 1win скачать зеркало отзывы 1win
You actually stated that well!
1win телефон мобильный 1вин 1win зеркало казино 1вин промокод 1win казино
You explained that superbly!
1win онлайн казино 1win crazy time cloud9 1win
Активный сабвуфер в авто dbshop.ru
Зовём Вас в самый лучший интернет магазин автоакустики DBShop, где есть огромный список составных частей для самого чистого звука конкретно в Ваш автомобиль. Мы осуществляем работу в представленной области уже большое количество лет и имеем контакты с мировыми фирмами прямиком, к примеру: Deaf Bonce, DL Audio, Kicx, PRIDE и другие. Поэтому стоимость у нас весьма соблазнительная и не имеет больших накруток.
По теме [url=https://dbshop.ru/product/perekhodnik_dlya_podklyucheniya_v_shtatnyy_akusticheskiy_razem_vesta/]штатная акустика веста[/url] переходите на указанный веб ресурс. На dbshop.ru есть вся обширная информация о нашей организации. Мастера, которые знают толк в своей работе, ориентированы на то, чтобы подобрать в Ваш авто идеальный сабвуфер. Учитывая пожелания и финансовый лимит клиента. Продукцию, которую Вы найдете в нашем перечне: автомагнитолы 2DIN, усилители, короба, питание системы, подиумы и многое другое.
Тут самые приятные цены, которые не влияют на потерю качества вовсе. А всё оттого, что мы работаем напрямую от поставщиков. Большинство товаров есть в наличии, но ещё можно выбрать товары под заказ, если конкретной модели сейчас нет. Доставляем точно в установленный срок, а постоянным заказчикам предлагаем гибкую систему скидок. Все товары, купленные у нас имеют сертификаты и гарантийный срок. Доставка происходит в любой город России, а при заказе от 9900 рублей доставка происходит бесплатно.
Если Вы хотели найти [url=https://dbshop.ru/]автозвук интернет магазин[/url] в сети интернет, то Вы на верном пути. Приобрести товары на онлайн портале dbshop.ru весьма просто. Следует кидать в корзину необходимые Вам товары, а следом оформить заказ. Напишите Ваше ФИО, контактный телефон, Email, способы оплаты и доставки, и ждите свой заказ. Если появились проблемы, звоните по контактному телефону, который указан ниже.
Мы находимся по адресу: г. Ижевск, ул. Коммунаров, 244. Режим работы с понедельника по пятницу с 9:00 до 19:00, в субботу и воскресенье с 10:00 до 18:00. Наш номер контактного телефона +7(3412)91-21-21 звоните и задавайте возникшие вопросы.
Xanax: Your path to a more peaceful existence. See how Buy Xanax for Quick Anxiety Relief can transform your approach to managing stress. Take the first step today!
Ищете надежный займ онлайн? Наш сайт объединяет более 50 МФО России, предлагая широкий выбор микрозаймов. У нас вы найдете как новые, так и малоизвестные микрофинансовые организации. Мы предоставляем эксклюзивные рекомендации по оформлению заявок, чтобы вы с высокой вероятностью получили одобрение. Наши услуги доступны всем гражданам старше 18 лет, даже без подтверждения дохода. Получите деньги удобным для вас способом: на карту, электронный кошелек или наличными в офисе МФО.
Mikro-Zaim-Online – [url=https://mikro-zaim-online.ru/]займы без отказа на карту онлайн срочно[/url] как выбрать лучший микрозайм: советы экспертов.
Say goodbye to anxiety with Xanax. Explore Attain Mental Wellness with Xanax to see how it can provide peace to your life. Join us on your journey to a peaceful mind now.
Xanax: Your path to a calmer existence. Find out how Ease Your Anxiety with Effective Xanax can change your approach to managing stress. Take the first step today!
Эффективное теплосбережение фасадов — комфорт и бережливость в вашем жилье!
Согласитесь, ваш домовладение заслуживает превосходного! Изоляция наружных стен – не просто решение для сбережения на тепле, это вкладывание в удобство и долголетие вашего домовладения.
✨ Почему теплосбережение с нами-мастерами?
Мастерство в своем деле: Наша бригада – профессионалы своего дела. Мы заботимся о каждой отдельной, чтобы обеспечить вашему жилью идеальное тепловая изоляция.
Стоимость теплоизоляции: Наша компания ценим ваш бюджетные ограничения. [url=https://stroystandart-kirov.ru/]Утепление стен дома снаружи цена[/url] – начиная с 1350 руб./кв.м. Это вложение средств в ваше удобное будущее!
Энергосберегающие решения: Забудьте о термических потерях! Наши не только сохраняют теплоту, но и дарят вашему недвижимости новый уровень тепла энергоэффективности.
Оформите свой домашнюю обстановку теплым и стильным!
Подробнее на [url=https://stroystandart-kirov.ru/]http://www.n-dom.ru/
[/url]
Не предоставляйте свой домовладение на произвольное решение. Доверьтесь профессионалам и создайте комфорт вместе с нашей командой!
Battling anxiety? Xanax might be the relief you need. Explore Experience the Difference with Our Xanax and see how it can improve your life. Start your path to a calmer future now.
Comment se passe l’accouplement chez l’Homme ou acheter viagra
Ready to say goodbye to constant anxiety? Xanax can be your ally in achieving mental wellness. Explore the benefits of Xanax for Stress Management and start your journey to a calmer you. Experience the change today!
Are you seeking a solution to ease your anxiety? Dealing with stress and anxiety can be overwhelming, but with the right support, it’s entirely manageable. Whether you’re facing everyday anxieties or seeking a more lasting solution, our product could be the answer you’re looking for. Learn how Buy Xanax Online – The Path to Wellness can help you in achieving mental calmness. Take the first step towards a stress-free life today and experience the extraordinary benefits for yourself!
What happens if you cough too much ventolin cupon
Xanax – A reliable solution for easing anxiety. Find out how Discover Peace with Trusted Xanax can help you attain stress relief. Begin today!
Combat your anxiety effectively with Xanax. If you’re looking for a way to manage your stress, see how Xanax – The Path to Serenity can assist. Join us today and experience a life with more peace.
Quels sont les nouveaux modeles familiaux tadalafil 20mg biogaran prix
active ingredient in levitra Transforming Healthcare Delivery through Innovative Medications
Мечтал пройти курсы программирования, но финансы не позволяли. Случайно наткнулся на mikro-zaim-online.ru, где мне одобрили 10 000 рублей без процентов. Теперь я осваиваю новую профессию и двигаюсь к своей мечте.
MIKRO-ZAIM – [url=https://mikro-zaim-online.ru/]займ быстро[/url]
Наши контакты: Зеленодольская улица, 36к2, Москва, 109457
Для тех, кто ценит истории о мужестве и героизме, [url=https://turkbiz.tv/voenie/]турецкие сериалы военные[/url] на turkbiz.tv откроют мир драматических событий и несломленных духов. Эти сериалы позволяют не только узнать о военной истории, но и пережить глубокие человеческие эмоции, связанные с борьбой, любовью и выживанием.
По теме [url=https://newswomanblog.win/begovaya]проститутки на беговой[/url] переходите к нам прямо сейчас. Если Вы измучены от скучных и серых будней, а также загруженных рабочих смен, то настало время наградитьни в чем не ограждать себя и получить настоящее развлечение.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://www.binance.com/zh-TC/register?ref=FIHEGIZ8
Мечтал устроить родителям сюрприз на их 30-летний юбилей брака. Деньги копил, но всё улетело на неожиданные расходы. Отчаиваться? Нет уж! На mikro-zaim-online.ru нашел займ на 10 000 рублей без процентов. Банкет был организован, и радость родителей стоила каждого потраченного рубля.
MIKRO-ZAIM – [url=https://mikro-zaim-online.ru/]займ онлайн быстро[/url]
Наши контакты: Зеленодольская улица, 36к2, Москва, 109457
Собираешься сделать [url=https://denezhnye-perevody-iz-rossii.top/]перевести деньги в норвегию[/url] ? На denezhnye-perevody-iz-rossii.top это проще простого! Мы предлагаем тебе удобные и быстрые способы перевода денег в Грузию. Не волнуйся за безопасность: мы используем надежные системы защиты. Просто следуй нашим инструкциям, и деньги быстро достигнут адресата.
Tadalafilo 10 Mg Precio
Willingly I accept. The question is interesting, I too will take part in discussion. I know, that together we can come to a right answer.
Cialis 5 mg prezzo tadalafil 5 mg prezzo cialis 5 mg prezzo
Join the elite ranks of winners at our Mexican casino site. With exclusive rewards and VIP privileges, you’ll be treated like royalty every time you play. tres reyes casino juegos te da mucho.
Wiekszosc slotow dziala tylko z VPN, ale wyprobuj ten bonusy Slottica jednak to dziala dla mnie.
Win big and live the dream at our Mexican online casino. With life-changing jackpots and thrilling tournaments, fortune favors the bold. caliente casino online la clave para una buena vida.
Win big and win often at our Mexican casino platform. With generous payouts and thrilling bonuses, every spin is a chance to change your life. bet mexico casino esto es lo que te diferencia de los demas.
Win big and win often at our Mexican casino platform. With generous payouts and thrilling bonuses, every spin is a chance to change your life. casinos online esto es lo que te diferencia de los demas.
Discover the excitement of online gambling at our Mexican casino site. With secure payments and 24/7 customer support, you can play with confidence and peace of mind. cosina o cocina esto es lo que te diferencia de los demas.
Discover the thrill of victory at our Mexican online casino. With adrenaline-pumping games and heart-stopping excitement, you’ll be on the edge of your seat with every bet. gametwist casino gratis la riqueza esta a tus pies.
Get ready to experience the thrill of victory at our Mexican casino platform. With high-stakes games and adrenaline-pumping excitement, you’ll be on the edge of your seat with every bet. caliente casino en lГnea tienes todo lo mejor.
Win big and win often at our Mexican online casino. With generous payouts and thrilling tournaments, the sky’s the limit when you play with us. caliente te da mas.
Get ready to experience the thrill of victory at our Mexican casino platform. With high-stakes games and adrenaline-pumping excitement, you’ll be on the edge of your seat with every bet. caliente casino app tienes todo lo mejor.
Join the party at our Mexican casino platform. With lively animations and immersive sound effects, you’ll feel like you’re celebrating every time you win. caliente cacino tu camino hacia el exito.
Do you have a spam problem on this website; I also am a blogger, and I was wondering your situation; we have developed some nice methods and we are looking to exchange strategies with other folks, why not shoot me an e-mail if interested.
My#page#site#:
https://ekcochat.com/read-blog/100054
https://gotartwork.com/Blog/%D0%BE%D0%B1%D1%83%D1%87%D0%B5%D0%BD%D0%B8%D0%B5-%D0%B7%D0%B0-%D1%80%D1%83%D0%B1%D0%B5%D0%B6%D0%BE%D0%BC-%D0%BF%D0%BE%D1%81%D0%BB%D0%B5-11-%D0%BA%D0%BB%D0%B0%D1%81%D1%81%D0%B0-%D1%80%D0%B5%D0%B0%D0%BB%D1%8C%D0%BD%D0%BE%D1%81%D1%82%D1%8C-%D0%B8%D0%BB%D0%B8-%D0%BC%D0%B8%D1%84-/262507/
https://telegra.ph/6-Problem-Rossijskogo-Obrazovaniya-v-2024-godu-Analiz-i-Puti-Resheniya-02-20
http://kvartal8b.getbb.ru/viewtopic.php?f=19&t=18014
http://newseducation2015.bestbb.ru/viewtopic.php?id=470#p482
May I just say what a relief to uncover an individual who actually understands what they’re discussing online. You actually know how to bring an issue to light and make it important. A lot more people must look at this and understand this side of your story. I was surprised you aren’t more popular because you certainly possess the gift.
My#page#site#:
http://vkmonline.com/blogs/post/1489018
https://click2connect.community/index.php?do=/public/blog/view/id_119678/title_/
http://www.paladiny.ru/forummess.dwar.php?TopicID=26041
http://www.spiritualpool.com/blog/%D0%B0%D1%82%D1%82%D0%B5%D1%81%D1%82%D0%B0%D1%82-%D0%BE%D0%B1-%D0%BE%D0%B1%D1%80%D0%B0%D0%B7%D0%BE%D0%B2%D0%B0%D0%BD%D0%B8%D0%B8-%D0%BC%D0%BE%D1%81%D1%82-%D0%BC%D0%B5%D0%B6%D0%B4%D1%83-%D1%88%D0%BA%D0%BE%D0%BB%D0%BE%D0%B9-%D0%B8-%D0%BF%D1%80%D0%BE%D1
https://conservatives.click/index.php?do=/public/blog/view/id_119667/title_/
Good post. I learn something totally new and challenging on sites I stumbleupon on a daily basis. It’s always helpful to read through articles from other authors and use something from their web sites.
http://go0gle.coom
http://inter.5bb.ru/viewtopic.php?id=9045#p9097
http://itw.fludilka.su/viewtopic.php?id=2486#p8355
http://www.baikal-biz.ru/forum/viewtopic.php?f=22&t=23683
http://mypenza.ru/forum/index.php?showtopic=62608
http://olvaldenis.mybb.ru/viewtopic.php?id=406#p5860
Ready to enhance your intimate moments? Discover the power of viagra online .
Explore the effectiveness of viagra online and take the first step towards improvement.
What you said made a lot of sense. But, think on this, suppose you added a little information? I ain’t saying your content is not good., but what if you added something that grabbed a person’s attention? I mean %BLOG_TITLE% is a little plain. You could peek at Yahoo’s front page and watch how they create article titles to get people to click. You might try adding a video or a related pic or two to get readers excited about everything’ve got to say. In my opinion, it might make your website a little livelier.
https://clients1.google.hr/url?sa=t&url=https://hottelecom.biz/id/
Aviator Spribe играть с друзьями онлайн
Добро пожаловать в захватывающий мир авиаторов! Aviator – это увлекательная игра, которая позволит вам окунуться в атмосферу боевых действий на небе. Необычные графика и захватывающий сюжет сделают ваше путешествие по воздуху неповторимым.
Aviator Spribe играть с друзьями онлайн казино
Aviator Spribe казино играть на тенге
Добро пожаловать в захватывающий мир авиаторов! Aviator – это увлекательная игра, которая позволит вам окунуться в атмосферу боевых действий на небе. Необычные графика и захватывающий сюжет сделают ваше путешествие по воздуху неповторимым.
Aviator Spribe играть на рубли казино
Good day! This post couldn’t be written any better! Reading this post reminds me of my previous room mate! He always kept chatting about this. I will forward this page to him. Fairly certain he will have a good read. Thank you for sharing!
RybelsusRybelsusRybelsusRybelsusRybelsus
Hi I am so delighted I found your web site, I really found you by accident, while I was browsing on Google for something else, Anyhow I am here now and would just like to say kudos for a remarkable post and a all round entertaining blog (I also love the theme/design), I don’t have time to read through it all at the moment but I have saved it and also added in your RSS feeds, so when I have time I will be back to read more, Please do keep up the fantastic work.
Rybelsus
Hi I am so happy I found your web site, I really found you by error, while I was searching on Google for something else, Nonetheless I am here now and would just like to say thank you for a marvelous post and a all round thrilling blog (I also love the theme/design), I don’t have time to go through it all at the moment but I have saved it and also added in your RSS feeds, so when I have time I will be back to read a lot more, Please do keep up the excellent work.
writing service
Мы коллектив специалистов по продвижению в интернете, специализирующихся на увеличении трафика и повышении рейтинга вашего сайта в поисковых системах.
Мы преуспели в своей деятельности и предоставим вам доступ к нашему опыту и навыкам.
Что мы можем вам предложить:
• seo раскрутка заказать
• Подробный анализ вашего сайта и создание персонализированной стратегии продвижения.
• Модернизация контента и технических аспектов вашего сайта для оптимальной работы.
• Систематический мониторинг и анализ результатов с целью улучшения вашего онлайн-присутствия.
Подробнее https://seo-prodvizhenie-ulyanovsk1.ru/
Наши клиенты уже видят результаты: увеличение посещаемости, улучшение рейтинга в поисковых системах и, конечно, рост бизнеса. Мы можем предоставить вам бесплатную консультацию, для обсуждения ваших потребностей и разработки стратегии продвижения, соответствующей вашим целям и финансовым возможностям.
Не упустите возможность увеличить прибыль вашего бизнеса в онлайн-мире. Обращайтесь к нам уже сегодня.
Производимые торгово-промышленным объединением тренажеры для кинезитерапии trenazhery-dlya-kineziterapii.ru и специально созданы для восстановления после травм. Устройства имеют интересное соотношение цены и качества.
Выбираем очень доступно блочную раму с облегченной конструкцией. В ассортименте для кинезитерапии всегда в реализации модели блочного и нагружаемого типа.
Изготавливаемые тренажеры для реабилитации обеспечивают мягкую и безопасную тренировку, что особенно важно для пациентов в процессе восстановления.
Станки обладают подстраиваемым сопротивлением и уровнями нагрузки, что позволяет индивидуализировать силовые тренировки в соответствии с задачами любого больного.
Все тренажеры актуальны для ЛФК по руководству врача физиотерапевта Бубновского. Оснащены поручнями для комфортного выполнения тяговых движений в наклоне или лежа.
Why users still use to read news papers when in this technological globe all is accessible on web?
https://www.myung-sung.kr/bbs/board.php?bo_table=free&wr_id=2899092
демонтаж москва
https://demontagmoskva.ru/
May I simply just say what a relief to uncover someone who actually knows what they are talking about on the web. You actually know how to bring an issue to light and make it important. A lot more people have to check this out and understand this side of the story. It’s surprising you are not more popular because you definitely possess the gift.
Официальный сайт Gama casino
Недавно мне понадобилось сменить входную дверь в квартире. Выбрал сайт dveri-msk1.ru, нашел подходящую модель и оформил заказ на монтаж. Мастера приехали в назначенное время, быстро и качественно установили новую дверь. Очень доволен сервисом и результатом – теперь чувствую себя намного безопаснее!
Приветики!
Были ли у вас случаи, когда приходилось писать дипломную работу в крайне ограниченные сроки? Это действительно требует большой ответственности и трудоемкости, но важно не отступать и продолжать активно участвовать в учебном процессе, как я.
Для тех, кто умеет эффективно находить и использовать информацию в сети, это действительно помогает в процессе согласования и написания дипломной работы. Больше не нужно тратить время на посещение библиотек или организацию встреч с научным руководителем. Здесь, на этом ресурсе, предоставлены надежные данные для заказа и написания дипломных и курсовых работ с гарантией качества и доставкой по всей России. Можете ознакомиться с предложениями тут https://rudik-diploms365.com, это проверенный источник!
https://gruppa365-diploms-srednee.com/
купить диплом университета
купить диплом о среднем специальном
купить диплом нового образца
купить диплом Вуза
купить аттестат
Желаю каждому прекрасных оценок!
Здравствуйте!
Было ли у вас когда-нибудь так, что приходилось писать дипломную работу в очень сжатые сроки? Это действительно требует огромной ответственности и может быть очень тяжело, но важно не опускать руки и продолжать активно заниматься учебными процессами, как я.
Для тех, кто умеет быстро находить и использовать информацию в интернете, это действительно облегчает процесс согласования и написания дипломной работы. Больше не нужно тратить время на посещение библиотек или устраивать встречи с научным руководителем. Здесь, на этом ресурсе, предоставлены надежные данные для заказа и написания дипломных и курсовых работ с гарантией качества и доставкой по всей России. Можете ознакомиться с предложениями на сайте , это проверено!
https://landik-diploms-srednee24.com/
купить диплом Вуза
купить диплом магистра
купить диплом Гознак
купить диплом техникума
купить диплом нового образца
Желаю каждому пятерошных) оценок!
Российский изготовитель реализует диски в интернет-магазине https://diski-dlya-shtang.ru/ для напряженной работы в коммерческих тренажерных центрах и в домашних условиях. Отечественный завод создает тренировочные блины разного посадочного диаметра и любого востребованного веса для разборных гантелей. Рекомендуем к заказу обрезиненные тренировочные блины для силовых занятий. Они не скользят, не шумят и более безопасны. Производимые изделия не нуждаются в постоянном обслуживании и рассчитаны на длительную работу в дома, в квартире. Предлагаем внушительный ассортимент любительских дисков с любым типом защитного покрытия. Оформите отягощения с подходящей массой и посадочным диаметром по доступным ценам напрямую у завода.
Российский изготовитель продает тренировочные диски на ресурсе Diski-Dlya-Shtang для напряженной работы в коммерческих тренировочных залах и в домашних условиях. Завод из России создает блины разного посадочного диаметра и любого востребованного веса для наборных штанг и гантелей. Советуем к заказу прорезиненные тренировочные диски для силовых тренировок. Они не скользят, не гремят и более безопасны. Выпускаемые изделия не нуждаются в постоянном обслуживании и ориентированы на длительную работу в клубах. Предлагаем обширный каталог олимпийских блинов с разным видом покрытия. Оформите отягощения с оптимальной массой и посадочным диаметром по низким ценам напрямую у завода-производителя.
Я обратился в компанию seo-prodvijenie-saytov было необходимо, когда мне нужно было улучшить видимость моего веб-ресурса в поисковых системах. Благодаря комплексной работе команды, использованию актуальных SEO-инструментов и индивидуализированной стратегии продвижения, я заметил значительное повышение трафика и улучшение позиций сайта. Рекомендую их как надежного партнера в SEO-продвижении.
Привет, дорогой читатель!
Приобретите документы об образовании всех ВУЗов России с гарантированной подлинностью и доставкой по РФ без предварительной оплаты – просто, надежно, выгодно!
http://saksx-attestats.ru/
Закажите диплом ВУЗа с доставкой по России без предоплаты и с гарантией подлинности – удобно и безопасно!
Заказать и купить диплом в России без предоплаты и с гарантией, можно только у Нас с гарантией под ключ
Кухни по индивидуальным размерам от Вита Кухни: идеальное сочетание стиля и функциональности
Здравствуйте!
Бывало ли у вас такое, что приходилось писать дипломную работу в крайне ограниченные сроки? Это действительно требует огромной ответственности и напряженных усилий, но важно не опускать руки и продолжать активно заниматься учебными процессами, чем я и занимаюсь.
Для тех, кто умеет искать и анализировать информацию в интернете, это действительно облегчает процесс согласования и написания дипломной работы. Не нужно тратить время на посещение библиотек или устраивать встречи с дипломным руководителем. Здесь, на этом ресурсе, предоставлены надежные данные для заказа и написания дипломных и курсовых работ с гарантией качества и доставкой по России. Можете ознакомиться с предложениями по ссылке купить диплом ссср, это проверено!
https://www.chrissaundersmd.com/question/%D0%BA%D1%83%D0%BF%D0%B8%D1%82%D1%8C-%D0%B4%D0%B8%D0%BF%D0%BB%D0%BE%D0%BC-%D1%83%D0%BD%D0%B8%D0%B2%D0%B5%D1%80%D1%81%D0%B8%D1%82%D0%B5%D1%82%D0%B0-%D0%B6%D0%B8%D0%B7%D0%BD%D0%B5%D0%BD%D0%BD%D1%8B/
где купить диплом
купить диплом ссср
купить аттестат школы
купить диплом колледжа
купить диплом института
Желаю любому прекрасных отметок!
Все о современных технологиях
Преимущества песка и щебня по ГОСТу: качество и надежность материалов для строительства
VSDC Free Video Editor: Your Ultimate Tool for Creating Stunning Videos
Привет, дорогой читатель!
Бывало ли у вас такое, что приходилось писать дипломную работу в очень ограниченные сроки? Это действительно требует большой ответственности и тяжелого труда, но важно не сдаваться и продолжать активно заниматься учебными процессами, так же, как и я.
Для тех, кто умеет эффективно использовать интернет для поиска и анализа информации, это действительно облегчает процесс согласования и написания дипломной работы. Не нужно тратить время на посещение библиотек или организацию встреч с дипломным руководителем. Здесь представлены надежные данные для заказа и написания дипломных и курсовых работ с гарантией качества и доставкой по всей России. Можете ознакомиться с предложениями по ссылке , это проверенный способ!
http://carpediem.mybb.ru/viewtopic.php?id=121#p184
купить диплом о высшем образовании
купить диплом ссср
купить диплом нового образца
купить диплом цена
купить диплом в Москве
Желаю всем прекрасных оценок!
Ландшафтный дизайн: создание гармоничного и уникального окружения
Здравствуйте!
Бывало ли у вас такое, что приходилось писать дипломную работу в крайне ограниченные сроки? Это действительно требует огромной ответственности и напряженных усилий, но важно не опускать руки и продолжать активно заниматься учебными процессами, чем я и занимаюсь.
Для тех, кто умеет искать и анализировать информацию в интернете, это действительно облегчает процесс согласования и написания дипломной работы. Не нужно тратить время на посещение библиотек или устраивать встречи с дипломным руководителем. Здесь, на этом ресурсе, предоставлены надежные данные для заказа и написания дипломных и курсовых работ с гарантией качества и доставкой по России. Можете ознакомиться с предложениями по ссылке купить диплом в Москве, это проверено!
https://comunidadeqm.marcelodoi.com.br/index.php?action=profile;u=611535
купить диплом цена
купить диплом бакалавра
купить диплом о среднем специальном
купить диплом специалиста
купить диплом нового образца
Желаю всем прекрасных отметок!
Известняковый щебень: применение и разнообразие сортов
Привет всем!
Были ли у вас случаи, когда вам приходилось писать дипломную работу в сжатые сроки? Это действительно требует большой ответственности и усилий, но важно не сдаваться и продолжать активно заниматься учебными процессами, как я.
Для тех, кто умеет эффективно искать информацию в интернете, это действительно облегчает процесс согласования и написания дипломной работы. Больше не нужно тратить время на посещение библиотек или организацию встреч с дипломным руководителем. Здесь, на этом ресурсе, предоставлены надежные данные для заказа и написания дипломных и курсовых работ с гарантией качества и доставкой по всей России. Можете ознакомиться с предложениями на купить аттестат школы, это проверенный источник!
http://alternativaprofi.com/forum/viewthread.php?thread_id=32316
купить диплом цена
купить диплом
купить диплом университета
купить диплом о высшем образовании
купить диплом техникума
Желаю любому пятерошных) оценок!
PBN sites
We’ll build a system of privately-owned blog network sites!
Benefits of our privately-owned blog network:
We perform everything so google DOES NOT grasp that this is A self-owned blog network!!!
1- We acquire web domains from various registrars
2- The principal site is hosted on a virtual private server (Virtual Private Server is fast hosting)
3- The remaining sites are on various hostings
4- We designate a unique Google ID to each site with confirmation in Search Console.
5- We design websites on WP, we do not utilise plugins with assisted by which malware penetrate and through which pages on your websites are generated.
6- We never repeat templates and utilize only unique text and pictures
We refrain from work with website design; the client, if desired, can then edit the websites to suit his wishes
Экологически чистые материалы в строительстве: забота о природе и здоровье
Ремонт тепловизоров в Москве: профессиональный сервис для вашей техники